Network attack path analysis method based on incidence matrixes
A correlation matrix and path analysis technology, applied in data exchange networks, digital transmission systems, electrical components, etc., can solve problems that cannot be applied to large-scale networks and cannot guarantee network security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] The present invention will be described in further detail below in conjunction with the accompanying drawings.
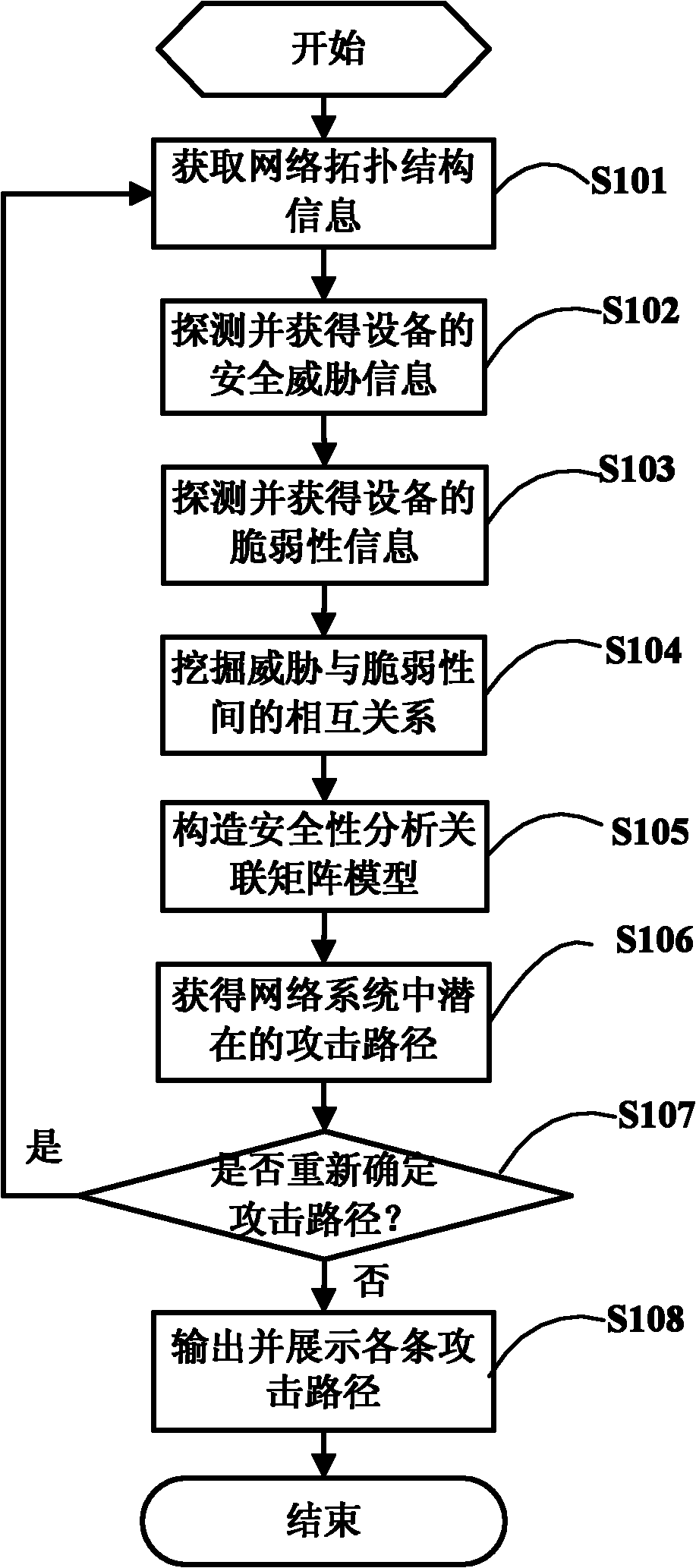
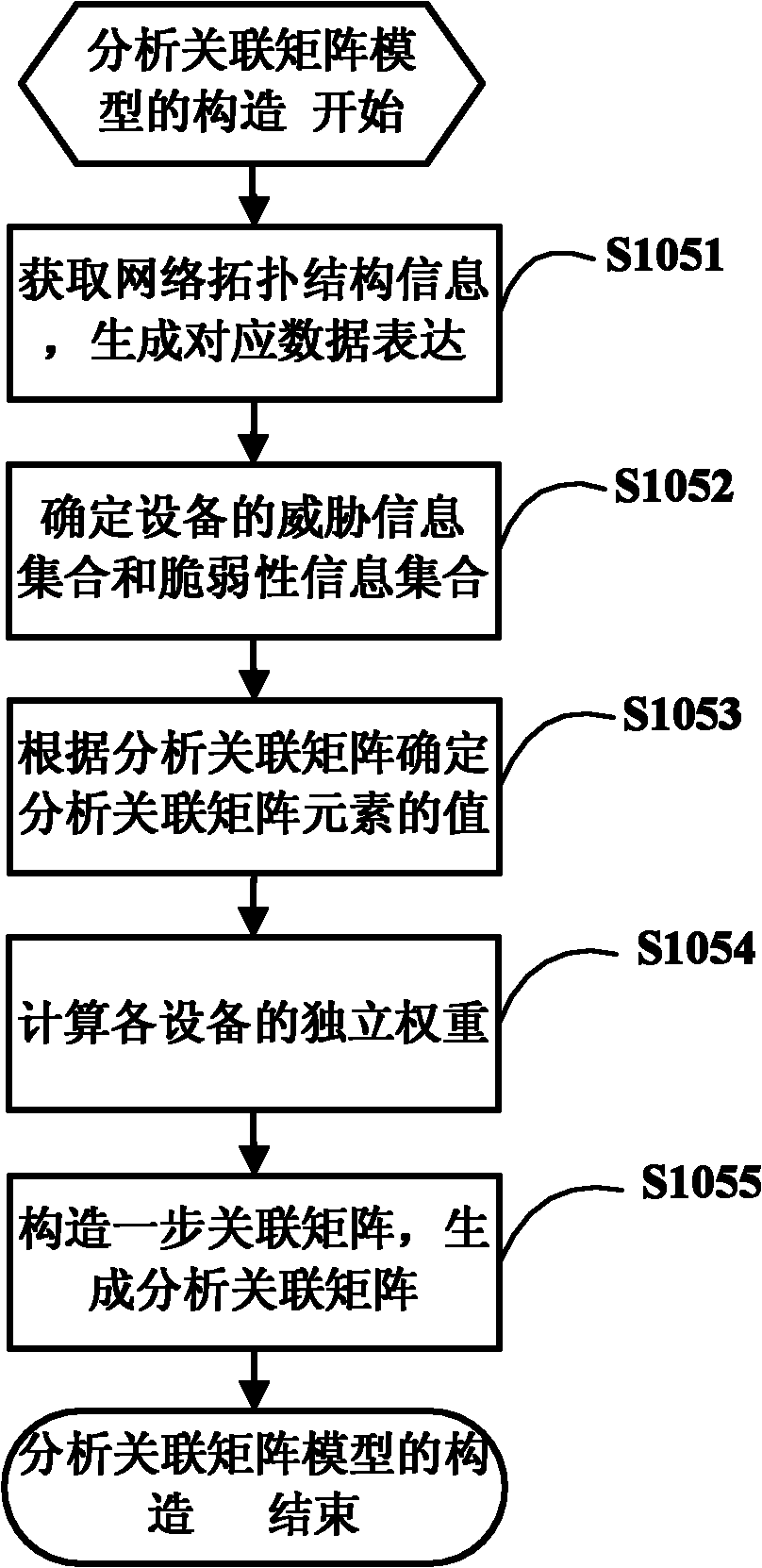
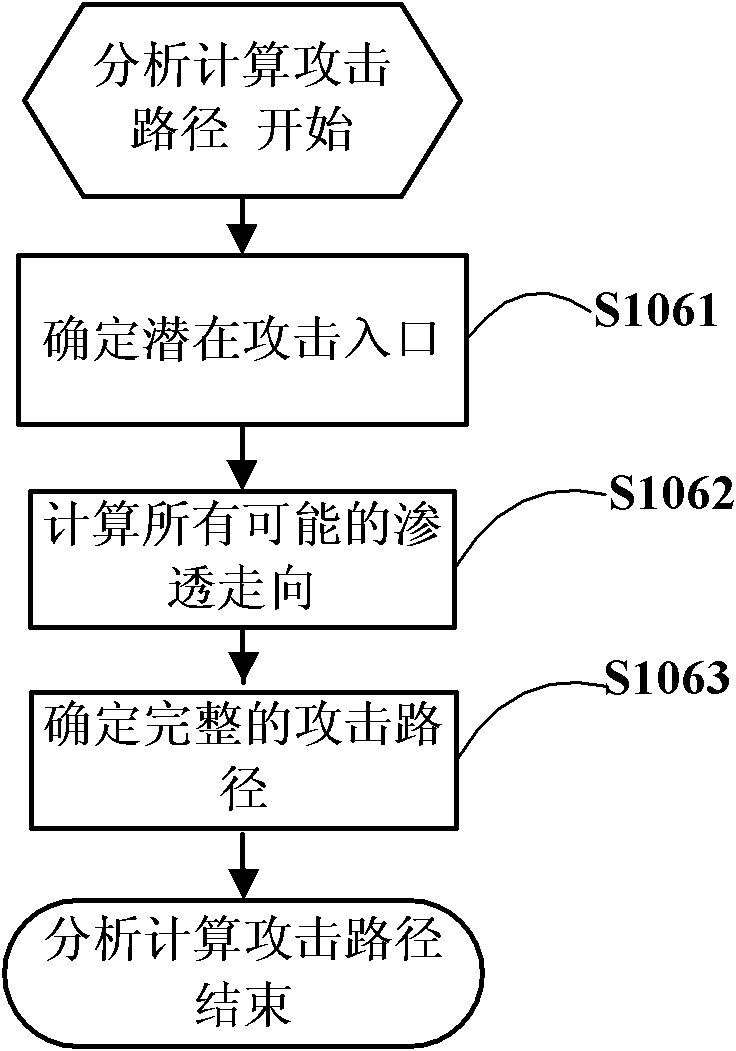
[0048] figure 1 It is an overall flow chart of the correlation matrix-based network attack path analysis method of the present invention.
[0049] pass below figure 1 The network attack path analysis method based on the correlation matrix of the present invention is described in detail.
[0050] Step S101, acquiring network topology information.
[0051] Generate a network topology structure based on automatic topology discovery and manual topology editing, and convert the information of the network topology structure into a data table.
[0052] If there are devices A and B in the network system, their structural information can be expressed as a function C, if A and B are physically related, then C(A, B)=1, otherwise, C(A, B)=0.
[0053] Step S102, detecting and obtaining device security threat information based on a single network device.
[0054] By a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More