Authentication method, device, authentication center and system
An authentication method and an authentication device technology, applied in the field of communication, can solve the problems of inapplicability to the Internet of Things, reduce the availability of Internet of Things services, etc., and achieve the effect of improving the usability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] The preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
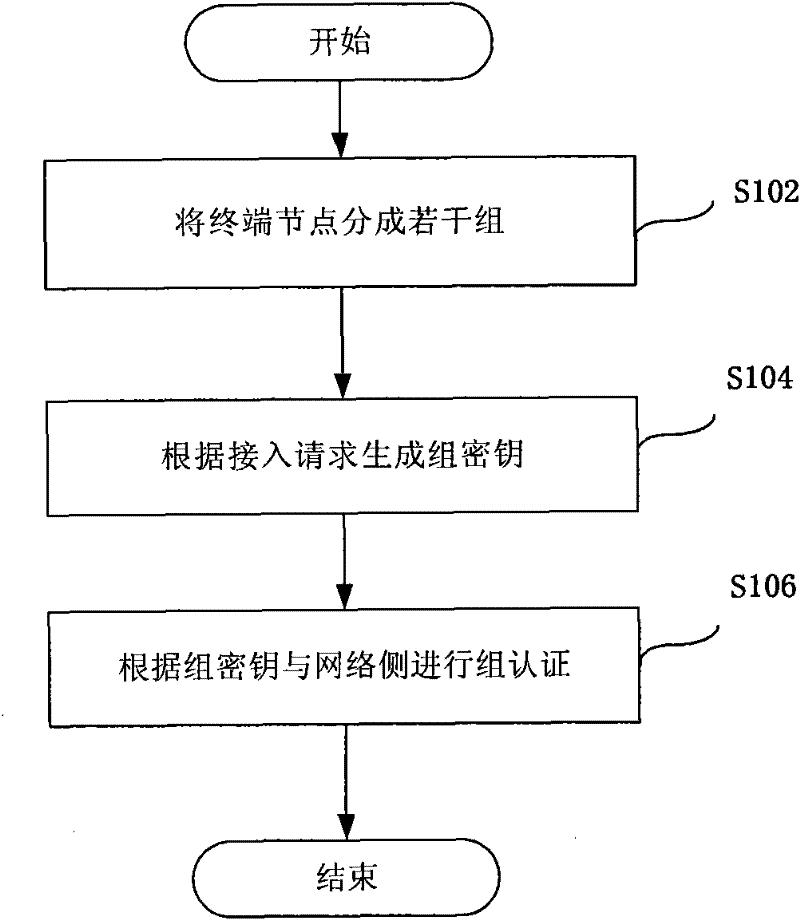
[0043] method embodiment
[0044] figure 2 It is a flow chart of Embodiment 1 of the authentication method according to the present invention, such as figure 2 As shown, this embodiment includes:
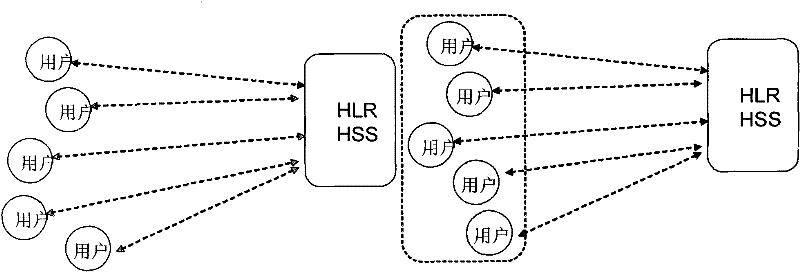
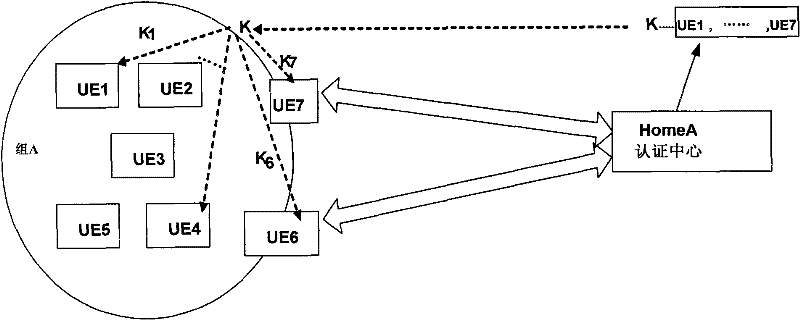
[0045]Step S102: The network side preliminarily forms a group of terminal nodes with the same behavior characteristics / behavior capabilities in the Internet of Things, specifically, for example, monitoring devices with shooting and capture characteristics form the same group; and save information in different groups , such as information such as the group, the nodes in the group, and the group key for authentication of the group, at least one representative node can b...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More