Method and system for detecting file stealing Trojan based on thread behavior
A file detection and thread technology
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
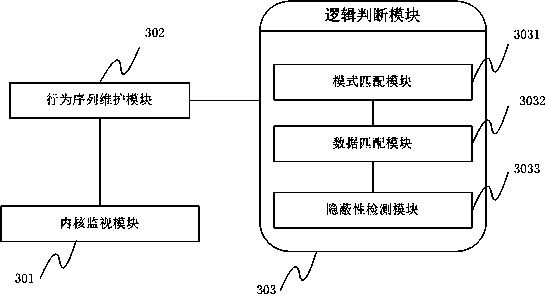
[0043] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
[0044] The invention provides a method and system for detecting files stolen by a Trojan horse based on thread behavior. The method and system greatly reduce false positives for normal file transmission and improve the detection of files stolen by a Trojan horse.
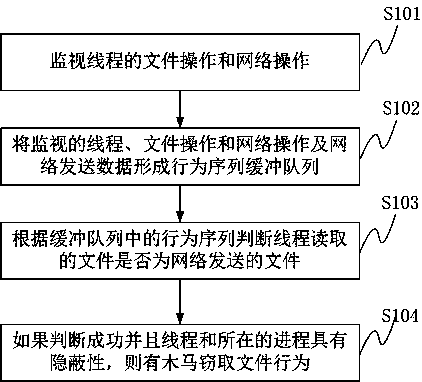
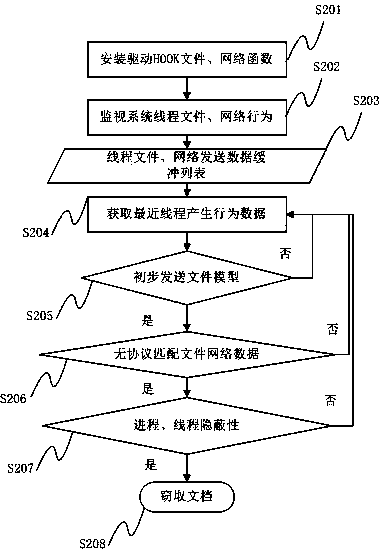
[0045] First introduce a kind of Trojan stealing file detection method based on thread behavior that the present invention provides, concrete implementation steps are as follows figure 1 shown, including:
[0046] S101, monitor the file operation and network operation of the thread; the file operation includes openi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More