Processing method of communication terminal after being stolen and communication terminal
A communication terminal and processing method technology, applied in the field of communication terminals, can solve the problems of inability to obtain the physical characteristics of thieves, unfavorable for police to solve cases, inconvenience in actual use, etc., and achieve the effects of protecting security, improving security, and avoiding deletion or destruction.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
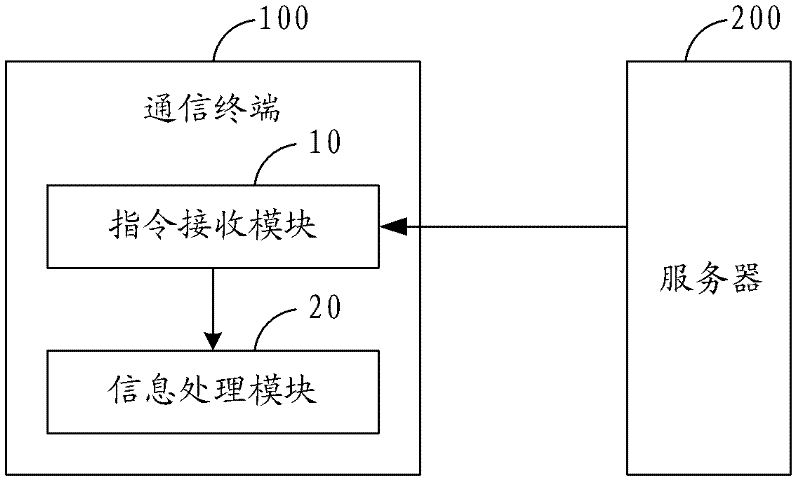
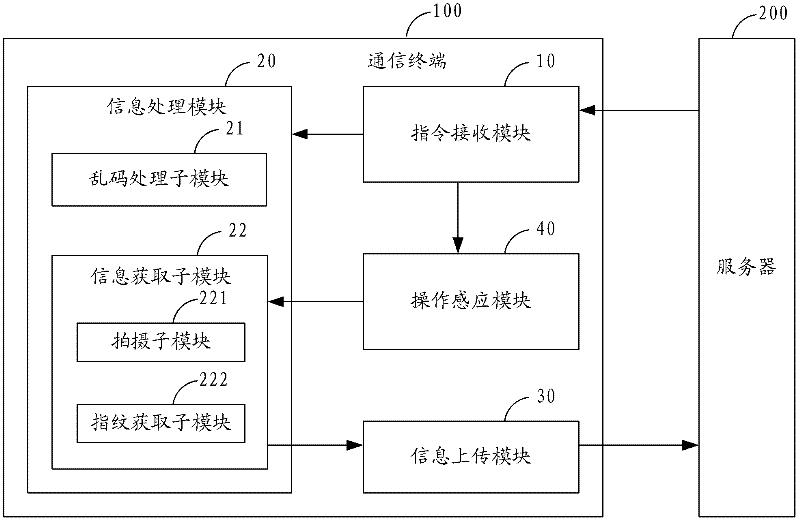
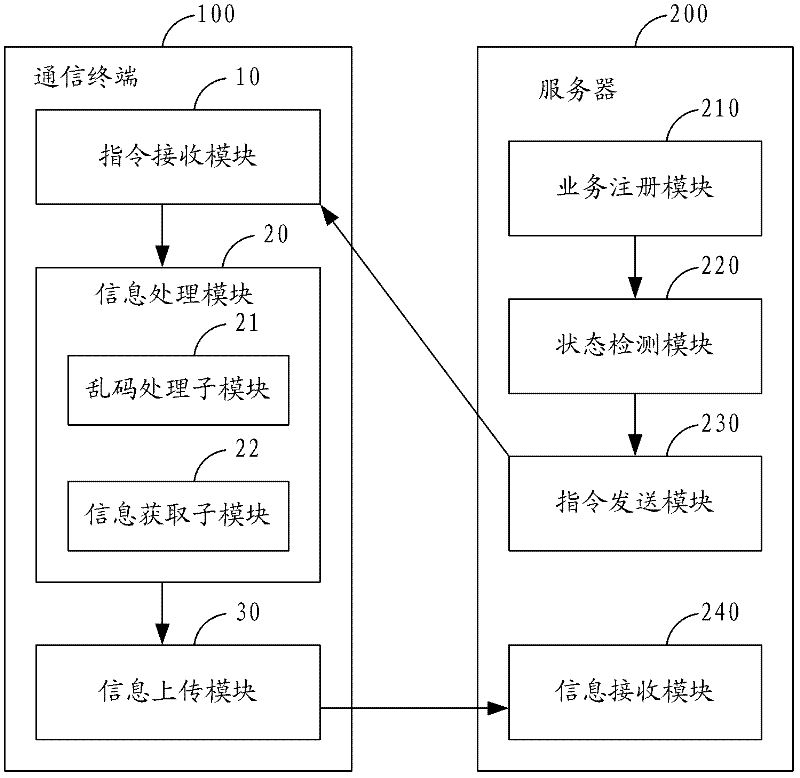
[0044] figure 1 The structure of the communication terminal of the present invention is shown, and the communication terminal 100 can be a mobile phone, a PDA (Personal Digital Assistant, a personal digital assistant), a palmtop computer, etc., and at least includes an instruction receiving module 10 and an information processing module 20, wherein:
[0045] The instruction receiving module 10 is configured to receive the anti-theft processing instruction sent by the server 200 . When the user's communication terminal 100 is stolen, the user may operate through a client such as a web (page) client...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More