Certificate-free remote anonymous authentication method for wireless body area network
A wireless body area network and anonymous authentication technology, applied in the field of certificateless remote anonymous authentication, which can solve the problems of high computational complexity and inability to achieve anonymity.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
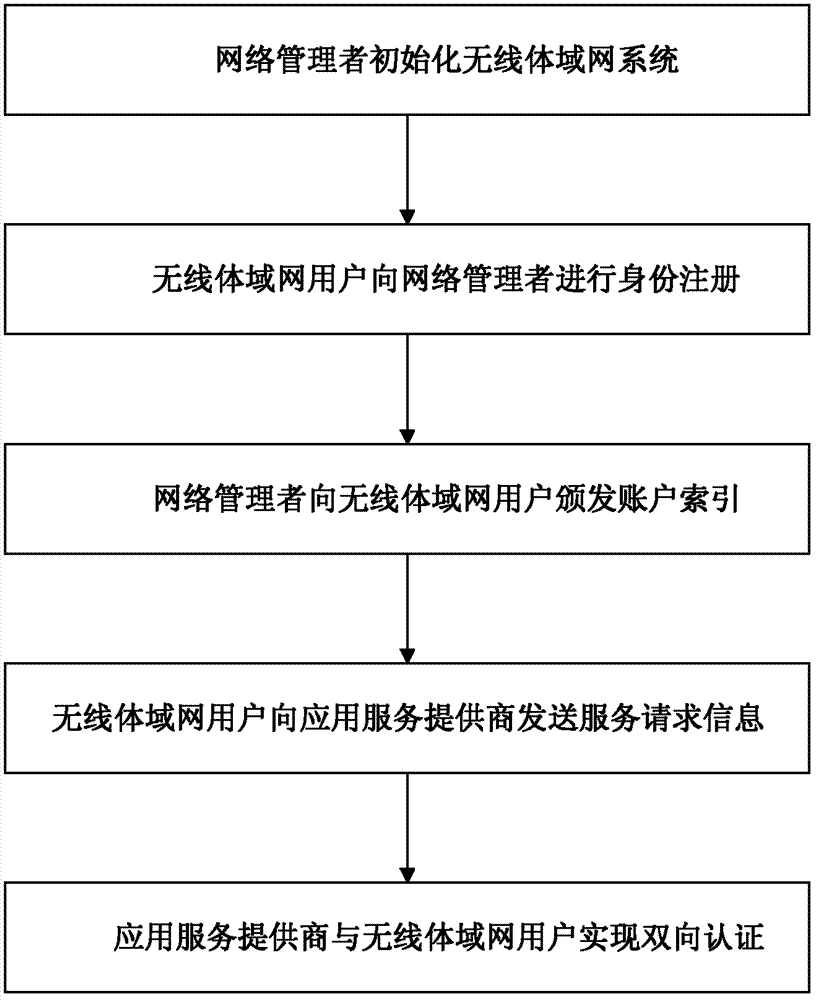
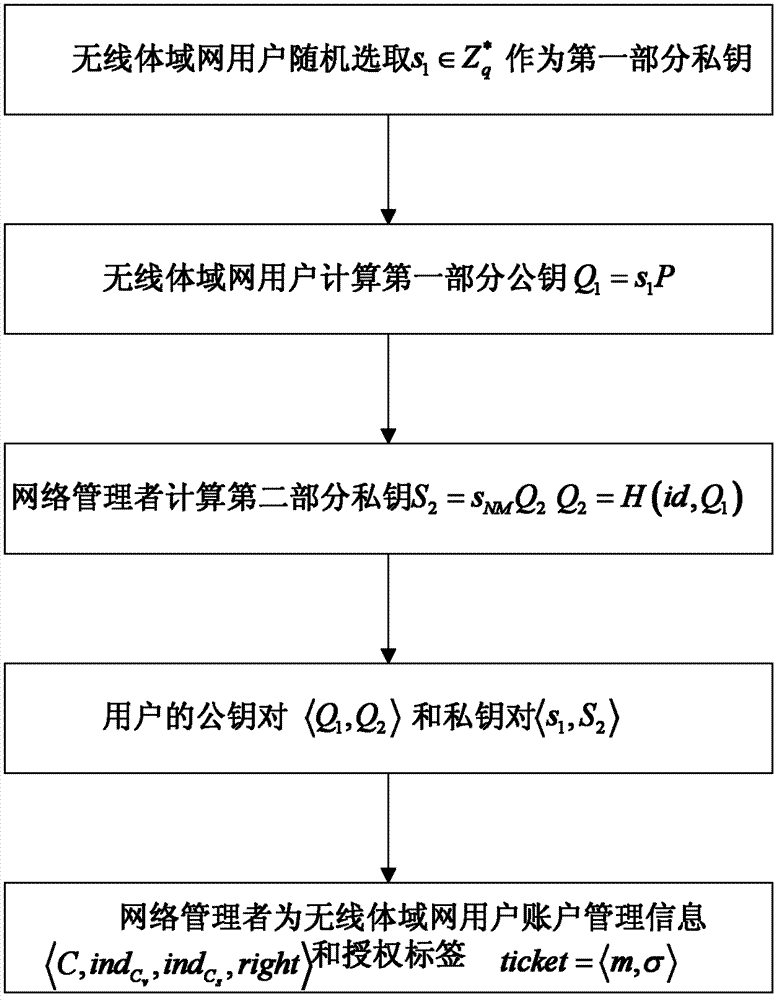
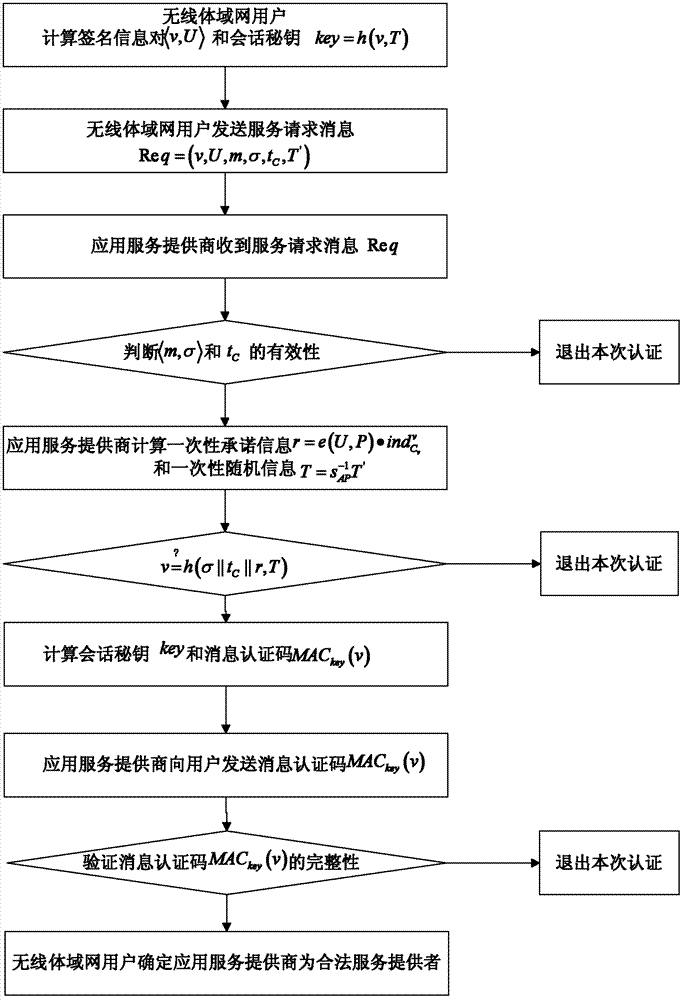
[0043] refer to figure 1 , the implementation steps of the present invention are as follows:
[0044] Step 1, initialization:
[0045] (1a) The network manager determines the size of the safety factor l and the prime number q according to the safety requirements, and uses the elliptic curve to construct the bilinear map e(G 1 , G 2 ) → G 2 The cyclic addition group G of 1 and the cyclic multiplicative group G 2 ;
[0046] (1b) The network manager chooses the following collision-free hash function H: {0, 1) * ×G 1 →G 1 and where H is a 0 / 1 sequence of varying lengths and G 1 Elements in G are mapped to G 1 The hash function of the elements above, h is the 0 / 1 sequence of different lengths and G 1 The elements in are mapped to the integer multiplicative group of modq The hash function of the above elements;
[0047] (1c) The network manager starts from the integer multiplication group Randomly choose an integer s from NM As its own private key and stored, calc...
Embodiment 2
[0064] refer to figure 1 , the implementation steps of the present invention are as follows:
[0065] Step A, initialization:
[0066] (A1) The network manager determines the size of the safety factor l and the prime number q according to the safety requirements, and uses the elliptic curve to construct the bilinear map e(G 1 , G 2 ) → G 2 The cyclic addition group G of 1 and the cyclic multiplicative group G 2 ;
[0067] (A2) The network manager chooses the following collision-free hash function H: {0, 1} * ×G 1 →G 1 and where H is a 0 / 1 sequence of varying lengths and G 1 Elements in G are mapped to G 1 The hash function of the elements above, h is the 0 / 1 sequence of different lengths and G 1 The elements in are mapped to the integer multiplicative group of modq The hash function of the above elements;
[0068] (A3) Network managers start from the integer multiplication group Randomly choose an integer s from NM As its own private key and stored, calculat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More