Anonymous authentication algorithm for remote authentication between credible platforms
An anonymous authentication and remote attestation technology, applied in the field of information security, can solve problems such as complex calculation process, difficulty in realizing zero-knowledge authentication, and limited computing power
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] The present invention will be described in further detail below in combination with specific embodiments.
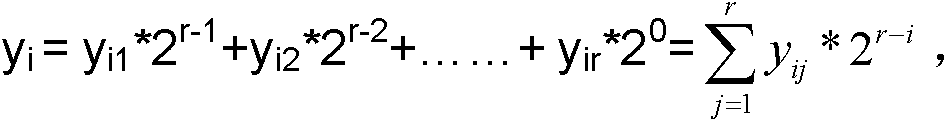
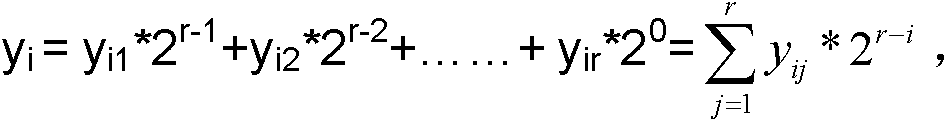
[0036] The present invention provides an anonymous authentication algorithm for remote certification of a trusted platform. This algorithm is based on the theoretical assumption of the public key encryption system RSA Assumption. Since the theoretical assumption of the public key encryption system is a well-known technology in the field of information security, it will not be described in detail. The present invention includes The following steps:
[0037] (1) Parameter initialization: The trusted platform involved in the verification of both parties selects two different large prime numbers PR 1 、PR 2 , set parameter n A =PR 1 PR 2 , e A =(PR 1 -1)(PR 2 -1), set the public parameter g A , g A for not more than n A A positive integer of , at the same time through the key generator of the trusted platform and the parameter e A Generate a public-private k...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More