Method, system and terminal device for processing WLAN authentication and privacy infrastructure (WAPI) certificate
A technology for terminal equipment and certificates, applied in electrical components, wireless communication, security devices, etc., can solve the problems of high security, inability to implement WAPI certificates, etc., and achieve the effect of improving security and ensuring security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
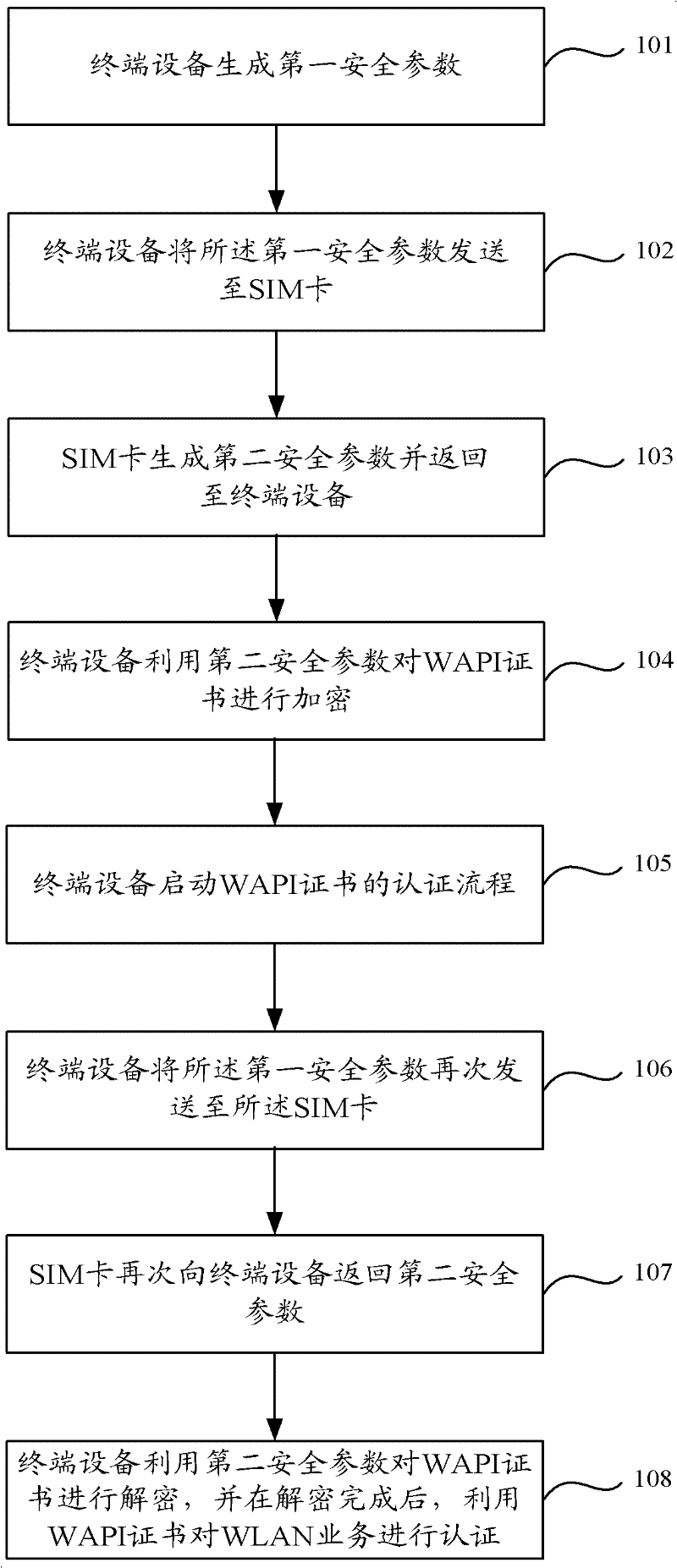
[0035] Embodiment 1 of the present invention provides a method for processing WAPI certificates, the step flow chart of the method is as follows figure 1 As shown, it specifically includes the following steps:
[0036] Step 101, the terminal device generates a first security parameter.
[0037] The first security parameter is generated randomly or according to a set rule each time the terminal device needs to encrypt the WAPI certificate.
[0038] Specifically, in order to facilitate the subsequent user identification module to generate the second security parameter according to the first security parameter, the format of the first security parameter may be an array of 128*N bits, where N is an integer greater than or equal to 1.
[0039] In this step, the generated first security parameter needs to be saved for subsequent decryption of the WAPI certificate.
[0040] Described user identification module can be SIM card, UIM (User Identity Module) card or USIM (Universal Subs...
Embodiment 2
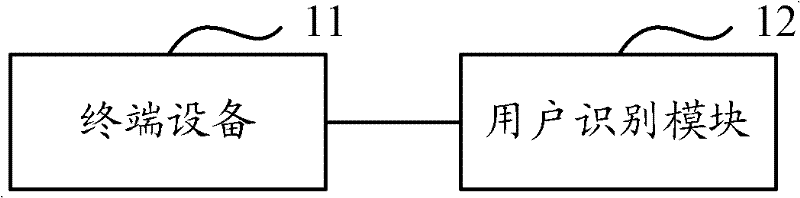
[0073] Embodiment 2 of the present invention provides a system for processing WAPI certificates. The structural diagram of the system is as follows figure 2 As shown, the system includes a terminal device 11 and a subscriber identification module 12, wherein:
[0074] The terminal device 11 is used to generate the first security parameter, and send the first security parameter to its own user identification module, and use the second security parameter returned by the user identification module to encrypt the stored WAPI certificate; user identification The module 12 is configured to use the first security parameter to generate the second security parameter and return it to the terminal device.
[0075] The terminal device 11 is further configured to send the first security parameter to the subscriber identification module again when it is necessary to use the WAPI certificate to authenticate the WLAN service, and use the second security parameter returned by the subscriber i...
Embodiment 3
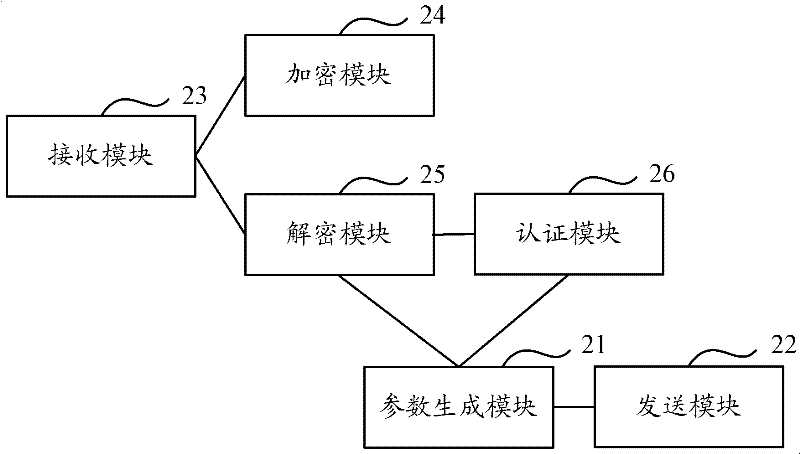
[0080] Embodiment 3 of the present invention provides a terminal device. The schematic structural diagram of the terminal device is as follows image 3 As shown, the terminal device includes a parameter generation module 21, a sending module 22, a receiving module 23 and an encryption module 24, wherein:
[0081] The parameter generating module 21 is used to generate a first security parameter; the sending module 22 is used to send the first security parameter to the subscriber identification module of the terminal device; the receiving module 23 is used to receive the second security parameter returned by the subscriber identification module ; The encryption module 24 is used to encrypt the stored WAPI certificate by using the second security parameter.
[0082] The terminal device also includes a decryption module 25 and an authentication module 26:
[0083] The sending module 22 is further configured to send the first security parameter to the subscriber identification mod...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More