Application program security verification method and terminal
An application and security verification technology, applied in the direction of digital data authentication, electrical components, transmission systems, etc., can solve problems such as misleading users and high security risks, and achieve the effect of ensuring security and improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
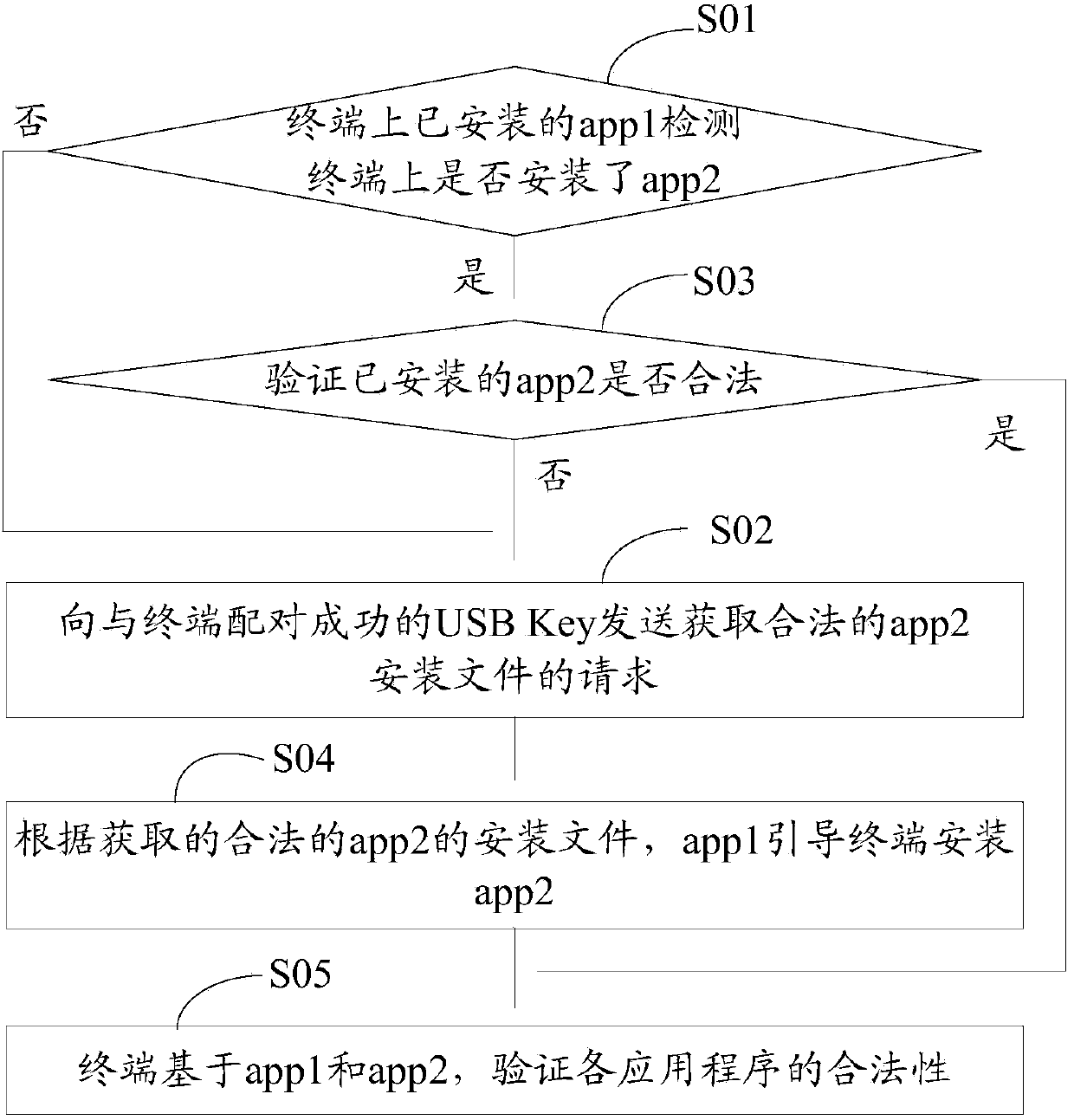
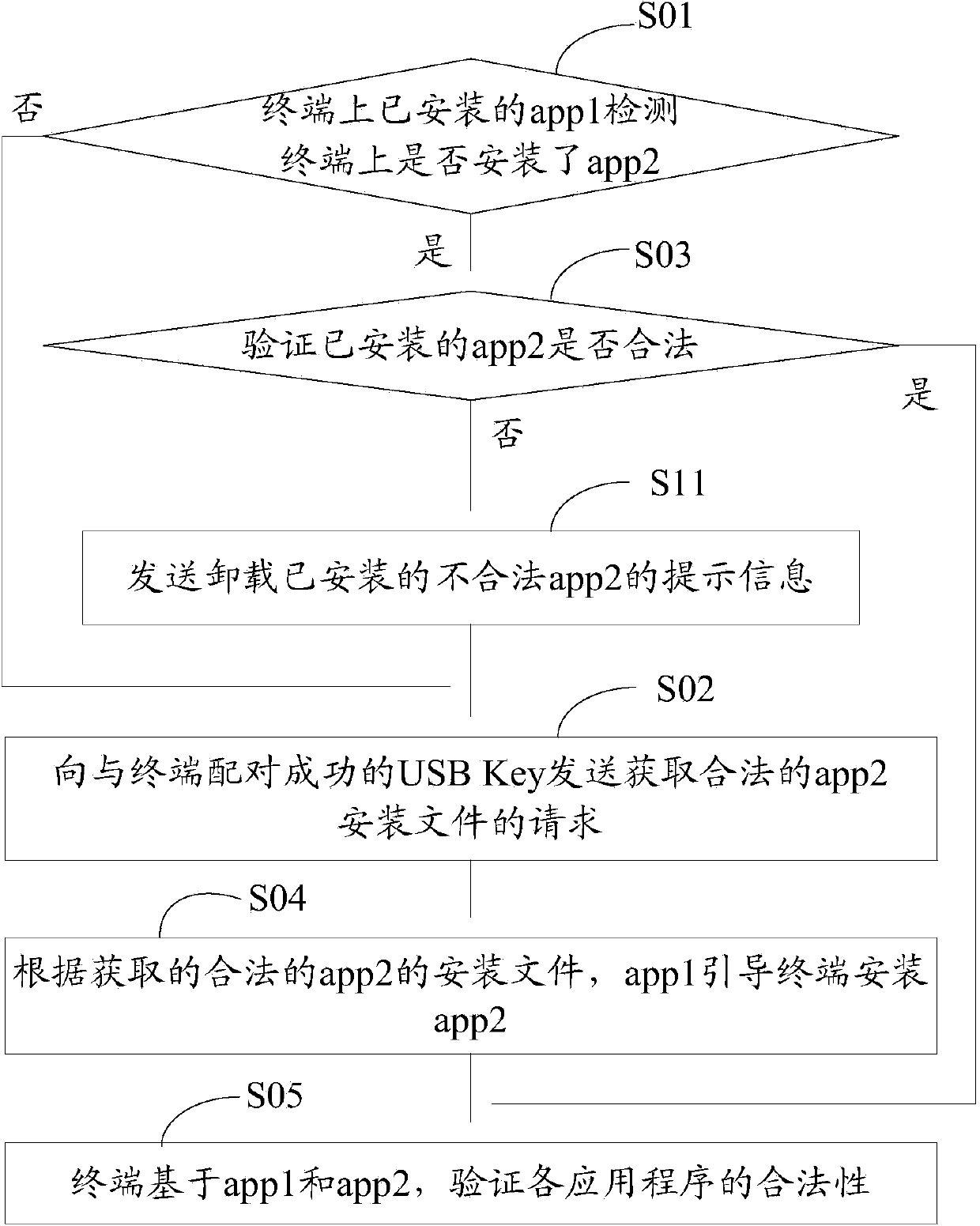
[0046] The technical solutions of the present invention will be further described below in conjunction with the accompanying drawings and specific embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
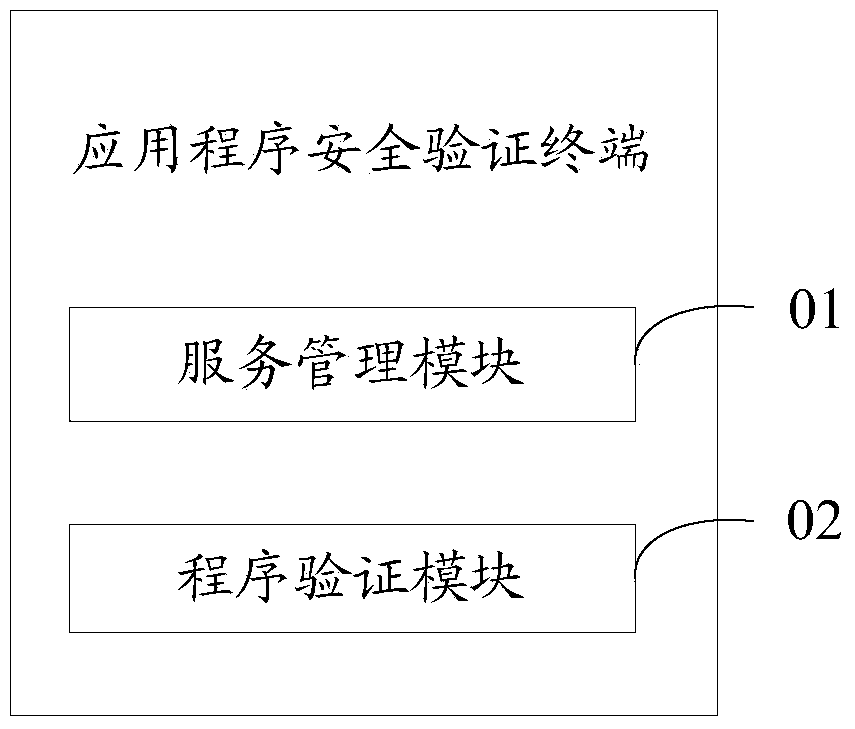
[0047] In the embodiment of the application program security verification method and terminal of the present invention, the second-generation USB Key is used as the security basis of the terminal app (Application, application program), and the built-in first reliable app (that is, the aforementioned The service management program, which will be referred to as app1 for the convenience of description, downloads, verifies, and manages other apps on the verification terminal through app1. When the USB Key and the terminal are not bound, the USB Key cannot be used; and after the USB Key is successfully paired with the terminal, the terminal must first install the built-in ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More