Method for realizing data security transmission, system, server and terminal
A data security and server technology, applied in the field of data security, can solve the problems of increasing user waiting time, long time, etc., and achieve the effect of reducing waiting time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
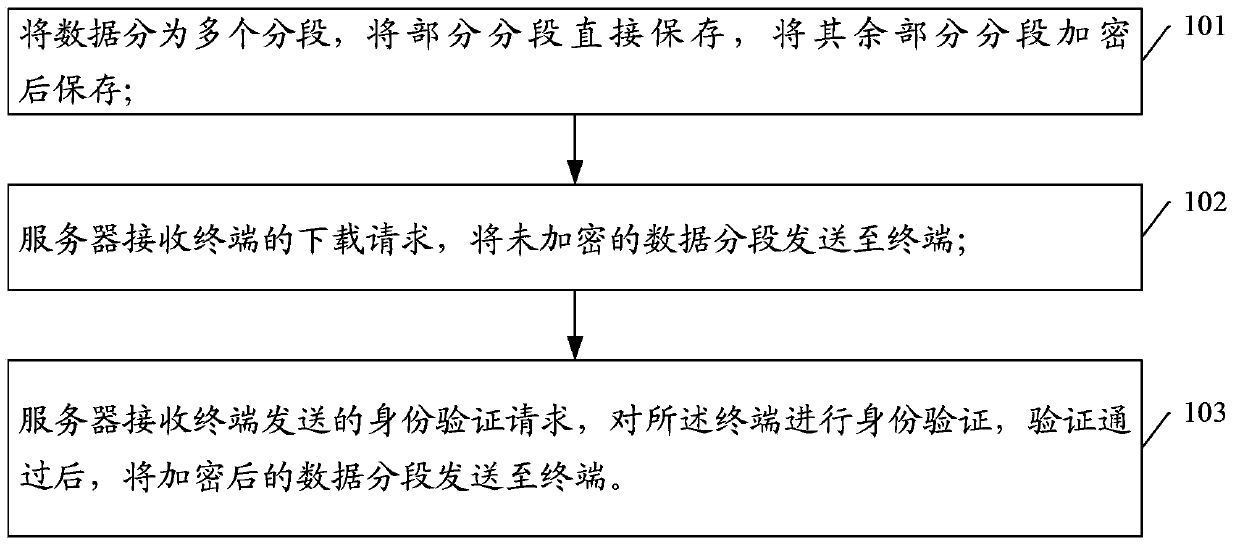
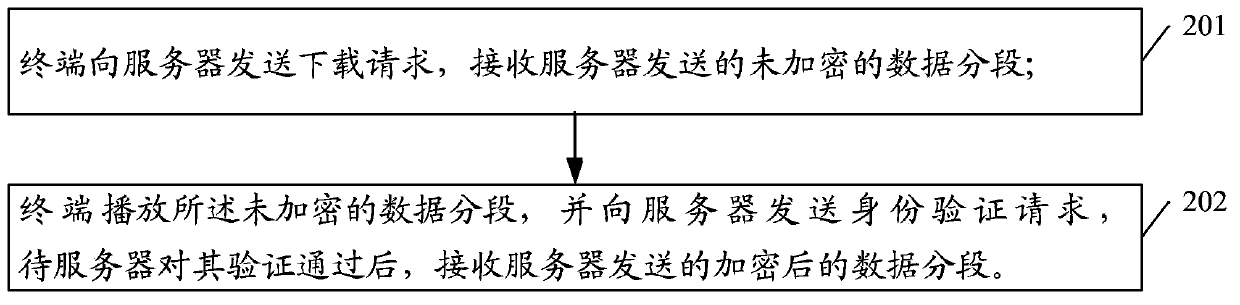
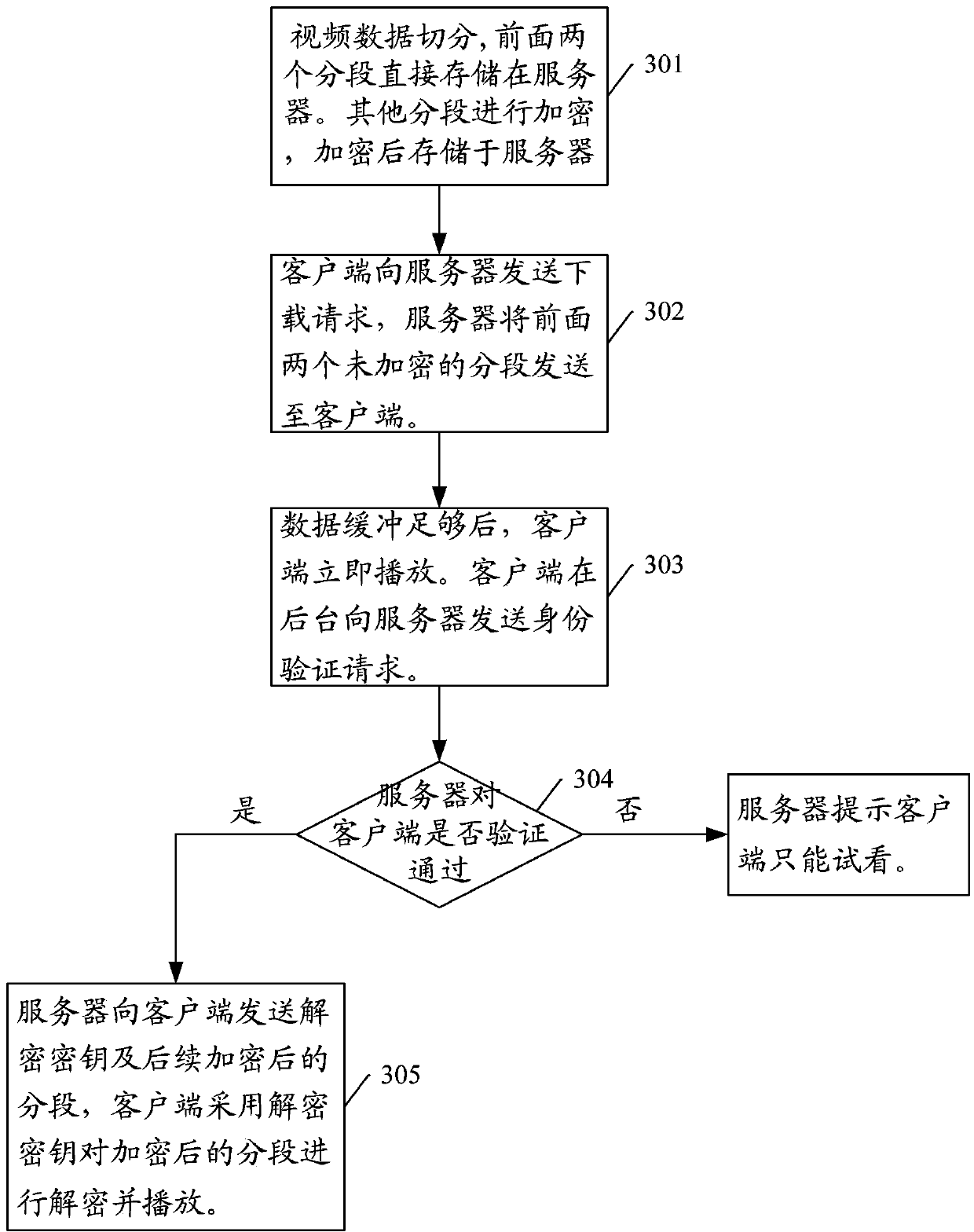
[0036] The present invention proposes a method for realizing secure data transmission, such as figure 1 A flowchart for the method proposed by the present invention, including:
[0037] Step 101: Divide the data into multiple segments, store some segments directly, and encrypt and store the rest of the segments;
[0038] Step 102: the server receives the download request from the terminal, and sends unencrypted data segments to the terminal;
[0039] Step 103: The server receives the identity verification request sent by the terminal, performs identity verification on the terminal, and sends encrypted data segments to the terminal after passing the verification.
[0040] In the above step 103, the terminal may send an identity verification request to the server while playing the unencrypted data segment.
[0041] If the authentication of the terminal by the server fails, an authentication failure message may be sent to the terminal.
[0042] In order to cope with the delay ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More