BMC security management method and system in a trusted computing server
A security management and trusted computing technology, applied in the field of computer security, to achieve the effect of improving security management performance and promoting the use value
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0014] The advantages and design content of the BMC security management method and system in the trusted computing server of the present invention will be described in detail below through an embodiment.
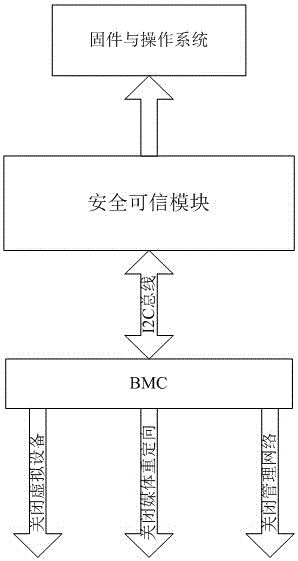
[0015] This embodiment is based on the domestic Loongson server as an example to illustrate the implementation process of realizing BMC security management, as attached figure 2 As shown, the secure trusted module detects and measures the BIOS and operating system, and formulates system security policies based on the BIOS and operating system. The secure trusted module communicates with the BMC (AST2400BMC chip) through the I2C bus, and sends management commands to the AST2400BMC chip. After the BMC receives the management command sent by the secure trusted module, it adjusts its own management functions and implements different management functions for different levels of security.
[0016] In this embodiment, the secure trusted module first formulates system security policies ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com