Disposable public key encryption structuring method based on fuzzy identity
A construction method, one-off technology, applied in the field of information security, which can solve the problems of inability to determine the identity of malicious users, deception, lack of traceability, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0056] The technical solution of the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
[0057] One, the detailed steps of the present invention
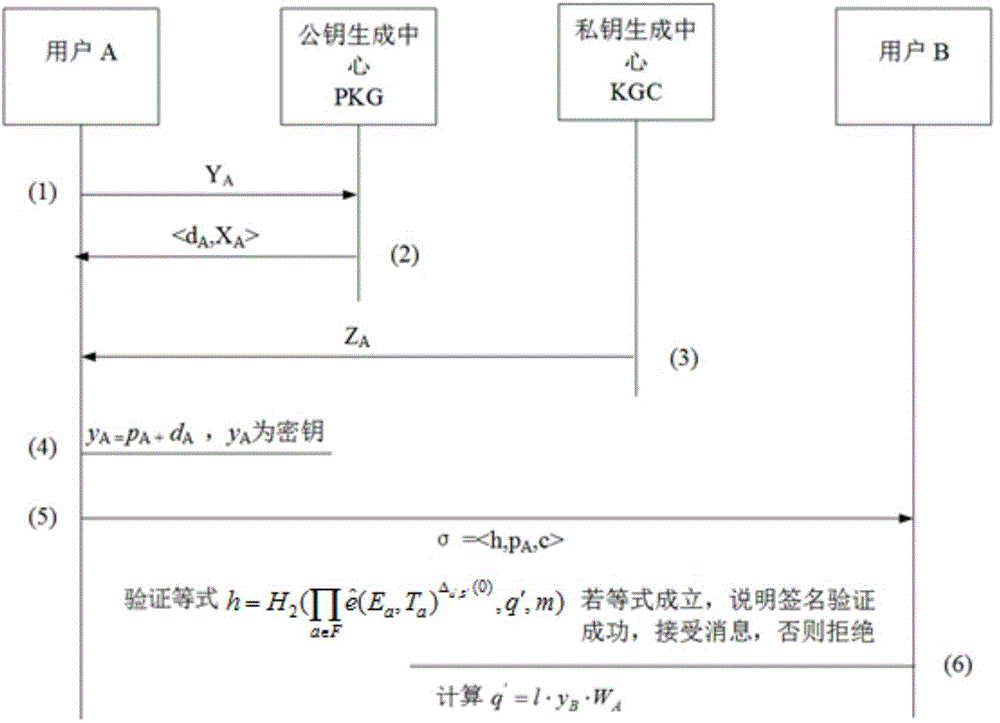
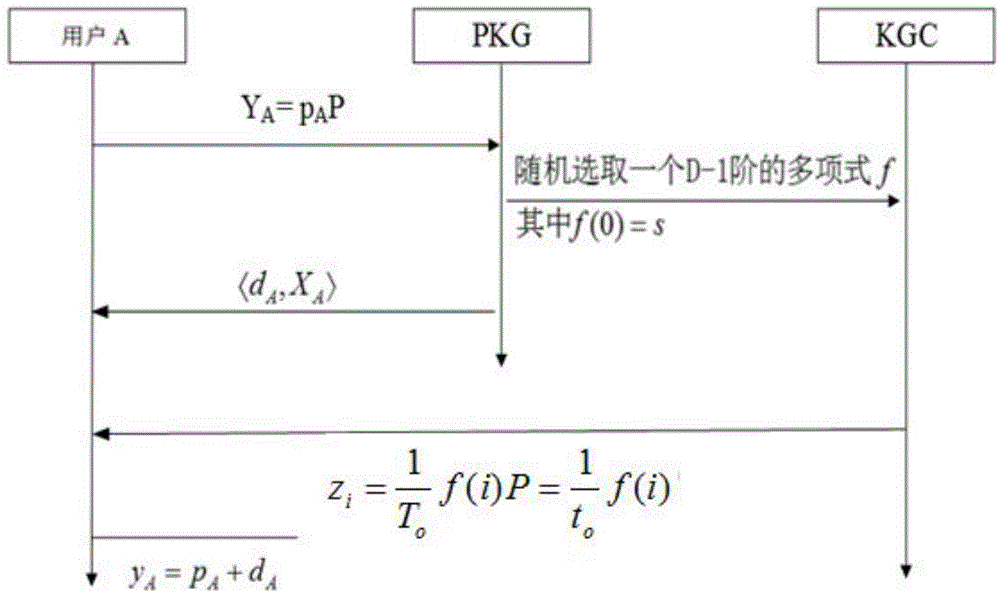
[0058] The method of the present invention uses a computer system to complete the construction of a one-time public key anonymous signcryption based on fuzzy identity. The computer system includes user A and user B who can communicate with each other, a public key generation center PKG and a private key generation center KGC; The method steps are as follows:
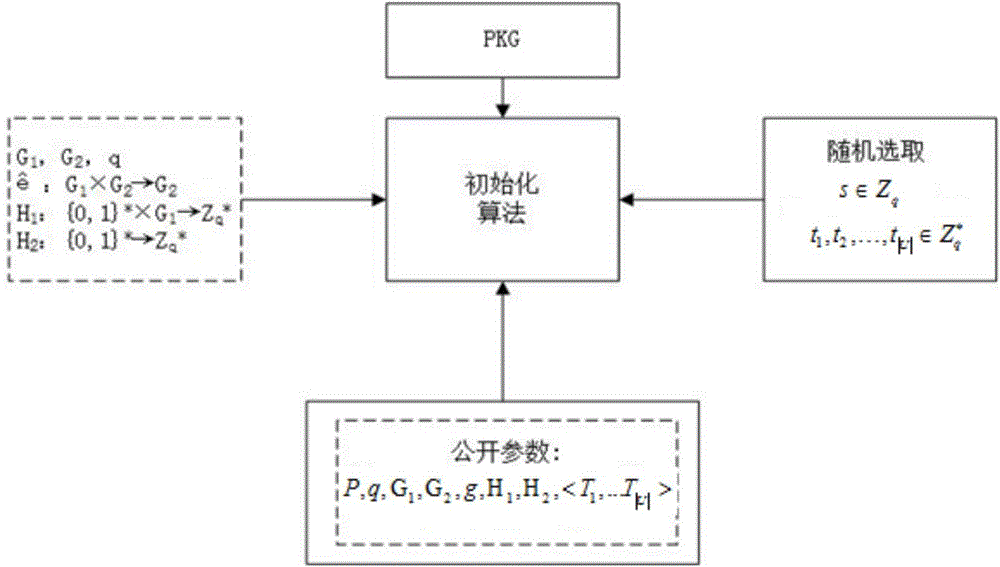
[0059] Step 1, system initialization
[0060] Step S10, such as figure 2 As shown, let P be a point on the elliptic curve, and the equation of the elliptic curve is: y 3 =x 3 +ax+b, a and b are constants; G 1 , G 2 are two groups generated by P, whose order is a prime number q; among them, G 1 is the cyclic addition group, G 2 is the cyclic multiplication group, in the group G 1 , G 2 ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More