Method and system for protecting desktop cloud service through access control
An access control, desktop cloud technology, applied in the desktop cloud security field, can solve the problems of easy guessing and brute force cracking, weak security strength, affecting system security, etc., to prevent unauthorized data flow and small changes.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] All features disclosed in this specification, or steps in all methods or processes disclosed, may be combined in any manner, except for mutually exclusive features and / or steps.
[0028] Any feature disclosed in this specification, unless specifically stated, can be replaced by other equivalent or similar purpose alternative features. That is, unless expressly stated otherwise, each feature is one example only of a series of equivalent or similar features.
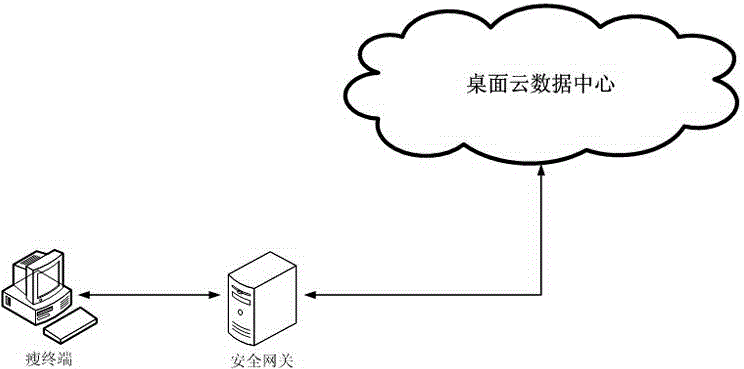
[0029] like figure 1 , connect the security gateway between the thin terminal and the desktop cloud data center, the security gateway provides two network ports, internal and external, the external network port is used to connect the thin terminal, and the internal network port is used to connect to the desktop cloud data center.
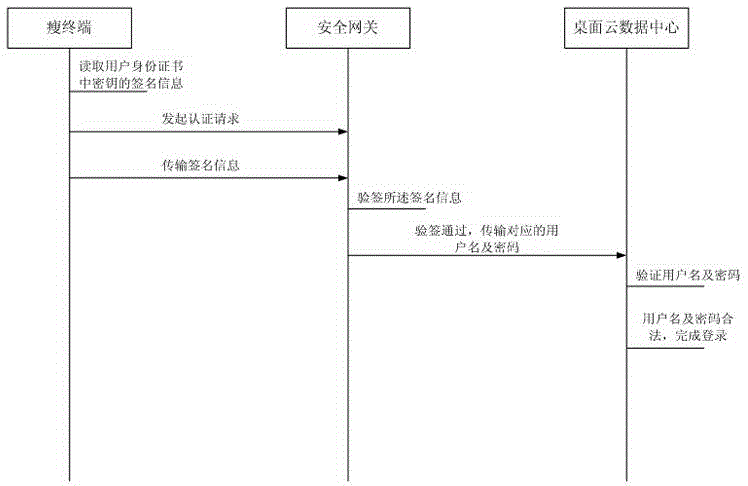
[0030] like figure 2 , the method disclosed in the present invention comprises:
[0031] Step 1: The thin terminal is connected to the desktop cloud data center through the security g...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More