Unstructured data protection method based on cloud storage technology
An unstructured data and unstructured technology, applied in electrical components, transmission systems, etc., can solve problems such as complex authority management, difficult implementation by enterprises, and difficult tracking
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The present invention will be described in detail below in conjunction with specific embodiments. The following examples will help those skilled in the art to further understand the present invention, but do not limit the present invention in any form. It should be noted that those skilled in the art can make several modifications and improvements without departing from the concept of the present invention. These all belong to the protection scope of the present invention.
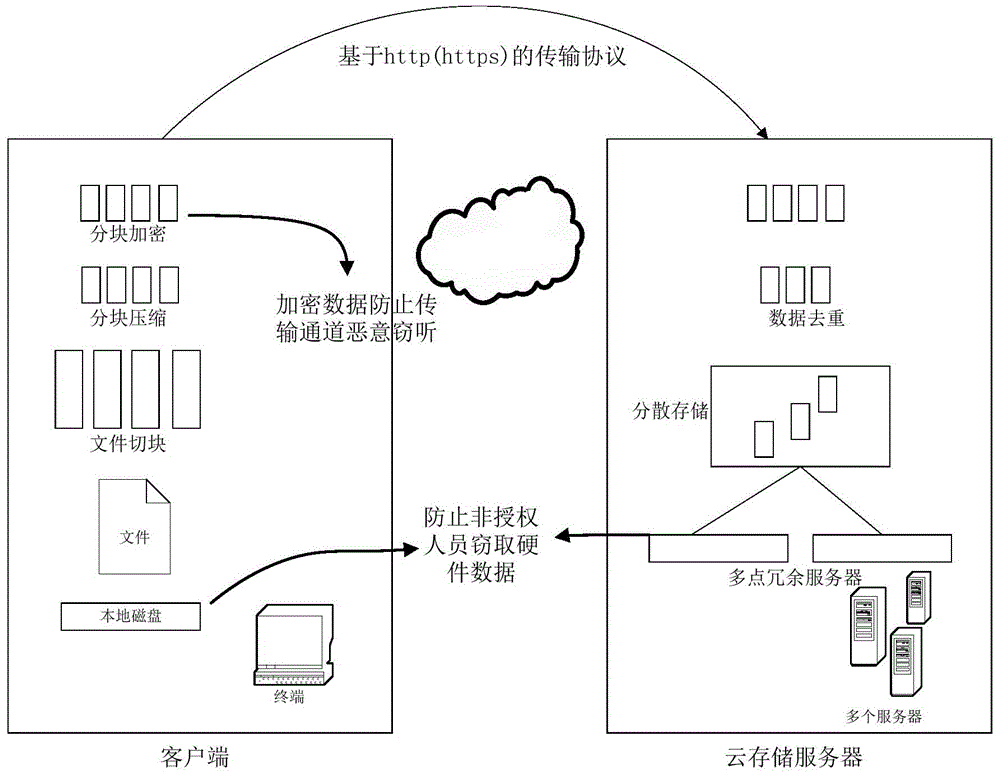
[0034] The present invention effectively links terminal security, data security, and cloud storage security, uses virtual mounting technology to generate secure disks on user terminals, and ensures that only legal personnel can create secure disks through compliant terminals, and through secure disks and cloud storage Perform real-time synchronization to provide full-cycle, full-process, and full-level protection for all protected unstructured data.
[0035] The unstructured data protection method...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More