Authentication method of RFID tag and back-end database based on lightweight function set
A technology of RFID tags and databases, applied in the field of authentication of RFID tags and back-end databases, can solve problems such as increasing the probability of attackers cracking the key
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
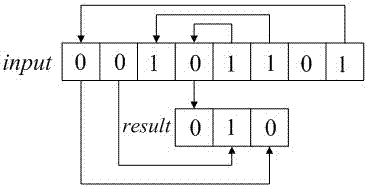
[0042] The present invention will be described in detail below in conjunction with the accompanying drawings.
[0043] 1. Initialization phase
[0044] When the label is produced, several lightweight functions are written in its internal memory, and these functions constitute the lightweight function set F={f 1 , f 2 ,..., f i ,..., f n}. Among them, any lightweight function f i At least the following conditions should be met:
[0045] The input can be a message of any length;
[0046] The same input results in the same output information;
[0047] The output obtained by different input is also different;
[0048] In the case of the same amount of input information, the calculation amount of the lightweight function is not higher than that of the symmetric key encryption algorithm, such as the AES algorithm with a key length of 128 bits;
[0049] The input of the function contains at least one secret value known only to the communicating parties;
[0050] Even if the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More