Access controlling method and access controlling device
A technology of access control and access method, applied in the field of communication, can solve problems such as inconvenience of operation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
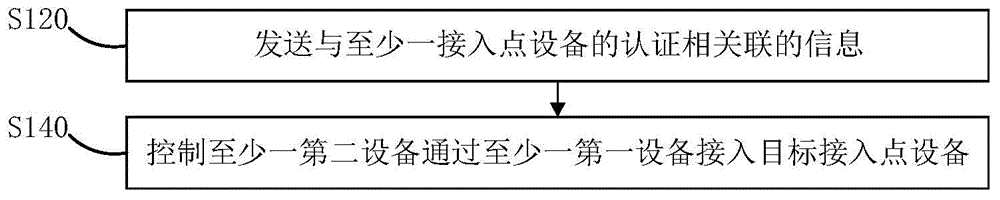
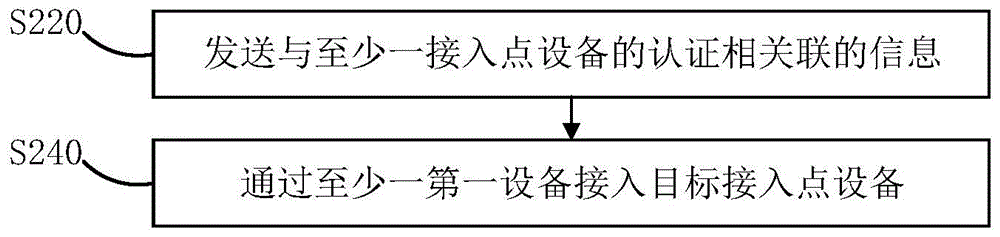
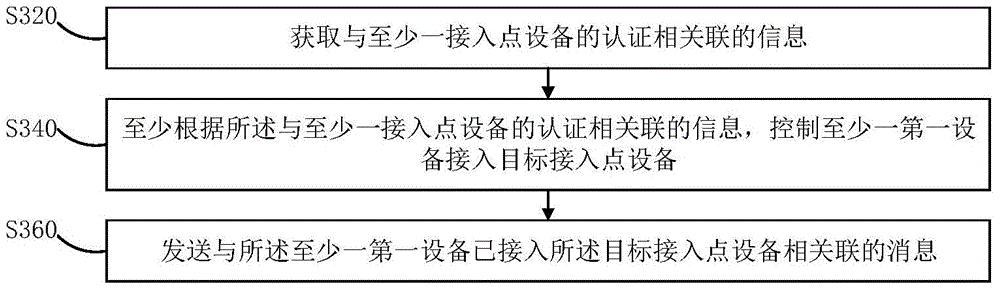
Method used
Image
Examples
Embodiment Construction
[0179] The specific implementation manners of the present invention will be described in further detail below in conjunction with the accompanying drawings and examples. The following examples are used to illustrate the present invention, but are not intended to limit the scope of the present invention.
[0180] Those skilled in the art can understand that terms such as "first" and "second" in this application are only used to distinguish different devices, modules or parameters, etc., neither represent any specific technical meaning, nor represent the inevitable relationship between them. logical order.
[0181]Generally, when a user expects to access a wireless local area network through an access point device, he needs to pass the authentication of the access point device, and such authentication may require the participation of other devices. For example, under the authentication method of SMS verification code, the user needs to enter the mobile phone number on the curre...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More