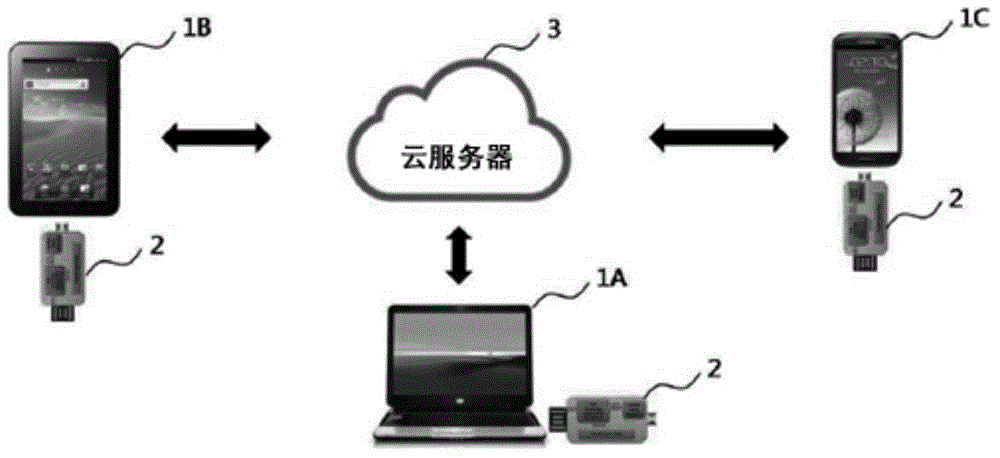
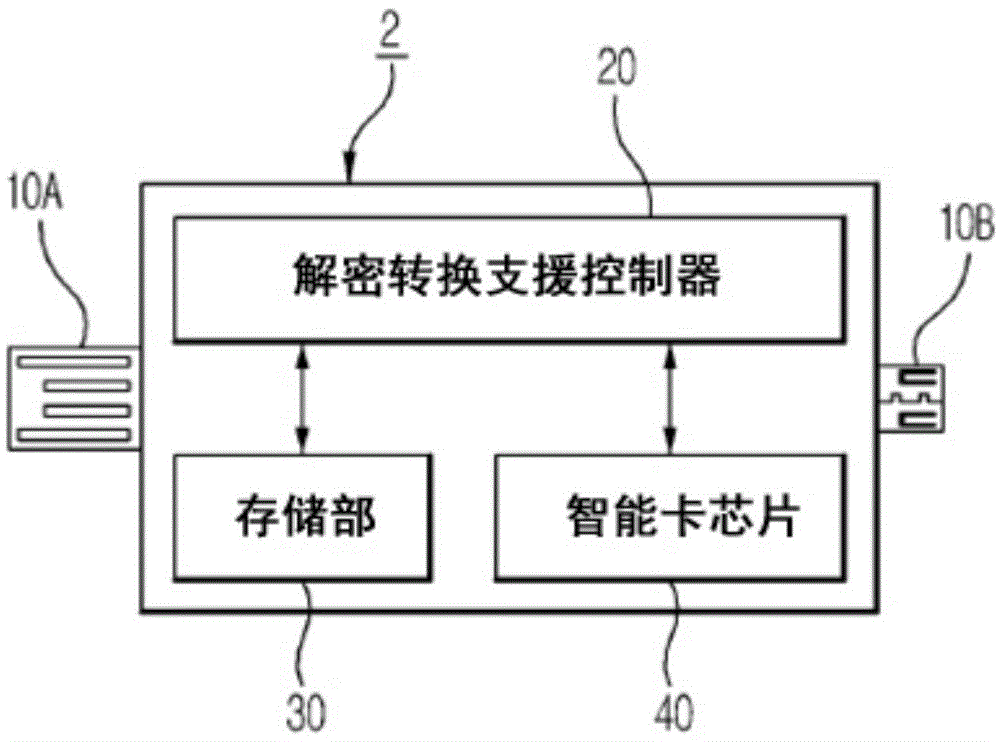
Security key device for secure cloud services, and system and method of providing security cloud services
A technology of dynamic password cards and cloud services, applied in transmission systems, computer security devices, instruments, etc., to prevent leakage and improve security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
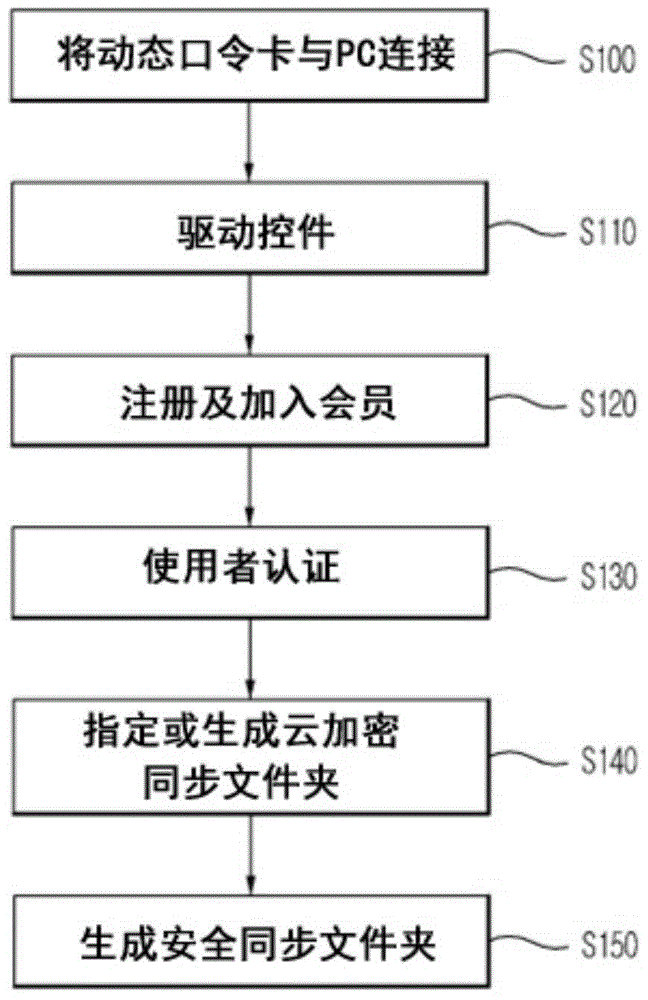
Method used
Image
Examples
Embodiment Construction
[0031] The description of the invention is merely an example for explaining the structure and function, and the scope of rights of the present invention should not be construed as being limited to the example described herein. That is, the embodiment can be changed variously and can have various forms, so it should be understood that the scope of rights of the present invention includes equivalents capable of realizing technical ideas. Moreover, the objects or effects proposed in the present invention do not mean that a specific embodiment must include all of the above objects or effects, or only include the above effects, and therefore, the scope of rights of the present invention cannot be limited thereto.
[0032] And, the meaning of the terms used in this application should be understood with reference to the following description.
[0033] Terms such as "first" and "second" are used to distinguish one constituent element from other constituent elements, and the scope of r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More