Resource push method and resource push device
A resource and resource sub-technology, applied in the field of resource push methods and devices, can solve problems such as high pressure on resource servers, and achieve the effect of solving excessive pressure and reducing processing pressure
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
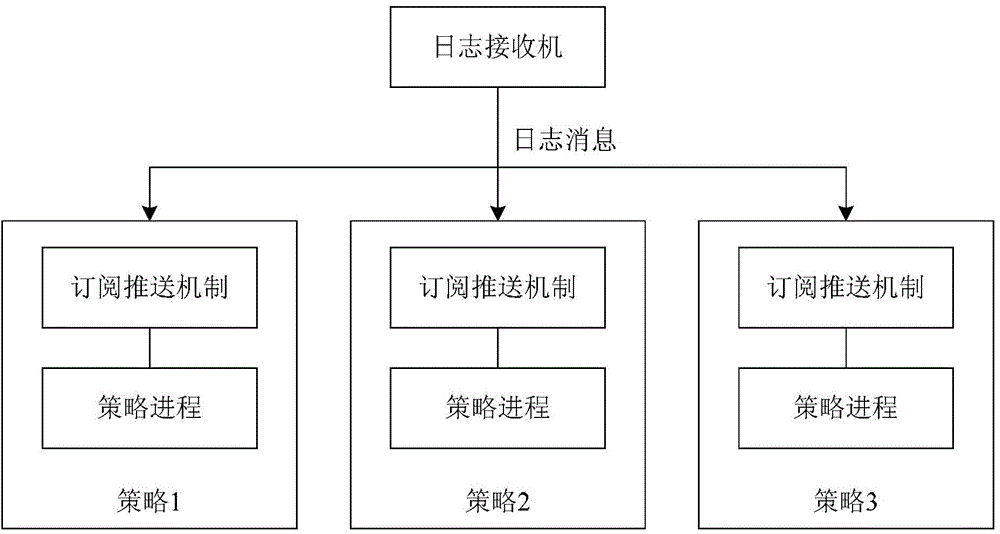
[0041] It should be clear that one of the problems to be solved by the technical solution of the present invention is to provide a method for pushing resources to subscribers who subscribe to the resources. Among them, generally speaking, for a network security system that performs relevant policy analysis based on log messages, the above-mentioned push is in response to the received log messages, or in other words, each time a log message is received, it needs to be preset to match the One or more subscribers associated with the log message or the log type to which the log message belongs pushes related resources, so that the subscribers can perform further policy-related processing operations according to the pushed resources.
[0042]In the above scenario, the related resource that needs to be sent to the subscriber in each push process represents the resource related to the received log message or the log type to which the log message belongs, and the subscriber receives th...
Embodiment 2
[0099] It should be clear that one of the problems to be solved by the technical solution of the present invention is to provide a device for pushing resources to subscribers who subscribe to the resources. Among them, generally speaking, for a network security system that performs relevant policy analysis based on log messages, the above-mentioned push is in response to the received log messages, or in other words, each time a log message is received, it needs to be preset to match the One or more subscribers associated with the log message or the log type to which the log message belongs pushes related resources, so that the subscribers can perform further policy-related processing operations according to the pushed resources.
[0100] In the above scenario, the related resource that needs to be sent to the subscriber in each push process represents the resource related to the received log message or the log type to which the log message belongs, and the subscriber receives t...
Embodiment 3
[0156] In an embodiment of the present invention, a resource service system is also provided, wherein the system may include the device for pushing resources as described in Embodiment 2 and a plurality of subscribers.
[0157] The following will be combined with Figures 24 to 26 A more specific implementation manner of the present invention is given as a reference for the resource pushing method, device and resource server system provided according to the above embodiments of the present invention.
[0158] Optionally, as in Figure 24 As shown, in the embodiment of the present invention, the overall architecture of the resource service system may include: a resource center foreground, a resource center background, and a policy unit, wherein the policy unit is used to generate and execute security policies according to received resources.
[0159] Such as Figure 24 As shown, the resource center can be divided into the front end of the resource center and the background of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More