Position privacy protection method combining k-anonymity and cloud end
A privacy protection and combination technology, applied in the field of location-based services and security privacy, can solve problems such as user privacy threats, protect location privacy, reduce the accuracy of publishing location messages, and achieve simple effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
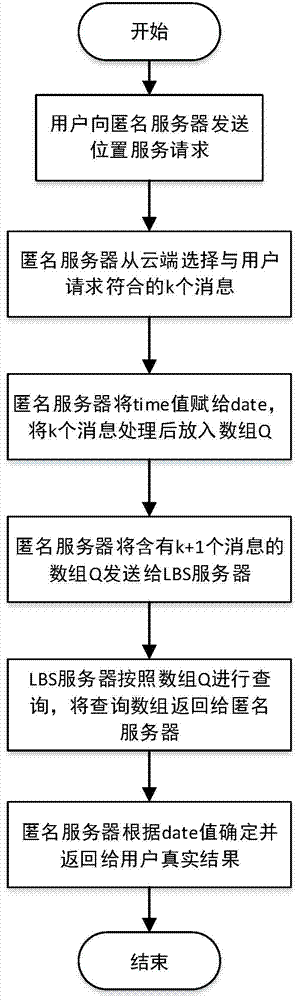
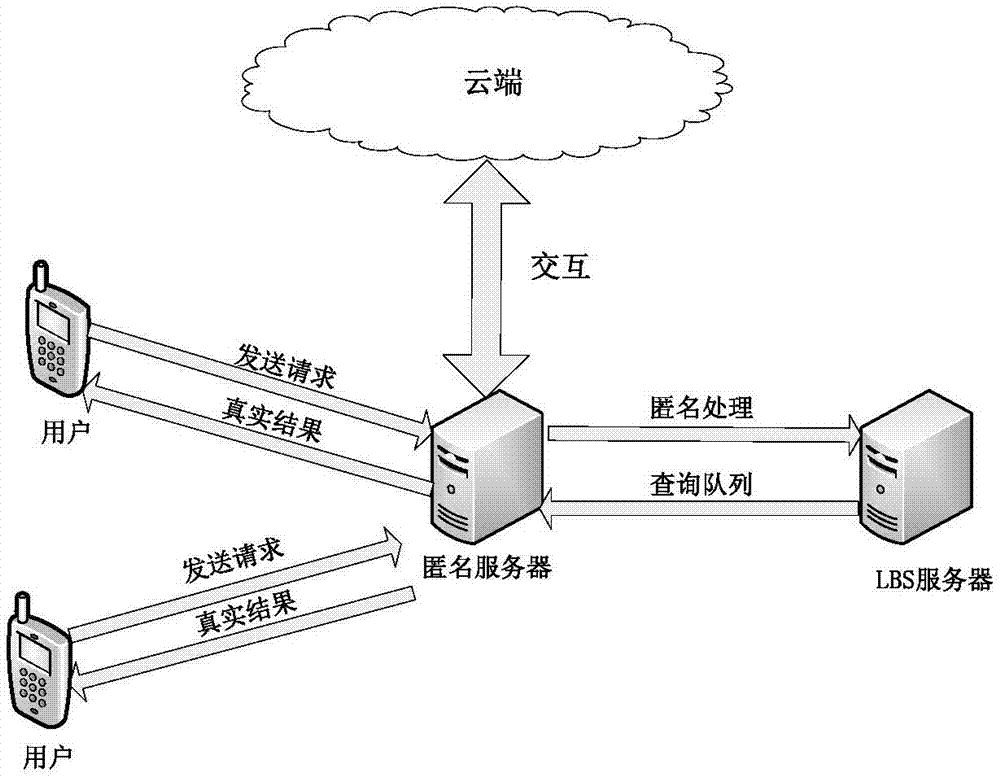
[0020] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
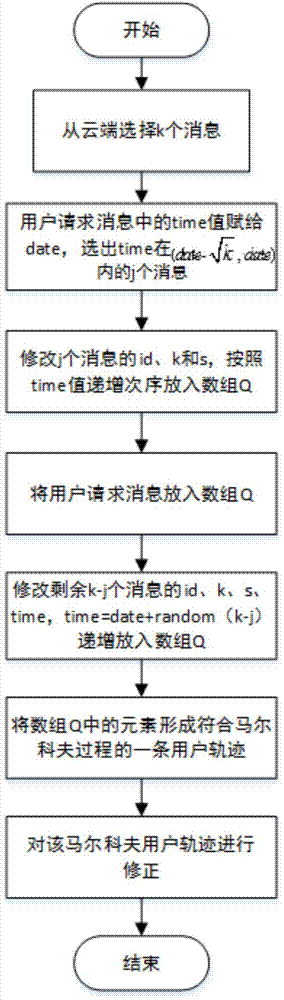
[0021] We use the six-tuple form q=(id, loc, time, qry, k, s) to represent the user's request message, where id is the id of the requesting user; loc is in the form of (x, y), indicating that the user sent The position when querying, x indicates the longitude of the position, y indicates the latitude of the position; time is the time when the request is sent; qry is the query content of the request; k indicates the anonymous parameter specified by the user; s indicates the anonymous area specified by the user.
[0022] Step 1. Send a request,
[0023] User U id If you want to check which bars are...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More