Distributed Vulnerability Scanning and Assessment Methodology
A vulnerability scanning and distributed technology, applied in the field of distributed vulnerability scanning and assessment, can solve the problems of core business interruption, data eavesdropping, core business system attacks, etc., to achieve the effect of distributed scanning, resolving secrets and improving performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0012] The present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments.
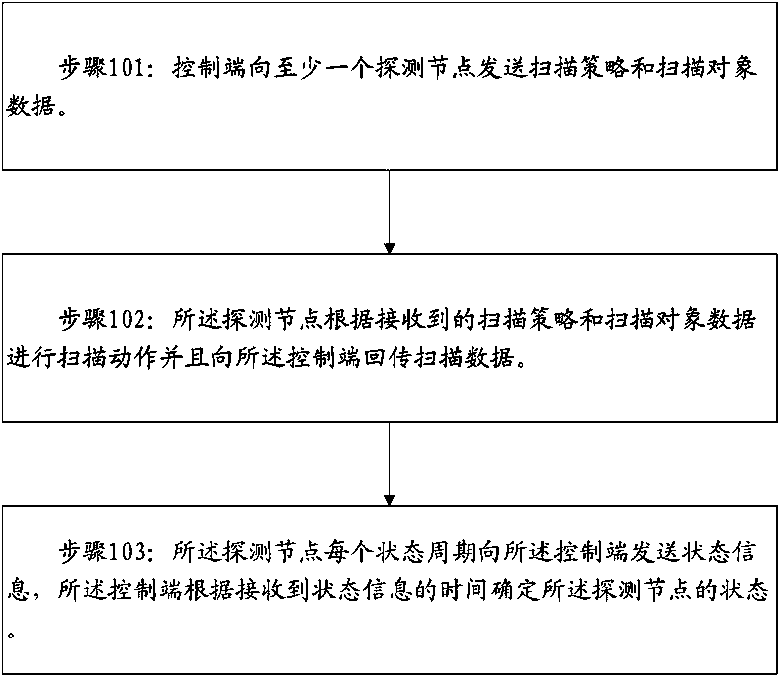
[0013] Embodiments of the present invention provide a distributed vulnerability scanning and evaluation method, such as figure 1 As shown, the method is implemented through the following steps:
[0014] Step 101: the control terminal sends scanning policy and scanning object data to at least one detecting node.
[0015] Specifically, the control terminal sets the legal IP address corresponding to each detection node for unique identification and communication.
[0016] Step 102: The detecting node performs a scanning action according to the received scanning policy and scanning object data and returns scanning data to the control terminal.
[0017] Step 103: The detection node sends state information to the control terminal every state period, and the control terminal determines the state of the detection node according to the time when the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More