Multi-Authoritative Key Policy on Lattice Attribute-Based Encryption Method
An encryption method and attribute technology, applied in the field of information security, can solve problems such as cooperation between different institutions, low workload, and inability to implement encryption methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example
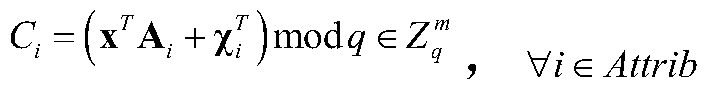
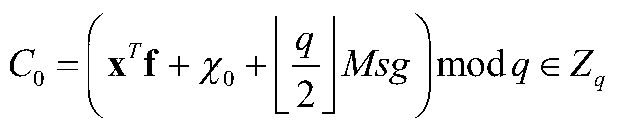
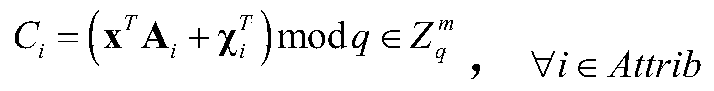
[0102] Example: Suppose challenger B randomly selects (lm+1) vectors And visit the oracle machine O to obtain (lm+1) LWE oracle machine samples and mark them as follows:
[0103]
[0104] Target: Adversary A announces the list of target attributes that it wants to attack, denoted as Attrib * , that is, the target to be challenged,
[0105] Setting: B Construct public attribute public key Apk as follows:
[0106] 1 vector is obtained from sampling with index 0, that is, s=w 0 ;
[0107] 2 For each i ∈ [l] and such that the attribute i ∈ Attrib * The corresponding public key matrix of is constructed from the LWE oracle to the sample with index i, namely
[0108] 3 For each i∈[l] and the attribute The corresponding matrix A i It is constructed according to the TrapGen algorithm in the real scheme, where the TrapGen algorithm is combined with a low-norm full-rank matrix B i makes A i B i = 0, all indexes in the LWE sampling here samples of are not used;
[...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More