Quantum key agreement protocol based on GHZ state
A technology of quantum key negotiation and protocol, applied in the field of quantum communication, which can solve the problems of inability to resist Trojan horse attacks and delayed photon Trojan horse attacks, and low qubit efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] 1. Preliminary knowledge
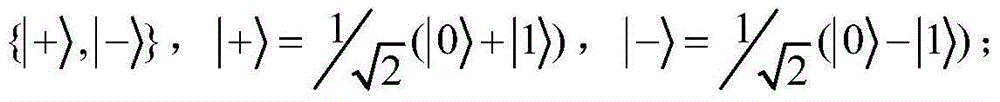
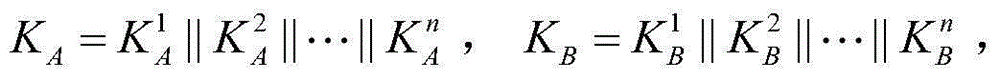
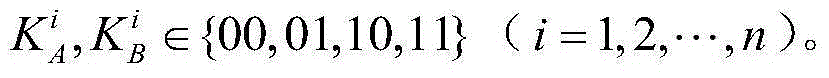
[0028] First, introduce four unitary transformations U 00 ,U 01 ,U 10 and U 11 , namely U 00 =I=|0>01 =X=|0>10 =Z=|0>11 =iY=|0>,|1>} form the Z base, {|+>,|->} form the X base, where, | + > = 1 / 2 ( | 0 > + | 1 > ) , | - > = 1 / 2 ( | 0 > + | 1 > ) .
[0029] The four Bell states are defined as follows:
[0030] | φ + > = 1 / 2 ( | 00 > ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More