Safe deactivation method and system for embedded intelligent card, and card management server for safe deactivation of embedded intelligent card
An embedded smart card and deactivation technology, applied in the field of the Internet of Things, can solve the hidden dangers of malicious attacks on embedded smart cards, and achieve the effect of avoiding terminal data transmission failure and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. The following description of at least one exemplary embodiment is merely illustrative in nature and in no way taken as limiting the invention, its application or uses. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
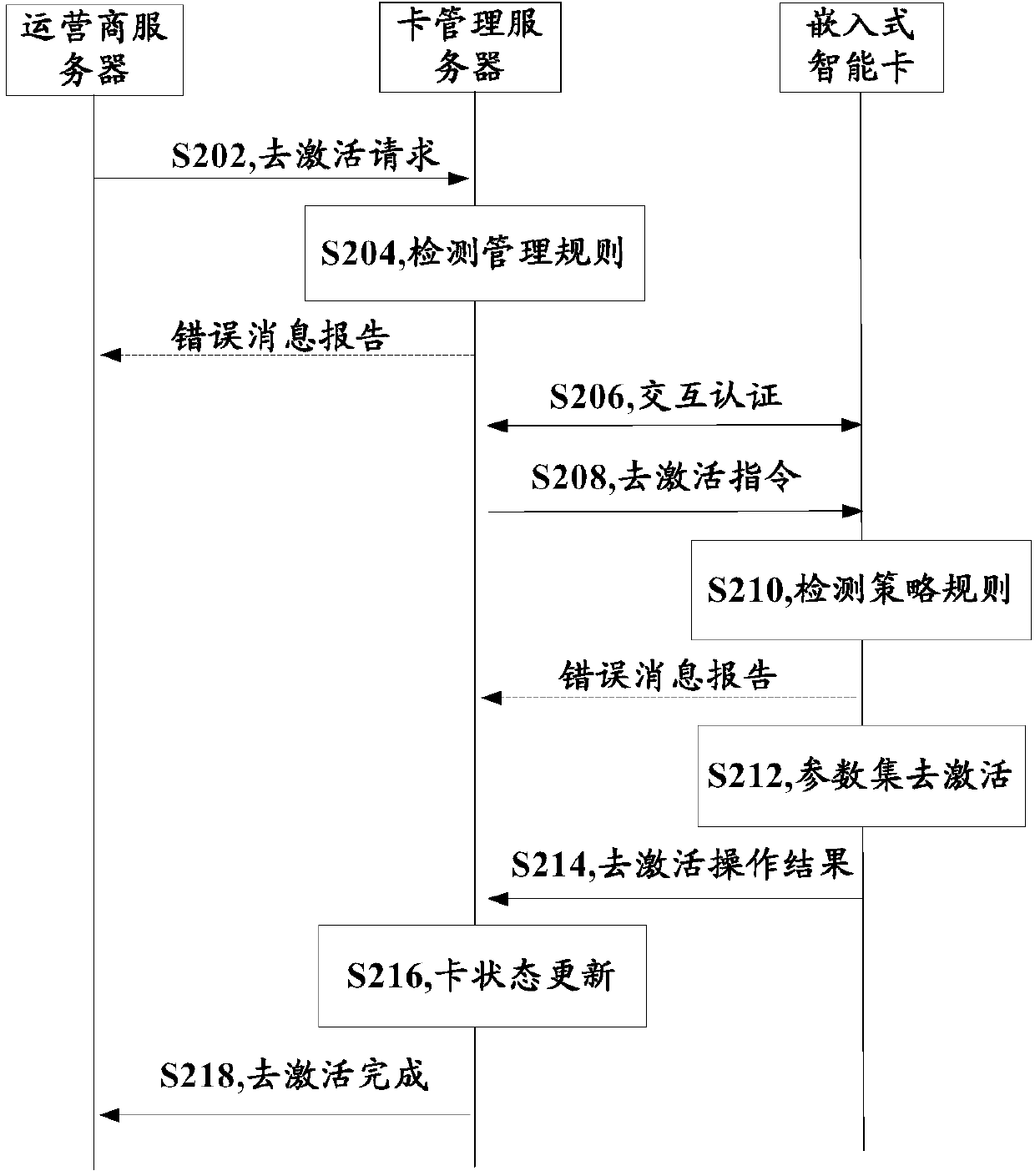
[0028] In order to solve the potential safety hazard of the embedded smart card being maliciously attacked during the deactivation process, the present invention proposes a safe deactivation scheme for the embedded smart card.
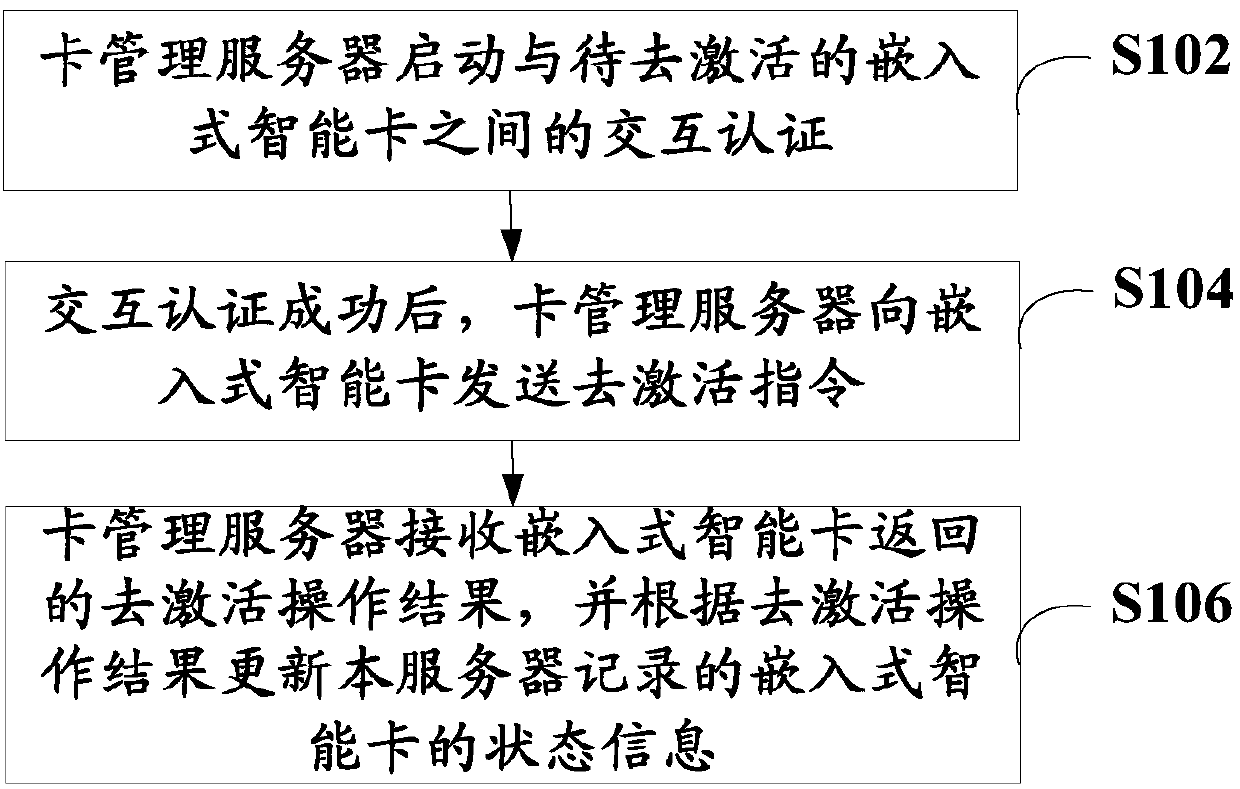
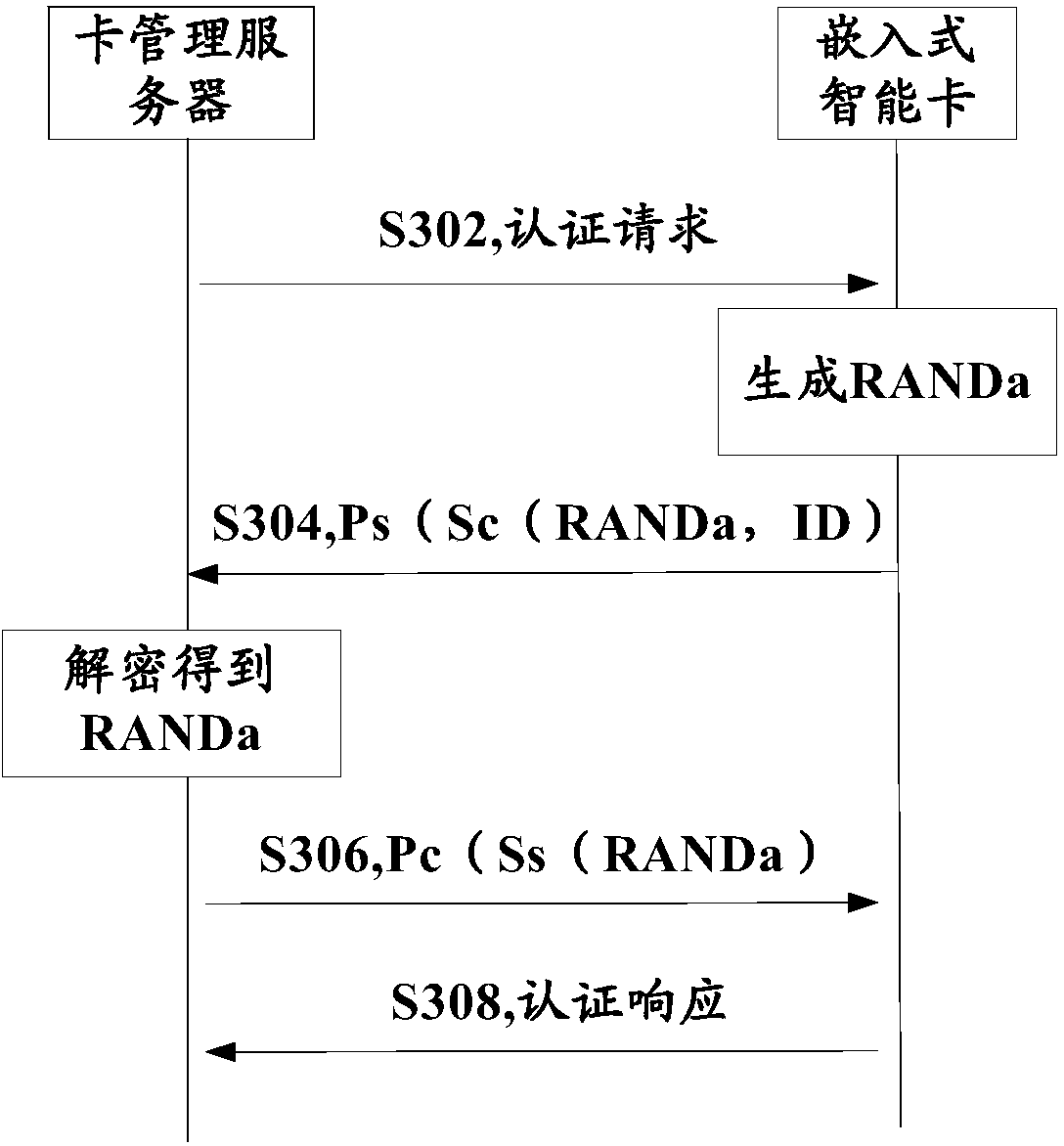
[0029] figure 1 It is a schematic flowchart of an embodiment of the met...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More