Set lock realization method and device
A realization method and technology of set lock, applied in the computer field, can solve problems such as the inapplicability of the MIPS framework
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 2
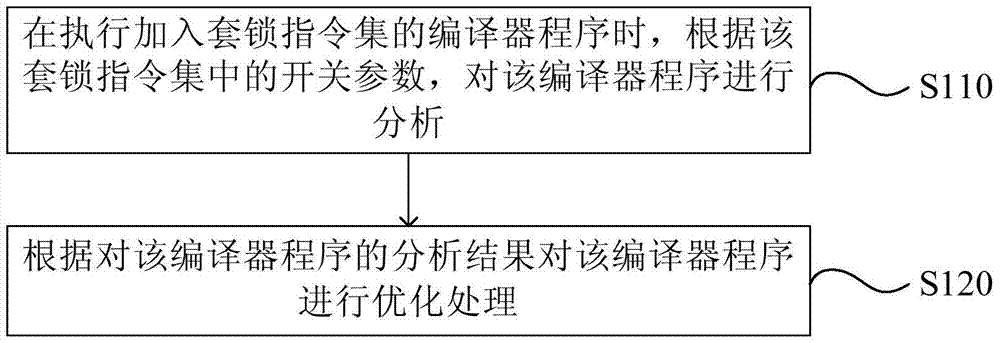
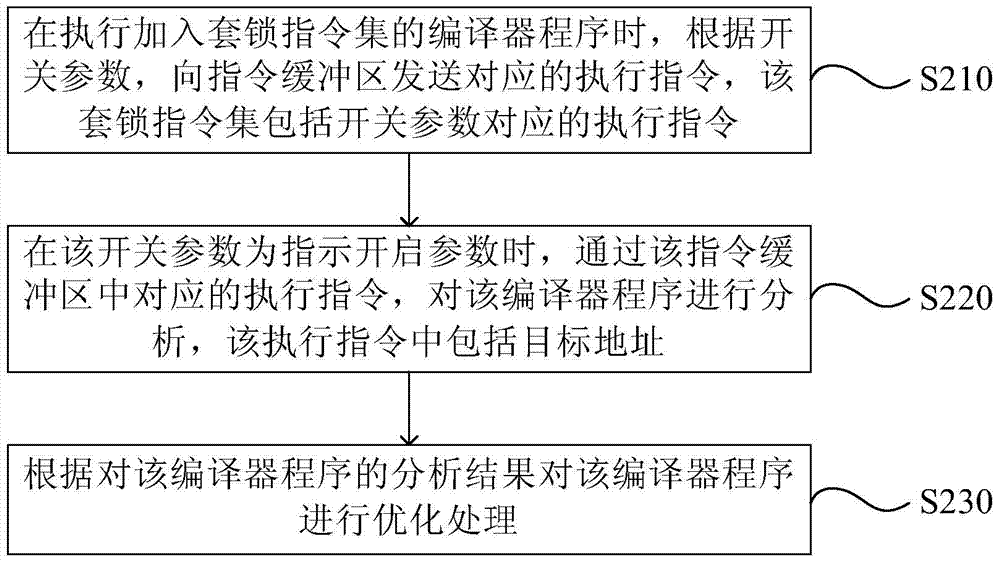
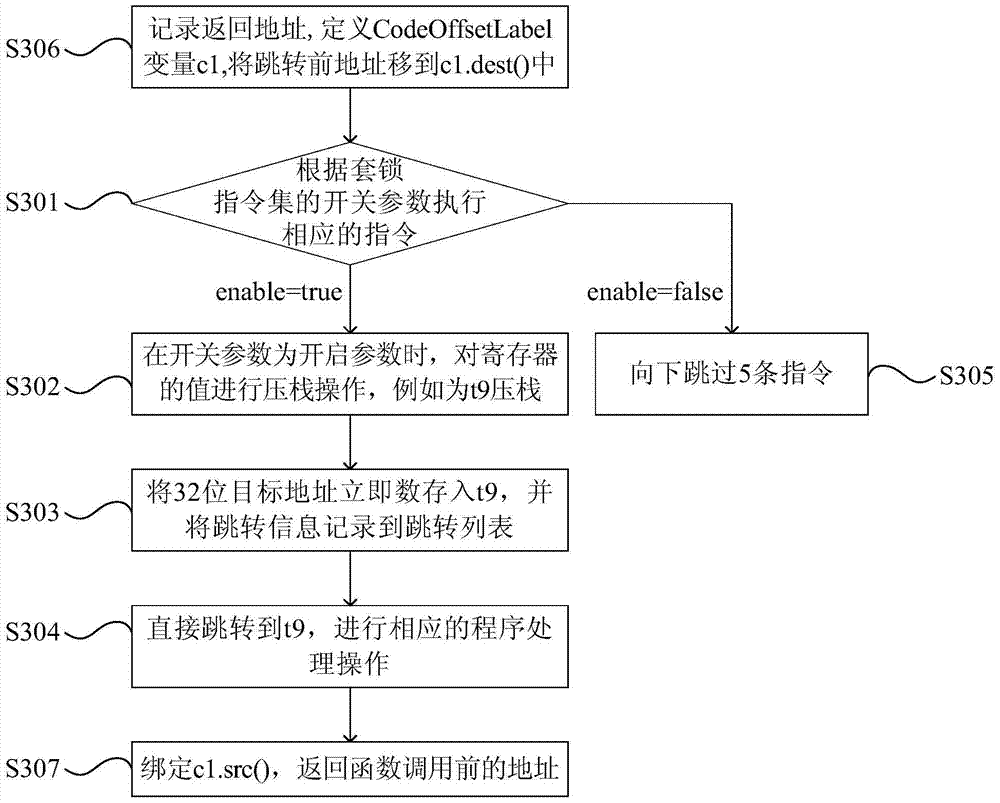
[0048] figure 2 It is a flow chart of a method for implementing a set lock provided in Embodiment 2 of the present invention. Such as figure 2 As shown, the method of this embodiment may include:
[0049] S210. When executing the compiler program added to the set of lock instructions, according to the switch parameters, send the corresponding execution instructions to the instruction buffer, where the set of lock instructions includes the execution instructions corresponding to the switch parameters.
[0050] In this embodiment, when the switch parameter indicates an on parameter or an off parameter, it corresponds to different execution instructions, that is, when the indications of the switch parameters are different, the execution instructions sent to the instruction buffer are also different.
[0051] S220, when the switch parameter is a parameter indicating to enable, analyze the compiler program through the corresponding execution instruction in the instruction buffe...
Embodiment 3
[0081] Figure 5 It is a schematic structural diagram of a set-lock realization device provided by Embodiment 3 of the present invention. Such as Figure 5 As shown, the set-lock implementation device of this embodiment specifically includes: an execution module 11 and an optimization module 12 .
[0082] Wherein, the execution module 11 is configured to analyze the compiler program according to the switch parameters in the set of lock instructions when executing the compiler program added to the set of lock instructions.
[0083] The optimization module 12 is configured to optimize the compiler program according to the analysis result of the compiler program.
[0084] The set lock implementation device provided by the embodiment of the present invention is used to implement the set lock implementation method provided by the first embodiment of the present invention, and has corresponding functional modules. Its implementation principle and technical effect are similar, and ...
Embodiment 4
[0086] Figure 6 It is a schematic structural diagram of a set-lock realization device provided by Embodiment 4 of the present invention. Such as Figure 6 As shown, the set lock realization device provided by this embodiment is in Figure 5 On the basis of the device structure shown, the set of lock instructions also includes: the execution instruction corresponding to the switch parameter. The instruction buffer sends the corresponding execution instruction; the execution unit 14 is configured to analyze the compiler program through the corresponding execution instruction in the instruction buffer when the switch parameter is an indication enable parameter.
[0087] In a specific implementation, in the device provided by this embodiment, when the switch parameter is a parameter indicating that the switch is turned on, the execution command sent to the command buffer may include the target address; correspondingly, the execution unit 14 is specifically configured to When t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com