Attack chain obtaining method and system in network environment
A network environment and acquisition method technology, applied in the field of attack chain acquisition in the network environment, can solve problems such as difficult restoration, and achieve the effect of improving recognition
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
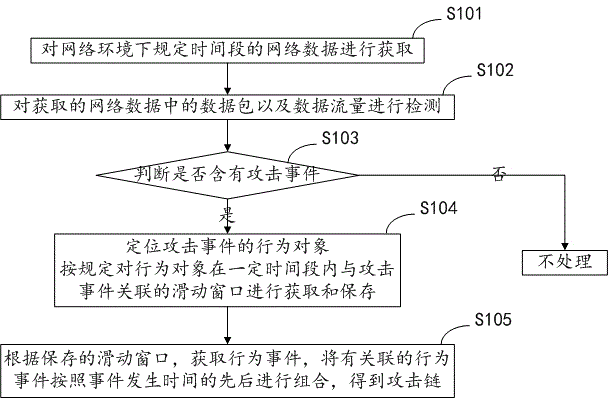
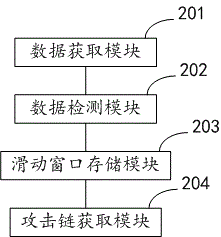
[0031] The present invention provides an embodiment of a method for acquiring an attack chain in a network environment, such as figure 1 shown, including:
[0032] S101: Acquiring network data of a specified time period under the network environment;
[0033] S102: Detect data packets and data traffic in the acquired network data;
[0034] S103: Determine whether there is an attack event, if so, enter S104, if not, do not process;
[0035] S104: Locate the behavior object of the attack event, and acquire and save the sliding window associated with the behavior object and t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More