Privilege control method of encryption document in terminal and terminal
A permission control and terminal technology, applied in the field of information security, can solve the problems of inability to control application layer permissions and to meet user needs, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
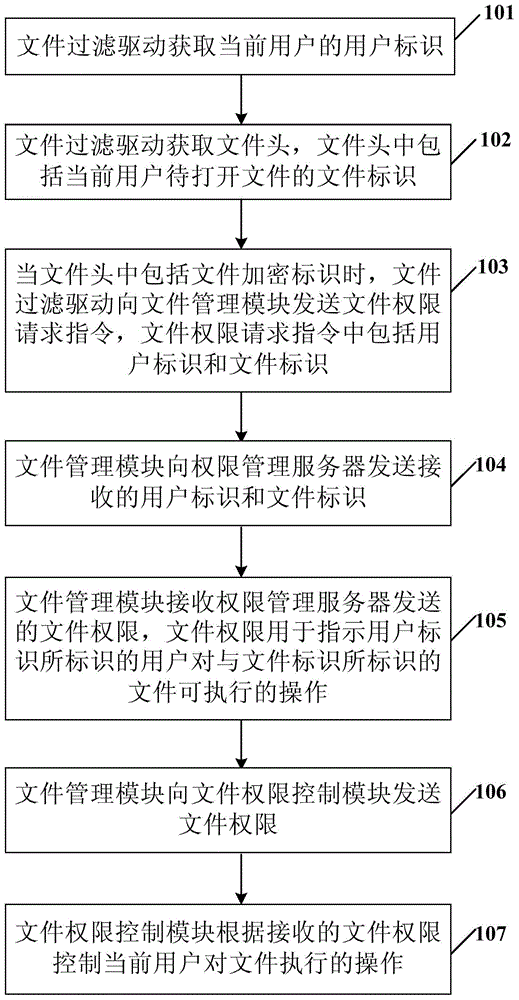
[0053] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the technical solutions in the embodiments of the present invention will be clearly described below in conjunction with the drawings in the embodiments of the present invention.
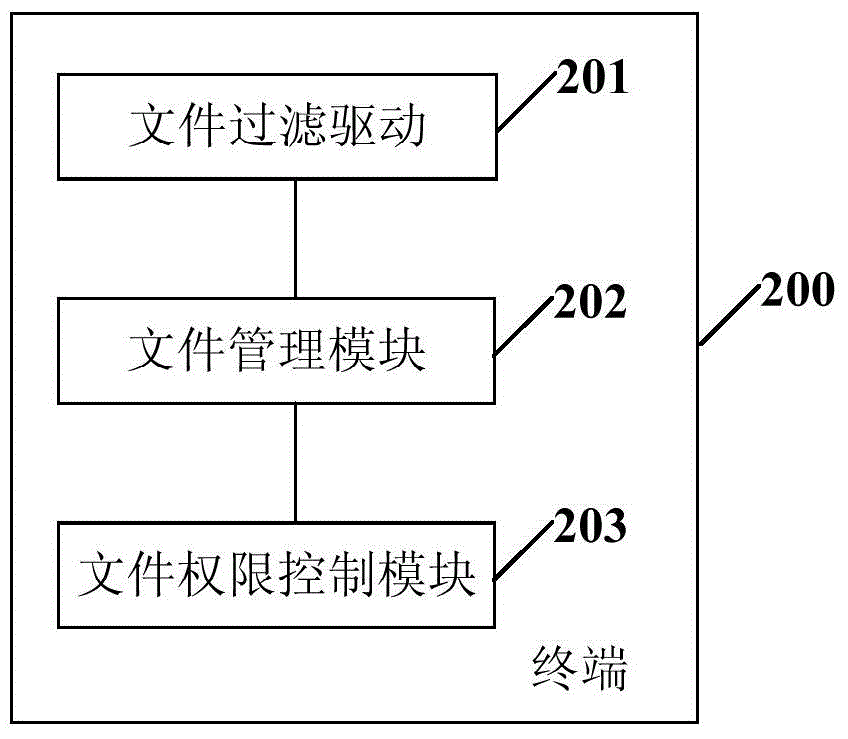
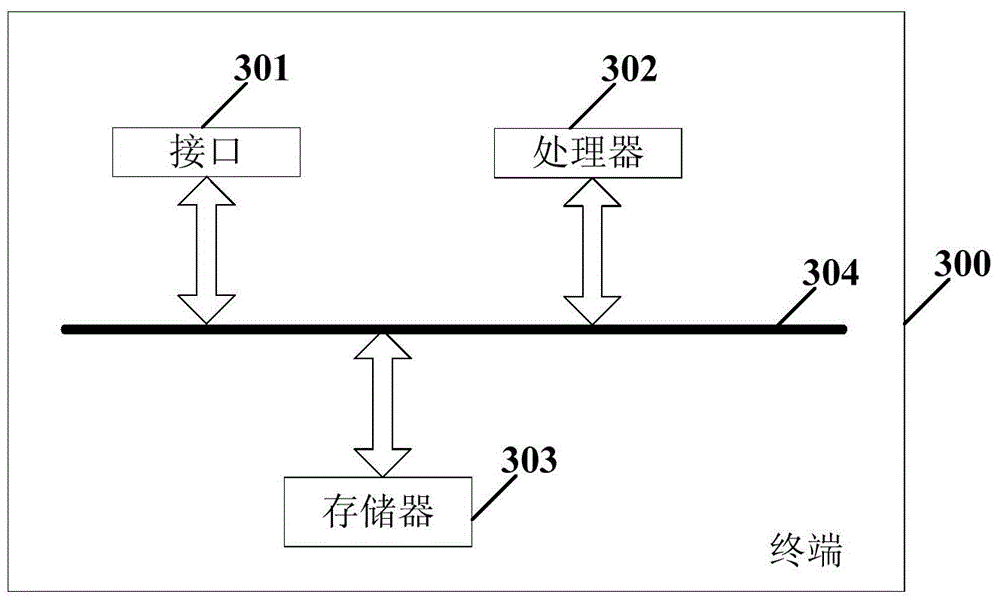
[0054] The present invention can be applied to a terminal with a Microsoft Windows (English: Microsoft Windows) operating system, and the terminal includes: a file filter driver, a file management module, and a file authority control module, wherein the file filter driver (English: Filefilterdriver) is a Windows operating system Existing drivers in the Windows operating system together with function drivers form the driver of the Windows operating system, and the function driver is used to process real business, while the file filter driver is a driver that hangs on the upper or lower layer of the function driver, and all function calls will be After the upper file filter dri...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More