User access cancelling control method based on agent re-encryption
A proxy re-encryption and access control technology, applied in the field of user revocation access control based on proxy re-encryption, can solve the problems of reducing data upload efficiency and increasing the burden on data owners
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
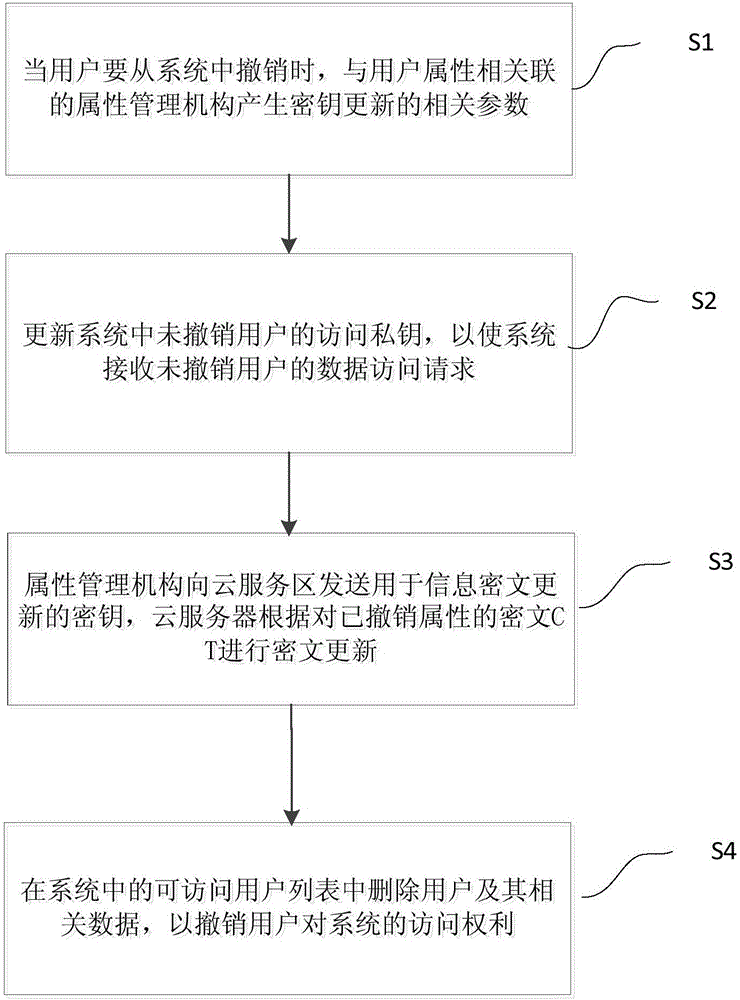
Image
Examples
Embodiment Construction
[0031] Embodiments of the present invention are described in detail below, examples of which are shown in the drawings, wherein the same or similar reference numerals designate the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary and are intended to explain the present invention and should not be construed as limiting the present invention.
[0032] The invention proposes a user revocation access control method based on proxy re-encryption. The method adopts proxy re-encryption technology to realize access control to revoked users and non-revoked users.
[0033] Firstly, the proxy re-encryption technology will be described below.
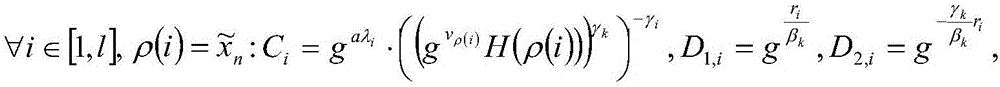
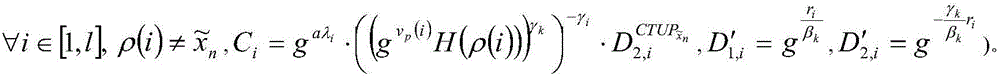
[0034] Proxy re-encryption technology is a key conversion mechanism, and its technical implementation process is as follows: firstly, the conversion key ω is generated; secondly, the proxy server uses ω to convert the encryption operation p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More