Authentication method for network security access and authentication system for implementing method
An access authentication and network security technology, applied in the field of network security access, can solve problems such as DSCP value legality check, DSCP value spoofing, network attack, etc., and achieve the effect of easy IPQoS guarantee and simple internal state
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] This embodiment is a preferred implementation mode of the present invention, and other principles and basic structures that are the same or similar to this embodiment are within the protection scope of the present invention.
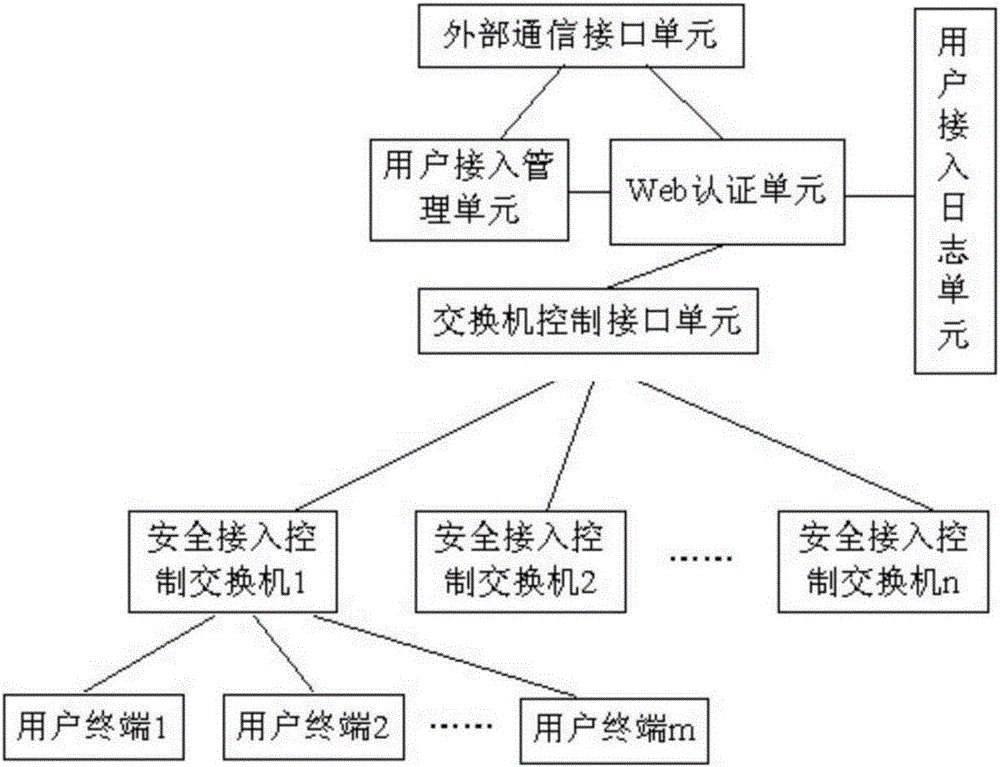
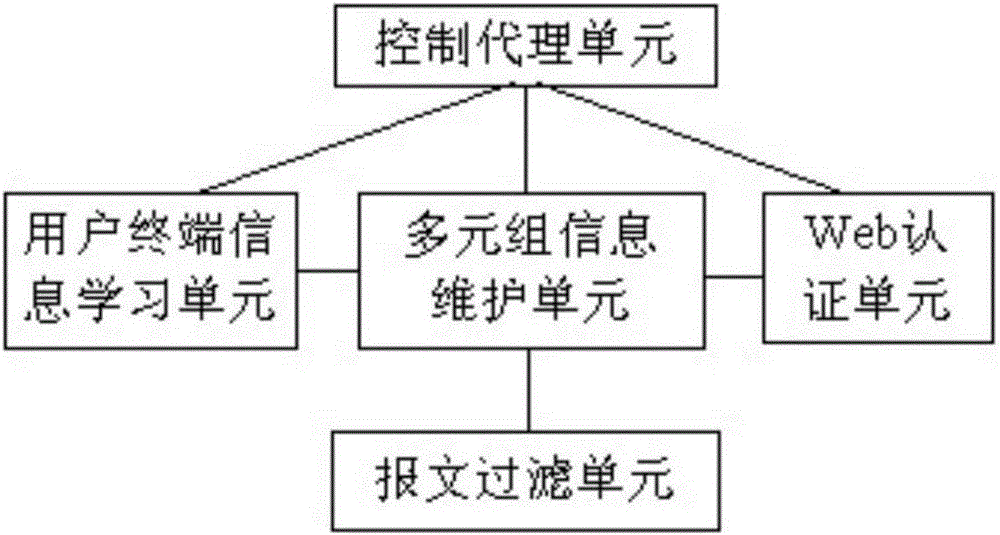
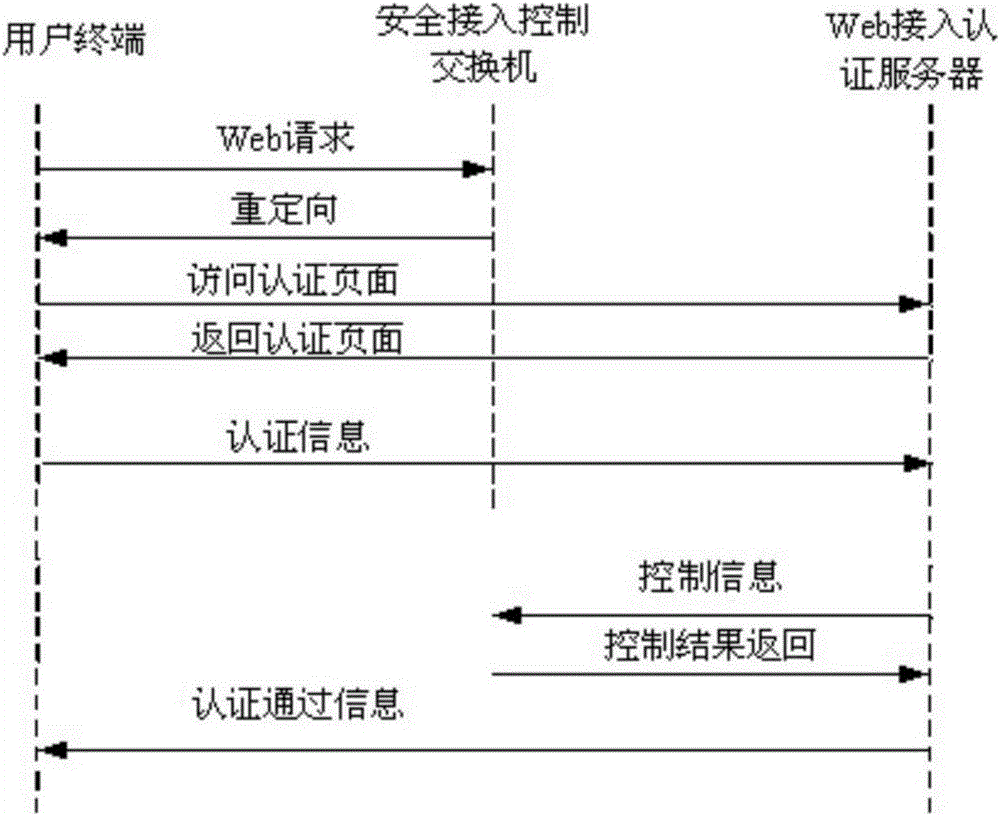
[0024] Please see figure 1 And attached figure 2 , a schematic diagram of a typical system structure of a switch-based network authentication system, including multiple security access control switches, Web access authentication servers, and user terminals, where the Web access authentication server and security access control switches are interconnected through the network , the security access control switch is connected to the user terminal through the access network. A typical implementation of a secure access control switch includes a user terminal information learning unit, a tuple information maintenance unit, a Web authentication unit, a control proxy unit and a message filtering unit, a control proxy unit and a user terminal information...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More