Method and device for revoking authority
An authorization token and time-limited technology, applied in security devices, secure communication devices, computer security devices, etc., can solve the problems of multiple manpower and time costs, low actual efficiency, and increased difficulty in technical implementation, so as to reduce the difficulty of technical implementation, The effect of improving processing efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
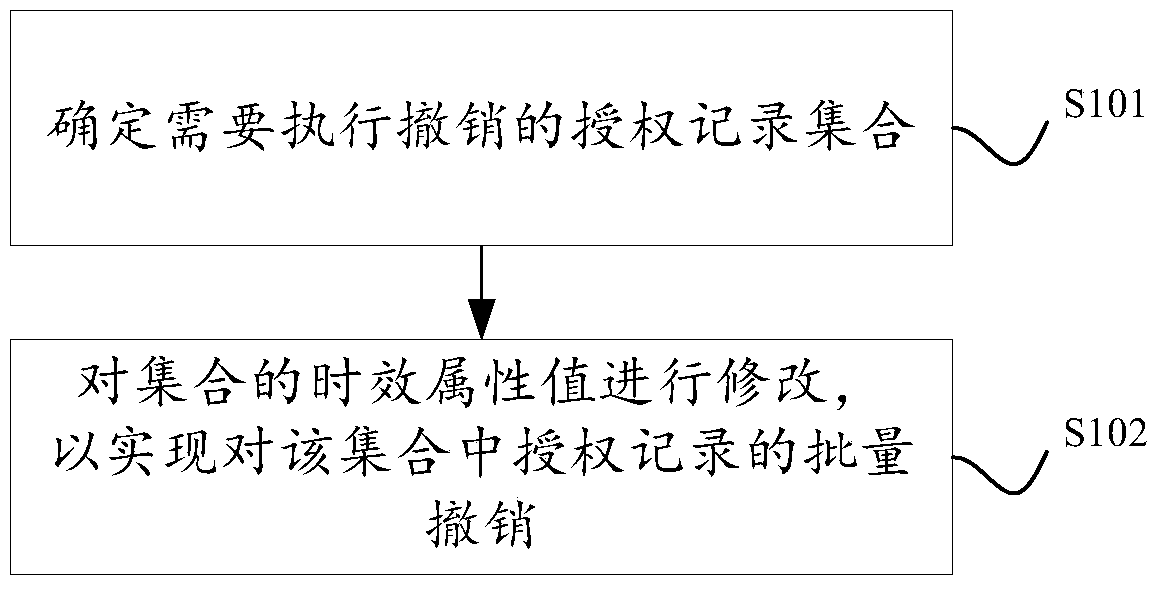
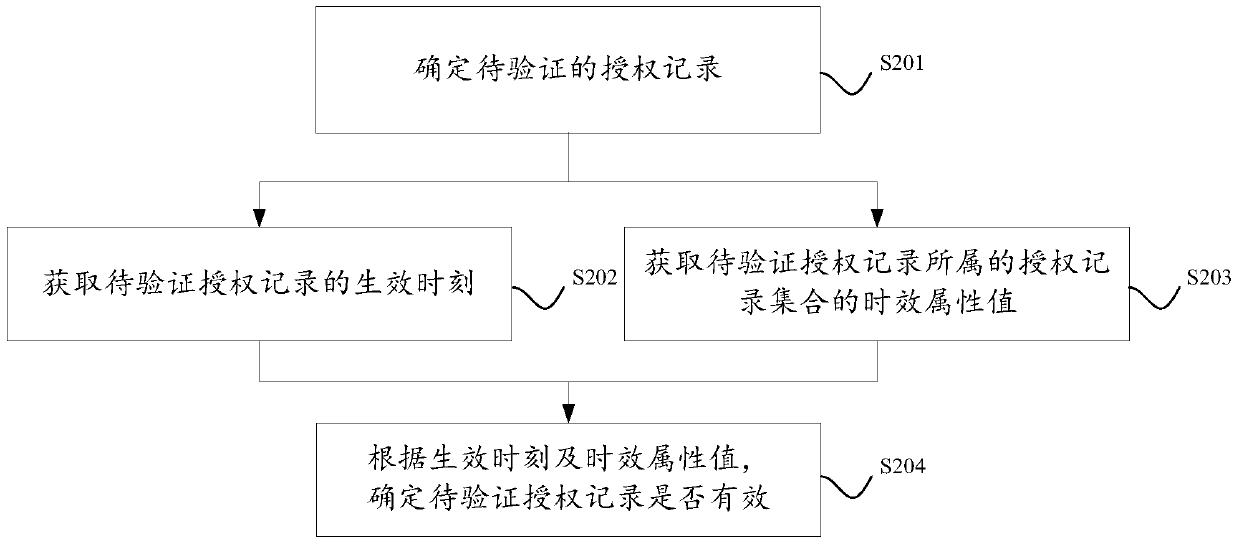
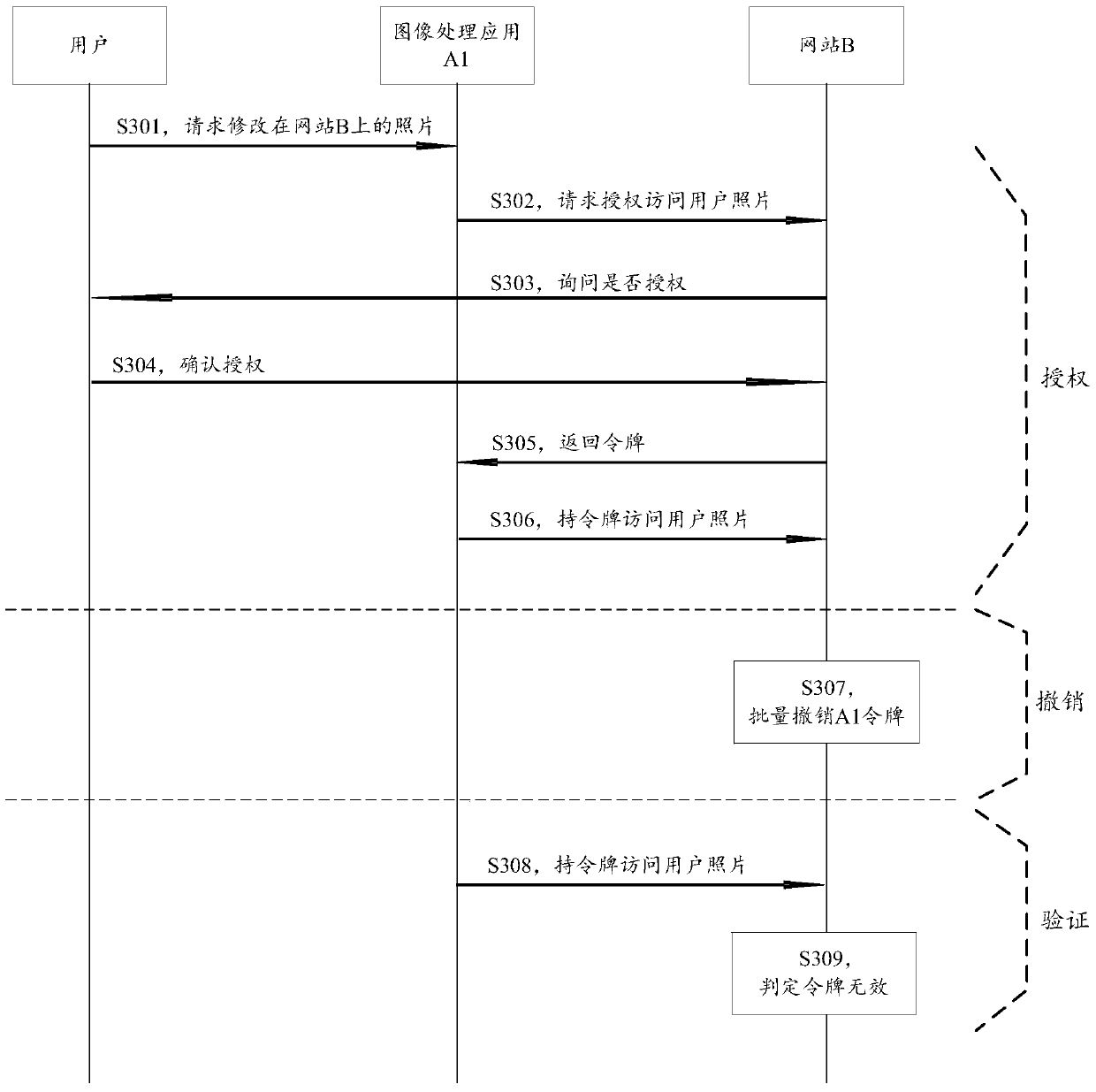
Method used
Image
Examples
Embodiment Construction
[0047] In order to enable those skilled in the art to better understand the technical solutions in the present application, the technical solutions in the embodiments of the present application will be described in detail below in conjunction with the drawings in the embodiments of the present application. Obviously, the described embodiments are only It is a part of the embodiments of this application, not all of them. All other embodiments obtained by persons of ordinary skill in the art based on the embodiments in this application shall fall within the protection scope of this application.
[0048] For the authorizing party, each permission that has been opened to the authorized party is stored in the database in the form of a data record. Table 1 shows an example of the data structure of a permission record. It should be noted that in this table The field attributes shown are for illustrative purposes only and do not constitute limitations on the scenario itself:
[0049]...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More