Authentication method and system in trust execution environment
A technology of execution environment and authentication method, applied in transmission systems, digital transmission systems, secure communication devices, etc., can solve problems such as embezzlement, attack on business applications, data leakage, etc., and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
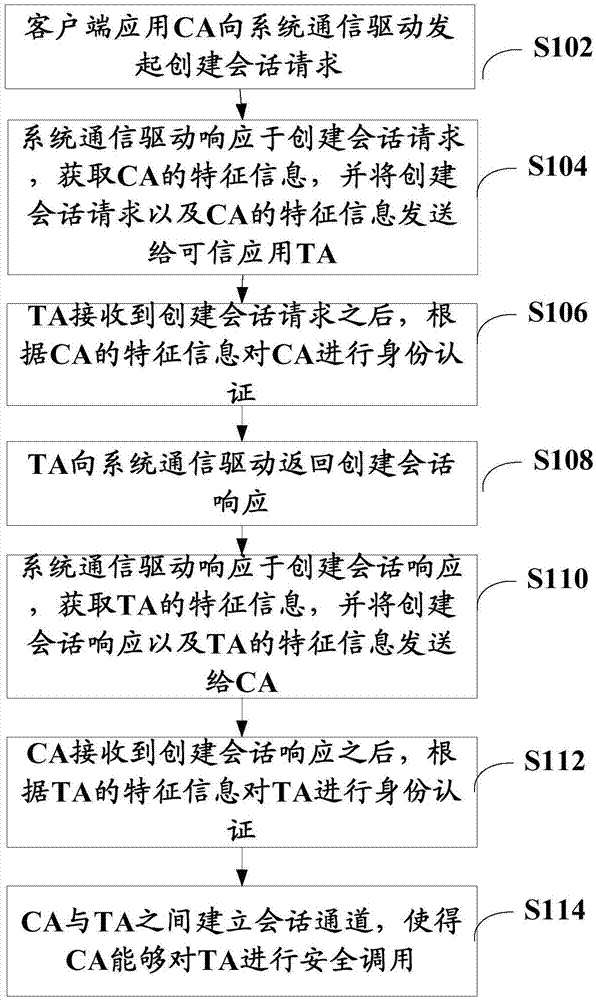
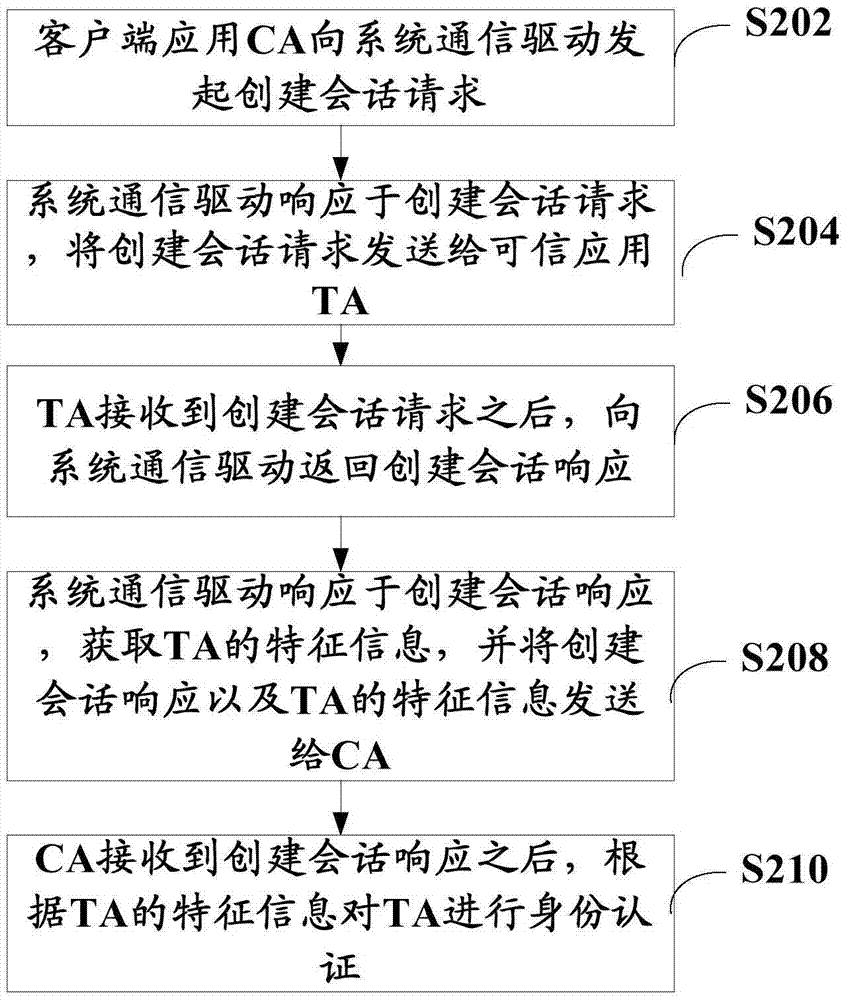
[0023] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. The following description of at least one exemplary embodiment is merely illustrative in nature and in no way taken as limiting the invention, its application or uses. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0024] The present invention is proposed based on the identity authentication problem between the trusted application TA and the client application CA.
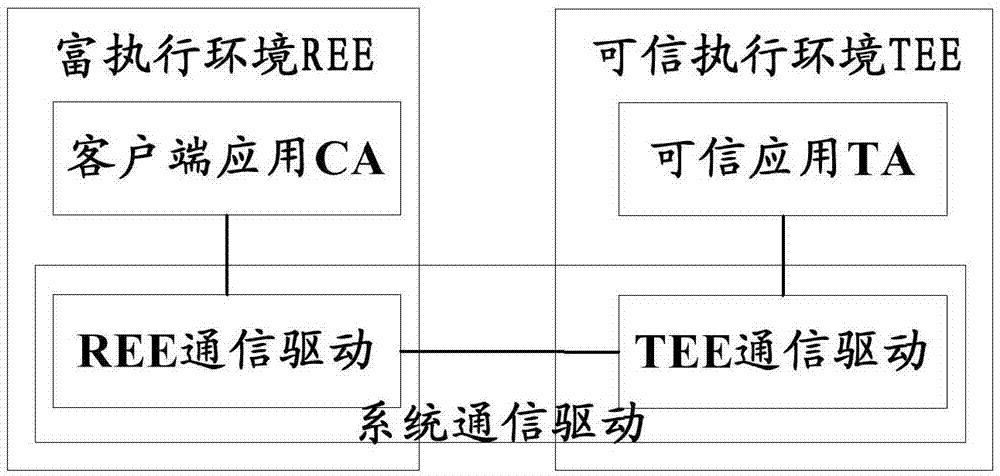
[0025] image 3 It is a schematic diagram of deployment of trusted application TA and client application CA in the present invention. Such as i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More