Multiple address access method and device for signals in mobile communication
A technology of mobile communication and access method, which is applied in the field of communication, and can solve the problems of short check matrix, high computational complexity, and lack of sparsity.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
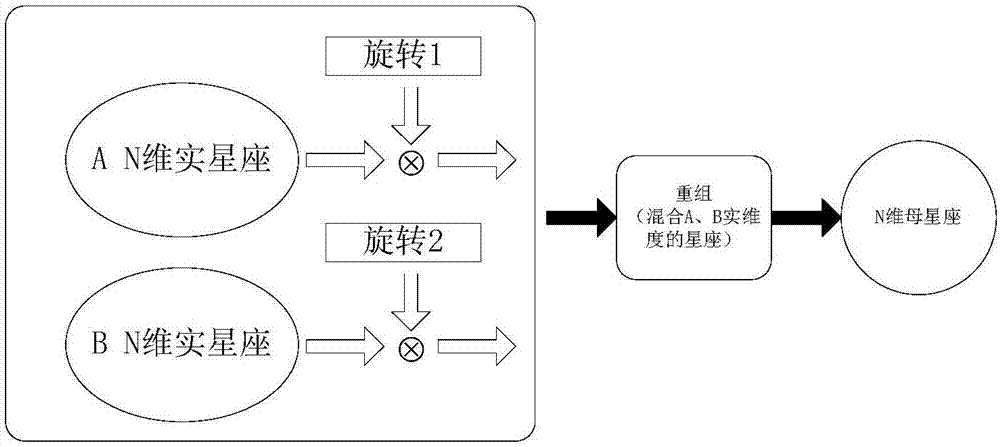
Method used
Image
Examples
Embodiment 1
[0121] Embodiment 1: The parity check matrix is a regular small-dimensional matrix
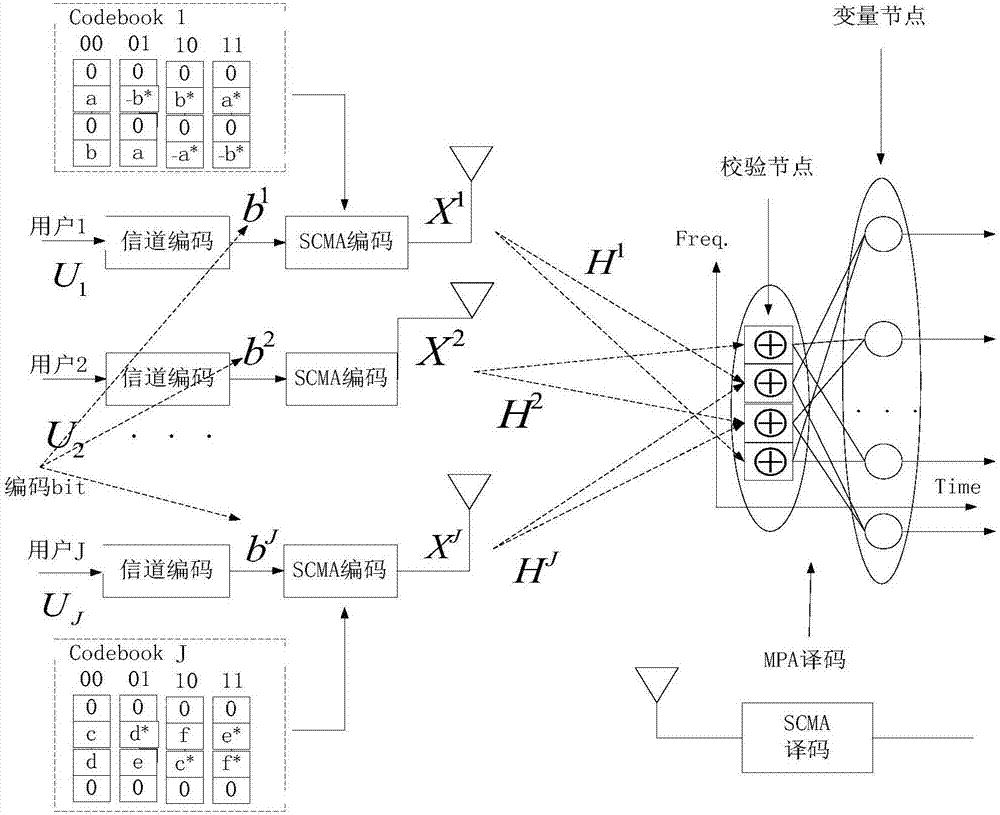
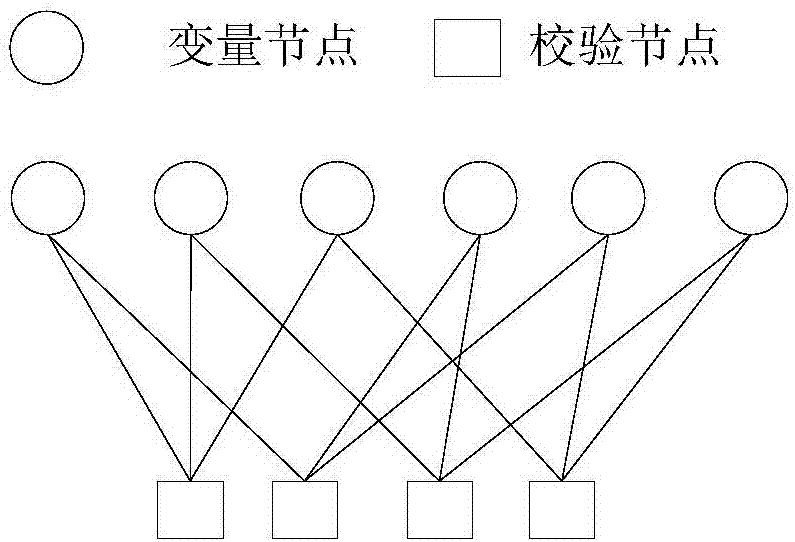
[0122]The scheme adopts the traditional SCMA method, and the simulation adopts figure 2 As shown in the factor diagram, there are J=6 users at the sending end, assuming that there is a near-far effect, these 6 users are divided into two groups, each group has three users, the number of subcarriers is K=4, and the overload rate is 150%. The corresponding rule The parity check matrix is as in formula (8), with a row degree of 3 and a column degree of 2.
[0123]
[0124] The codebook used in the simulation is a 4-point codebook constructed according to the traditional SCMA codebook design. The two non-zero parts of each layer data stream are as follows: Figure 9 shown.
Embodiment 2
[0125] Embodiment 2: check matrix is a regular low-density matrix
[0126] Aiming at the problem that the dimension of the traditional SCMA parity check matrix is small, the present invention expands the dimension of the parity check matrix, the number of users is 6 for the simulation, the length of each user's coded information is 96, the code rate R=1 / 2, and QPSK modulation is adopted , then the number of symbols corresponding to each user is 96, using Representing the 96 symbol vectors of the jth user, there are 576 symbols in total before spreading, and these symbols are spread and superimposed on 384 carriers. The parity check matrix corresponding to the above process corresponds to a row degree of 3 and a column degree of 2.
Embodiment 3
[0127] Embodiment 3: The parity check matrix is an irregular low-density matrix
[0128] When the near-far effect exists, the present invention considers constructing an irregular parity check matrix to realize unequal protection for remote users, thereby improving the overall performance of the system. When there is a near-far effect, the present invention still expands the dimension of the parity check matrix. The number of users used in the simulation is 6, the coded information length of each user is 96, the code rate R=1 / 2, and QPSK modulation is adopted, and each user corresponds to The number of symbols is 96, use Representing the 96 symbol vectors of the jth user, there are 576 symbols in total before spreading, and then these symbols are spread and superimposed on 384 carriers. Corresponding irregular check matrix, row degree ρ 4 =0.5, ρ 5 =0.5, the column degree is λ 2 =0.5,λ 4 =0.5, ρ i Indicates the proportion of row degree i, λ i Indicates the proportion...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More