Mutual anonymous authentication and key agreement protocol in mobile network
A technology of mutual authentication and key agreement, applied in the field of anonymous mutual authentication and key agreement protocol, which can solve problems such as insecurity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] The preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
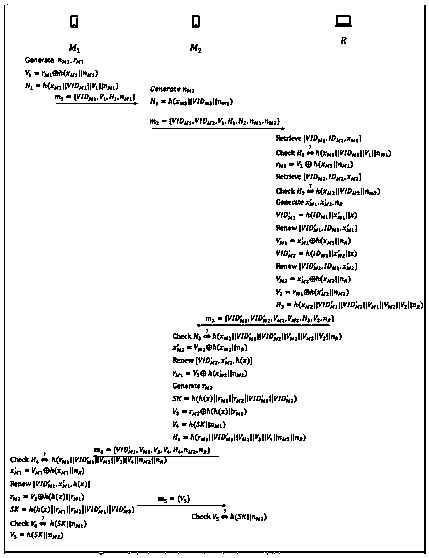
[0025] figure 1 As shown, an anonymous mutual authentication and key agreement protocol in a mobile network, which includes the following steps:
[0026] A. Registration stage: The legal mobile device will first send identity information to the server for registration. The specific steps are as follows:
[0027] A1: Mobile device choose yourself , sent to the server through a secret channel ;
[0028] A2: The server generates the key , and then calculate , and store [ ], the server sends [ ] to the mobile device.
[0029] A3: The mobile device receives and stores [ ].
[0030] B. Authentication and key agreement phase, assuming two legally registe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More