Cloud database security audit method based on Docker virtualization
A security audit and database technology, applied in the field of cloud database security audit based on Docker virtualization, can solve problems such as immature technology, and achieve the effect of improving security and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] The technical solutions in the embodiments of the present invention will be described clearly and in detail below with reference to the drawings in the embodiments of the present invention. The described embodiments are only some of the embodiments of the invention.
[0032] The technical scheme that the present invention solves the problems of the technologies described above is:
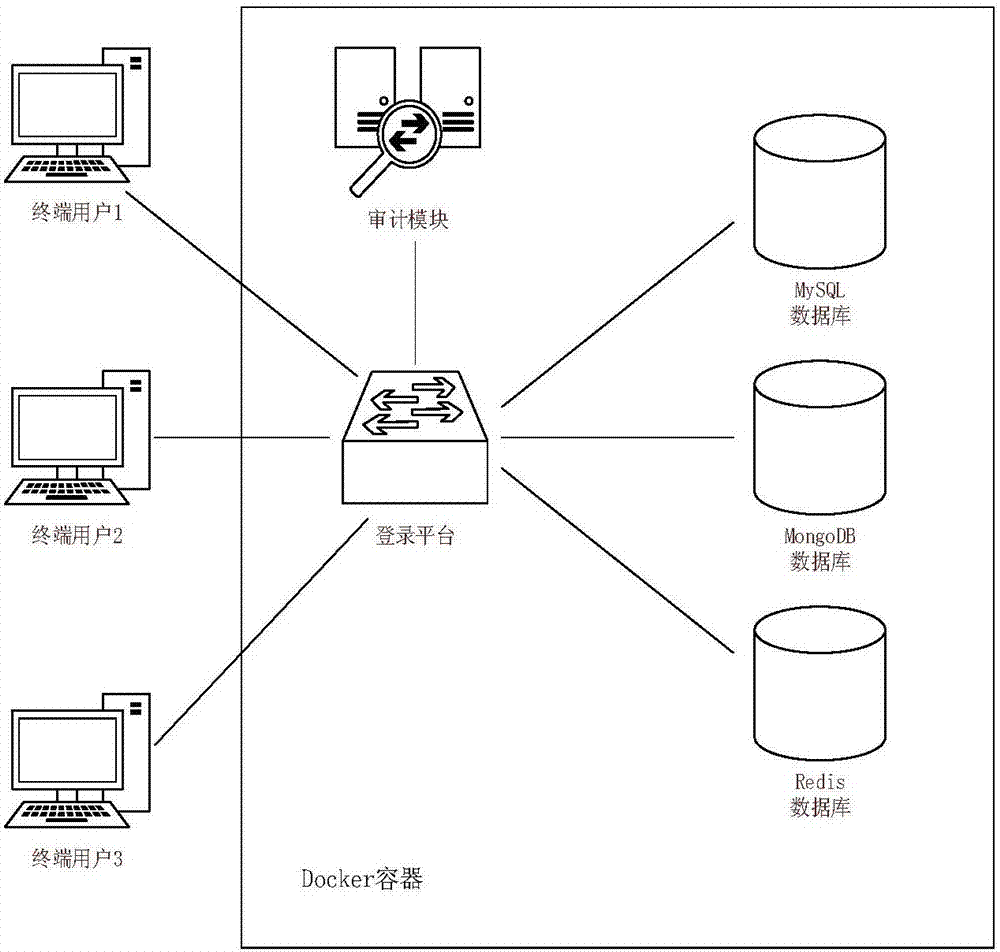
[0033] figure 1 It is a schematic diagram of a network architecture in related technologies, see figure 1 , There are multiple database images configured in the Docker container, such as MySQL, Redis, MongoDB, etc. Download the Linux image in the Docker public warehouse, load the login and audit platform, repackage and enable it. Each client needs to access the above-mentioned database through the platform, so as to realize the audit of the access of each client.
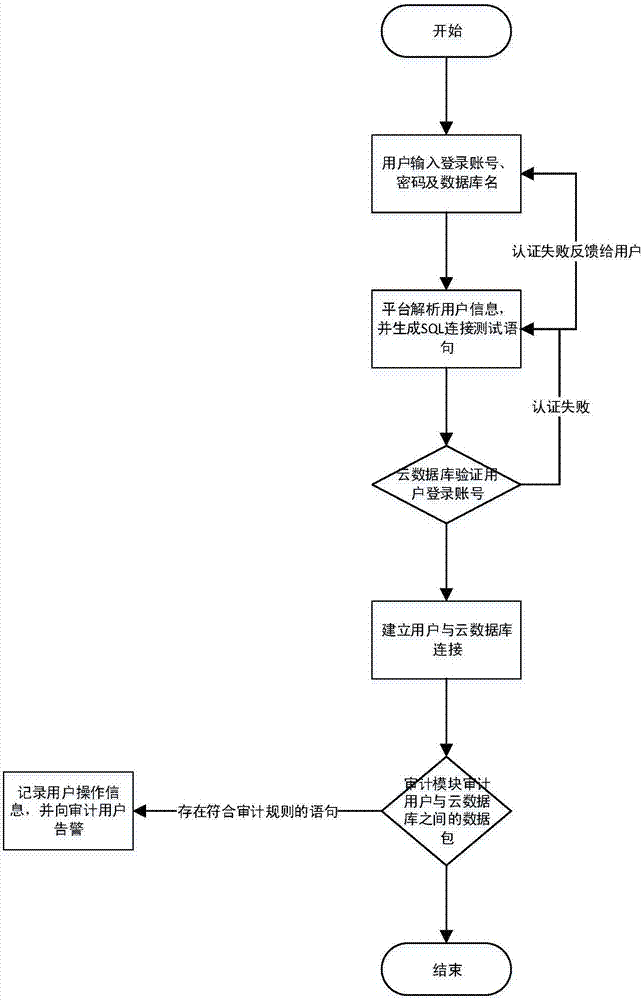
[0034] Take the MySQL database as an example. When client 1 accesses the MySQL database in Docker, it can send a request me...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More