Encryption method and device and decryption method and device
An encryption method and encryption and decryption technology, applied in the fields of devices and decryption methods, devices, and encryption methods, can solve problems such as leakage, page theft, and page incompleteness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly described below in conjunction with the drawings and embodiments of the embodiments of the present invention.
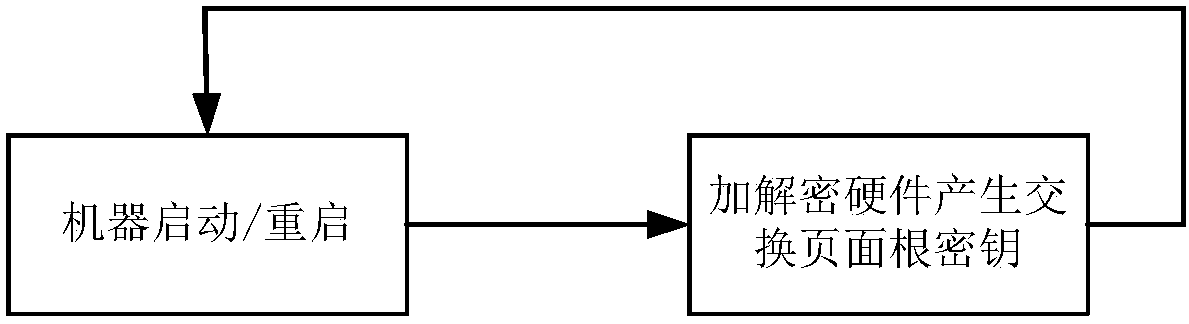
[0028] figure 1 A schematic diagram of generating a swap page root key (SwapRootKey) provided by an embodiment of the present invention. Such as figure 1 As shown, when the computer is just started, a one-time key, namely SwapRootKey, is generated in the computer and stored in the encryption and decryption hardware. The encryption and decryption hardware can be a secure processor (Secure Processor), and this SwapRootKey only The hardware is ready to use, and every time the computer is restarted, a new SwapRootKey is generated.
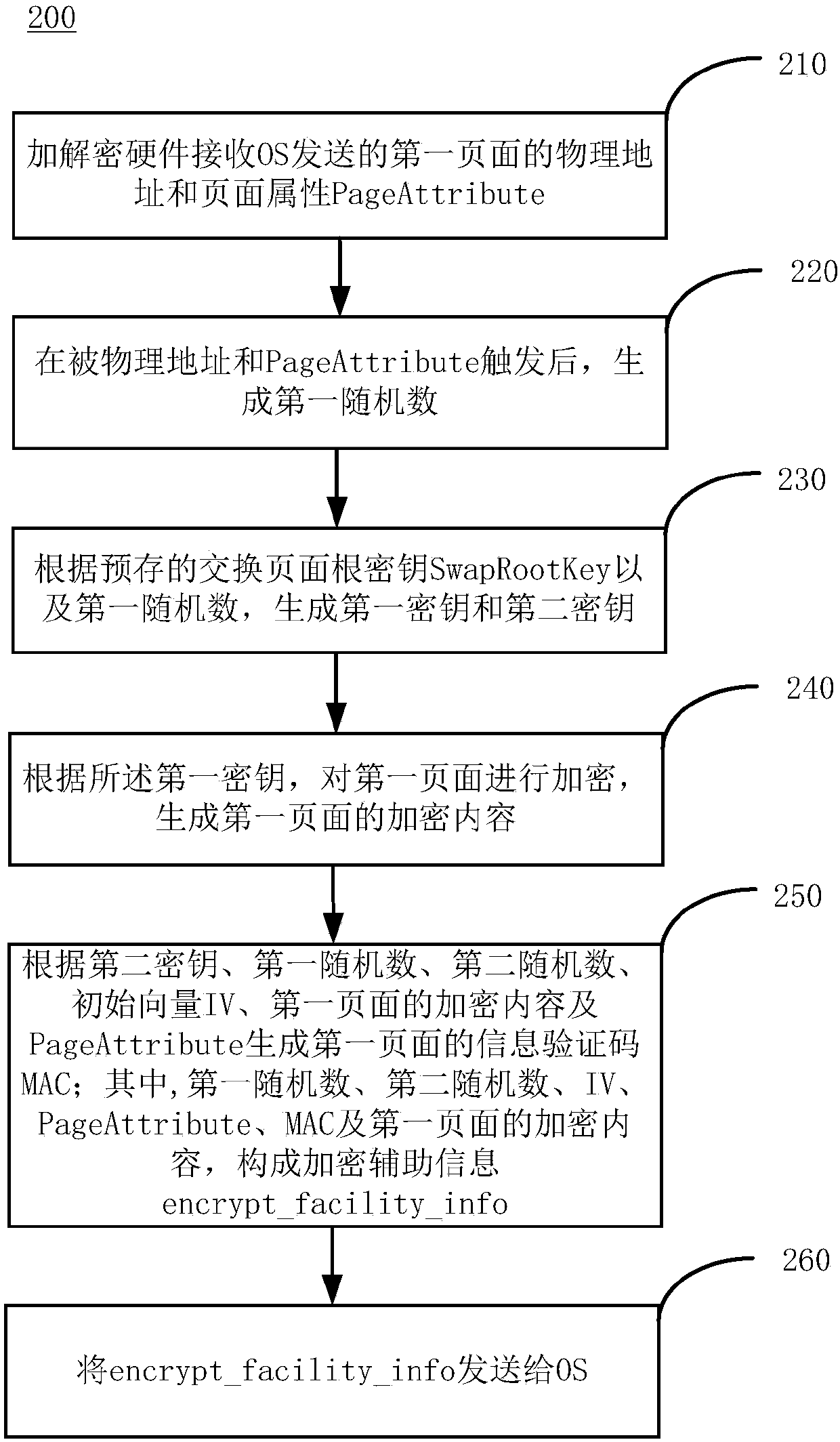
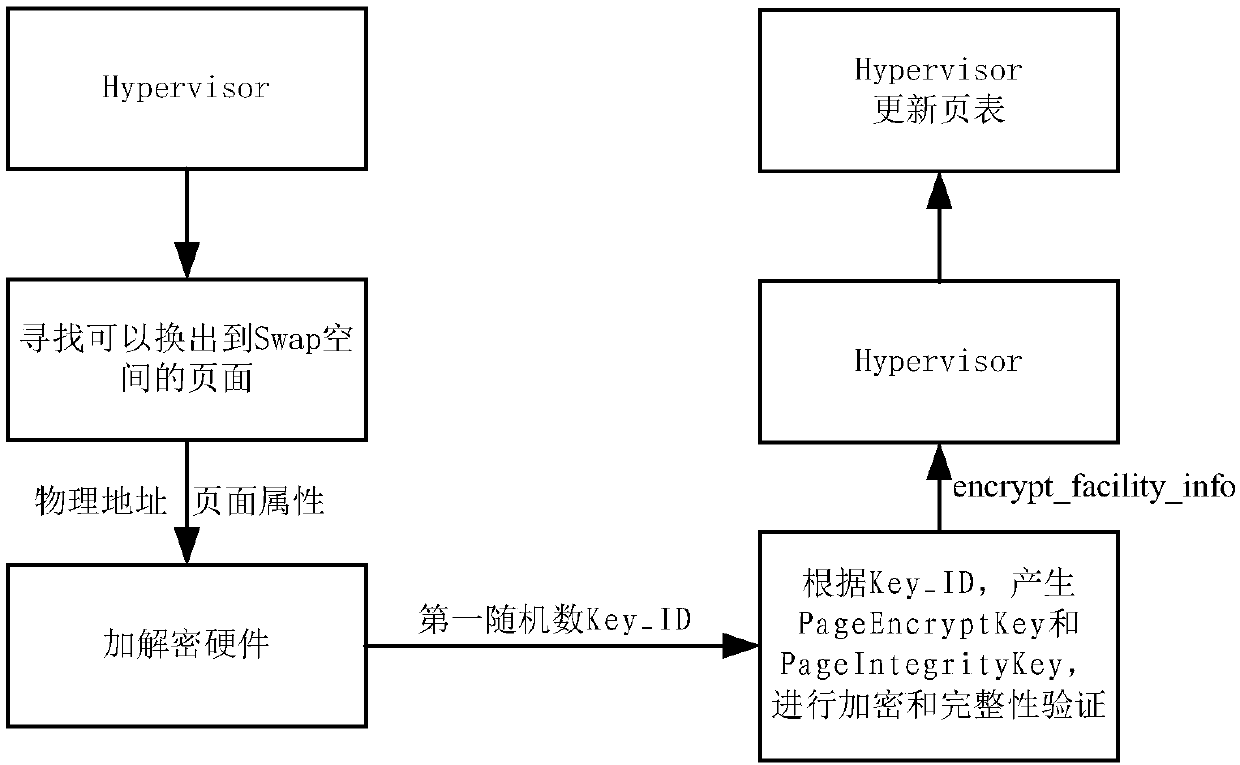
[0029] The encryption and decryption hardware provides the interface ENCRYPT_FOR_PAGE_OUT, which can also be implemented by directly ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More