Network security detecting method and device
A network security and detection method technology, applied in the field of big data, can solve problems such as low efficiency, complex calculation, and inability to meet the detection requirements of dynamic changes and large data volumes
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The technical solutions of the present invention will be described in further detail below with reference to the accompanying drawings and embodiments.
[0033] The flowchart of an embodiment of the network security monitoring method of the present invention is as follows figure 1 shown.
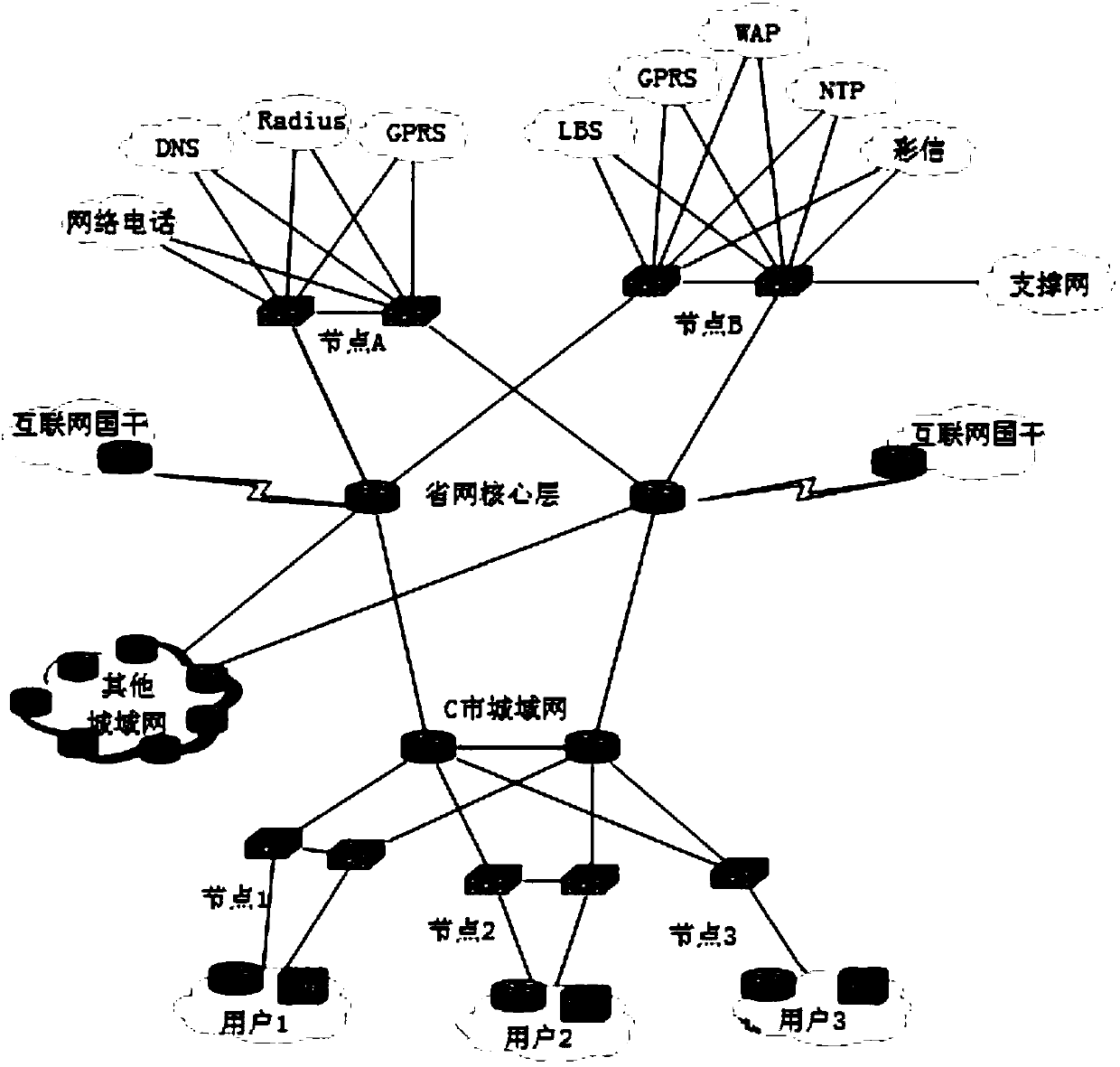
[0034] In step 101, a network state diagram is generated in real time according to the network communication state. The information represented by the nodes in the network state diagram includes hosts, IP addresses, users, etc., and the information represented by the connection lines in the network state diagram includes communication between hosts, user login, IP address switching, etc. In one embodiment, the network state diagram is as figure 2 shown.
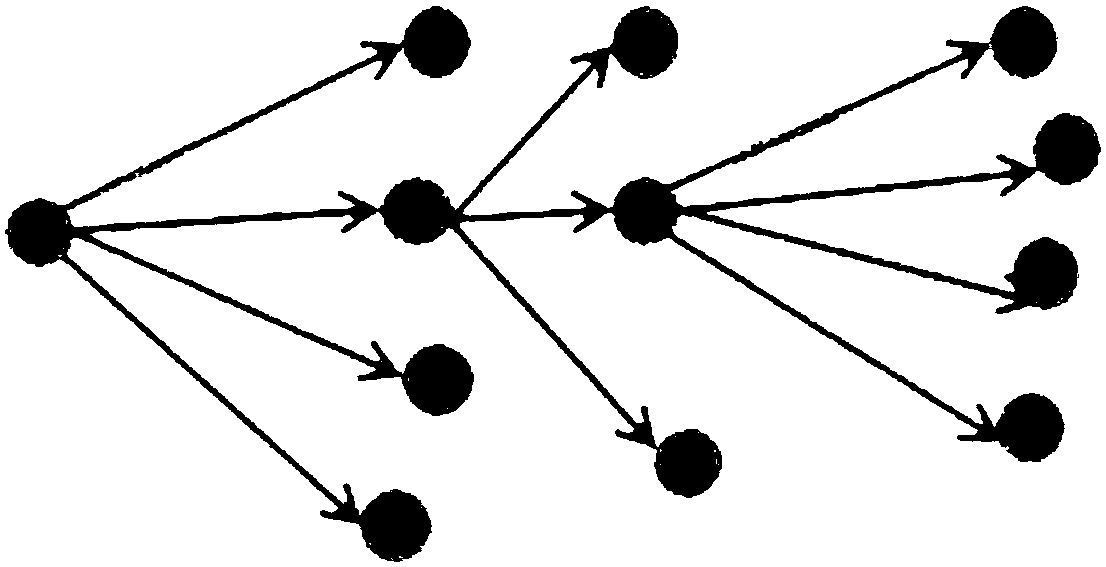
[0035] In step 102, a predetermined characteristic subgraph is matched in the network state diagram, wherein the predetermined characteristic subgraph is a state diagram when an abnormality occurs in the network communication sta...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More