Webshell detection method and device
A detection method and detection device technology, applied in the field of information security, can solve problems such as deficiencies, and achieve the effect of improving the accuracy rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0061] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
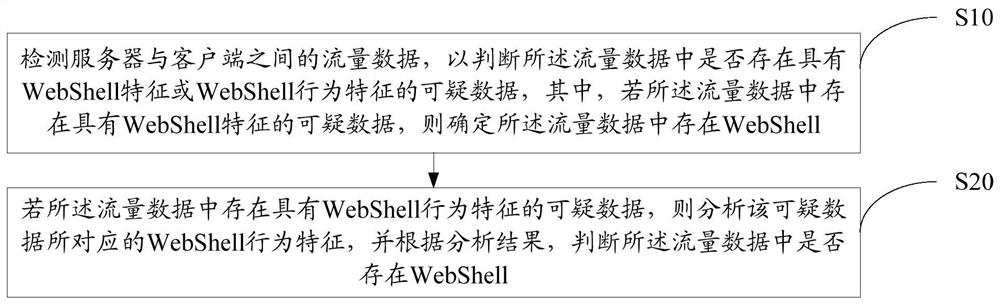
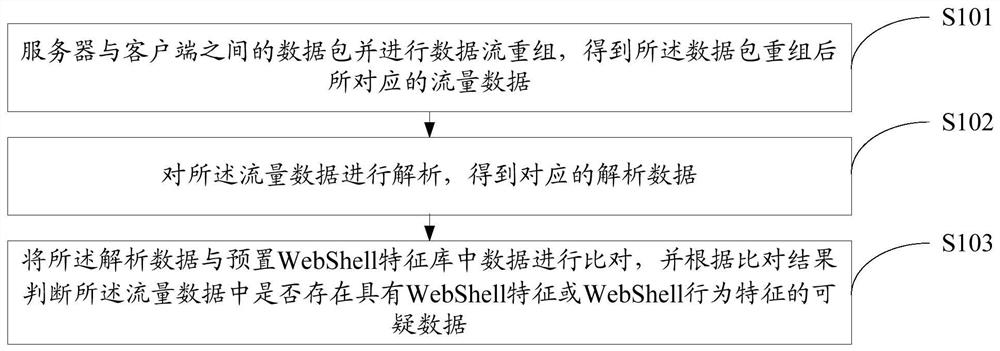
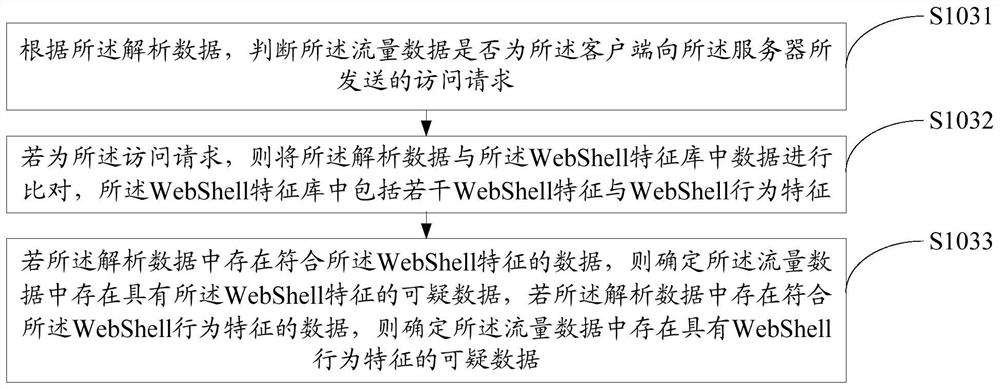
[0062] refer to figure 1 , figure 1 It is a schematic flowchart of the first embodiment of the WebShell detection method of the present invention. In this embodiment, the WebShell detection method includes:
[0063] Step S10, detecting the traffic data between the server and the client to determine whether there is suspicious data with WebShell characteristics or WebShell behavior characteristics in the traffic data, wherein, if there is suspicious data with WebShell characteristics in the traffic data, Then it is determined that WebShell exists in the traffic data;
[0064] WebShells are often overtly interactive. For example, when using WebShell for file management, the general process is: the intruder lists the directories and files on the server through WebShell, and then further decides to download some of th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More