A Verifiable Encrypted Search Method
A search method and search result technology, applied in the field of verifiable encrypted search, to achieve the effect of less communication rounds and less overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The present invention will be described in further detail below in combination with specific embodiments and with reference to the accompanying drawings.
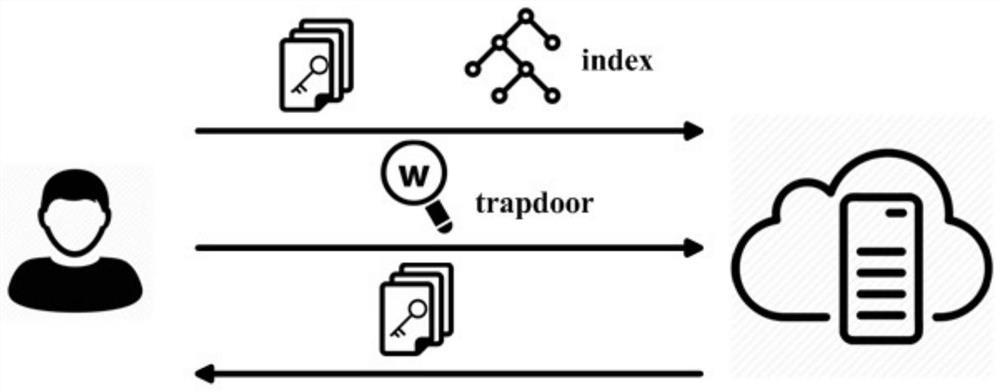
[0030] The system framework of the verifiable encrypted search scheme includes two entities, client and server, where the client uploads the verification index (index) corresponding to its data to the cloud; the cloud server (server) provides storage, search and verification services for the client; after the client searches Verify the search results returned by the cloud server. As follows, before describing the working process of the system, the symbols and the meanings of some concepts that will be used in this specific implementation are given first.
[0031]
[0032] The workflow of the system is defined as follows:
[0033] KGen C (1 k )→{K 1 ,K 2}: It is a probability calculation operation performed by the Client. Its input is a security parameter, and its output is a symmetric key set K 1 ,K 2 .
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More