Trusted execution environment-based key burning system and method
An execution environment and programming system technology, applied in transmission systems, digital transmission systems, and key distribution, can solve problems such as leaked keys, data security threats, and key cracking leaks, to prevent accidental damage and ensure integrity. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] It should be noted that, in the case of no conflict, the following technical solutions and technical features can be combined with each other.
[0035] The specific embodiments of the present invention will be further described below in conjunction with the drawings:
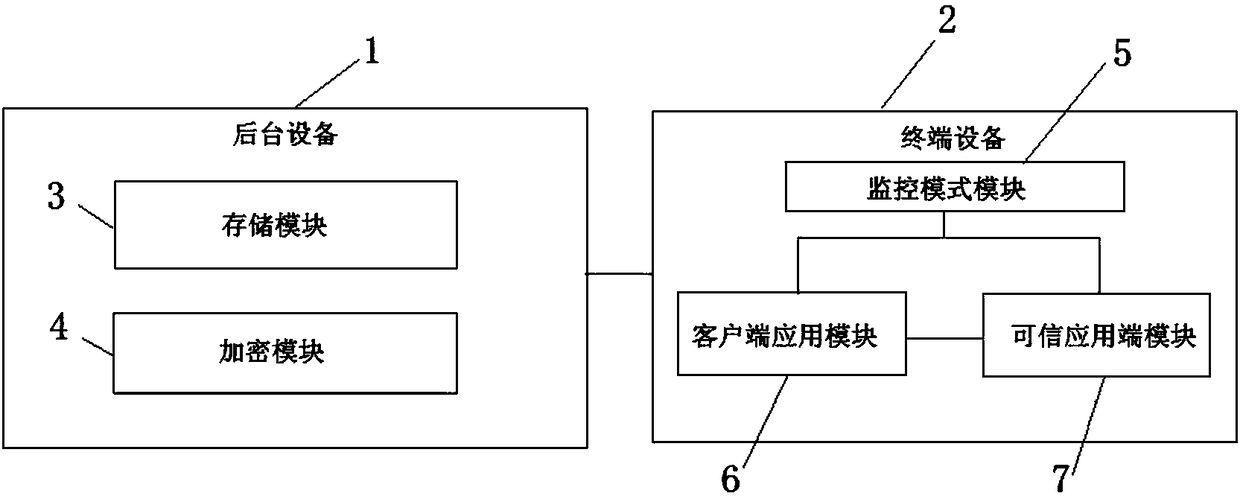
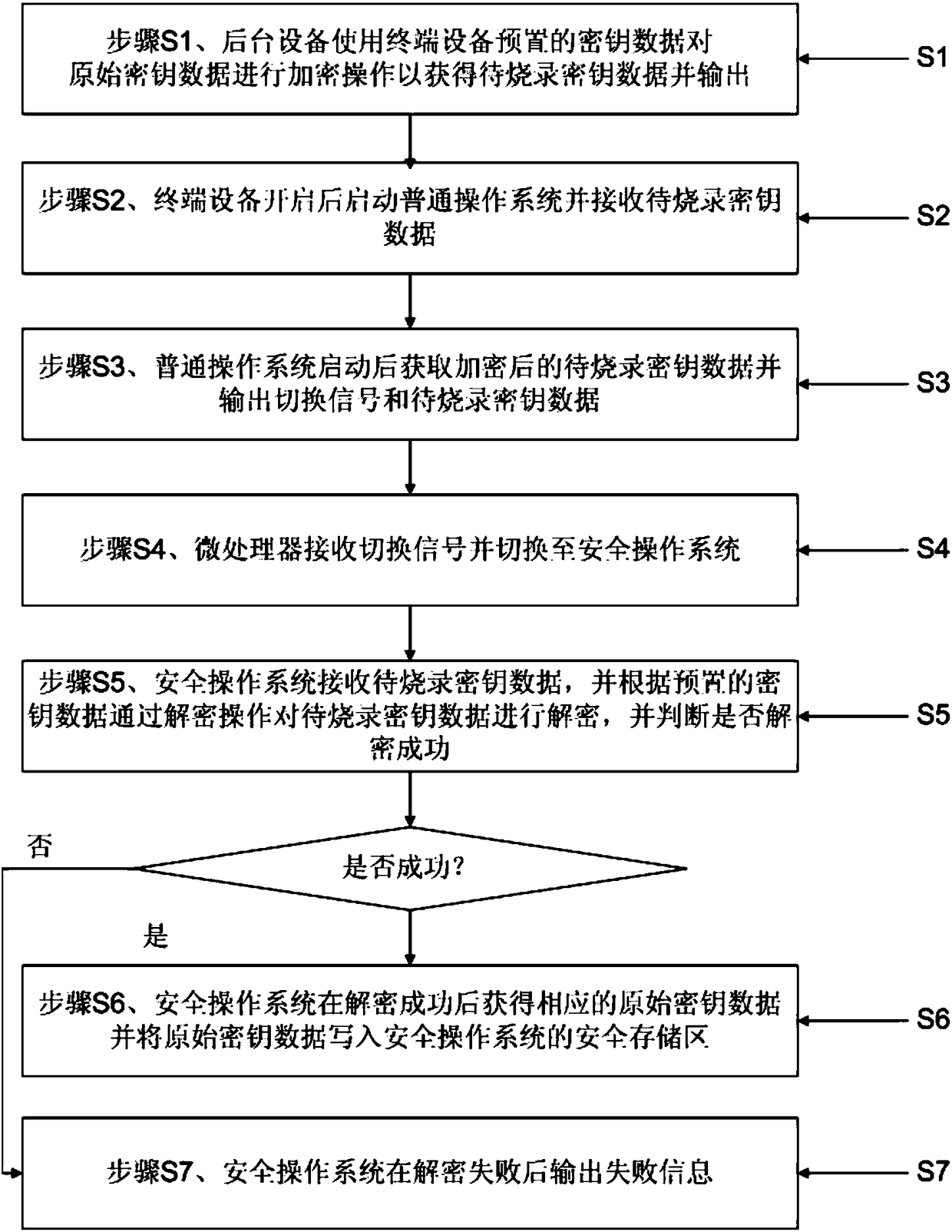
[0036] Such as figure 1 As shown, a key burning system based on a trusted execution environment includes a back-end device 1 and a terminal device 2. The back-end device 1 is used to encrypt original key data to obtain and output the key data to be burned. The above-mentioned terminal device 2 has a microprocessor based on TrustZone technology. The physical core of the above-mentioned microprocessor is divided into a virtual security core and an ordinary core. The above-mentioned microprocessor provides a trusted execution environment and a rich execution environment. The above-mentioned trusted execution environment provides A secure operating system based on the aforementioned secure core, the aforementioned...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More