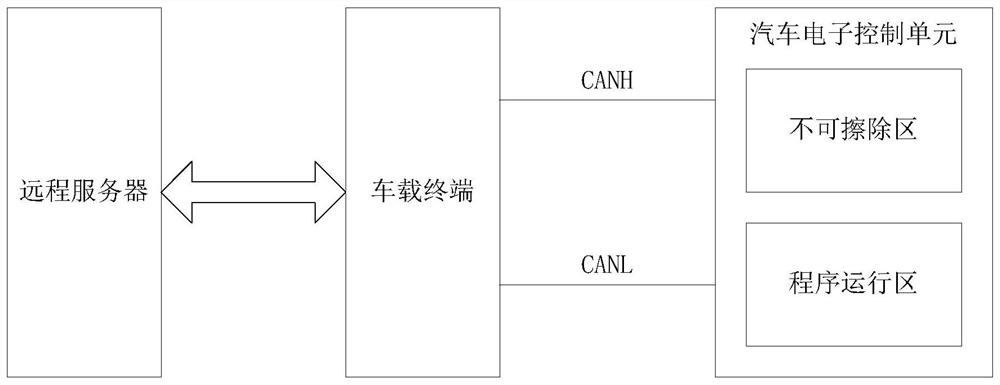
Vehicle program file encryption method and system
A technology of program files and encryption methods, which is applied in the direction of transmission systems, digital transmission systems, encryption devices with shift registers/memory, etc., can solve the problem of increasing the failure of electronic control units, remote servers or electronic control units being hacked, program files Easy to be tampered with, increase data loss and leakage, etc., to reduce the risk of encryption being cracked, reduce the possibility of being tampered with, and reduce the effect of data loss and leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
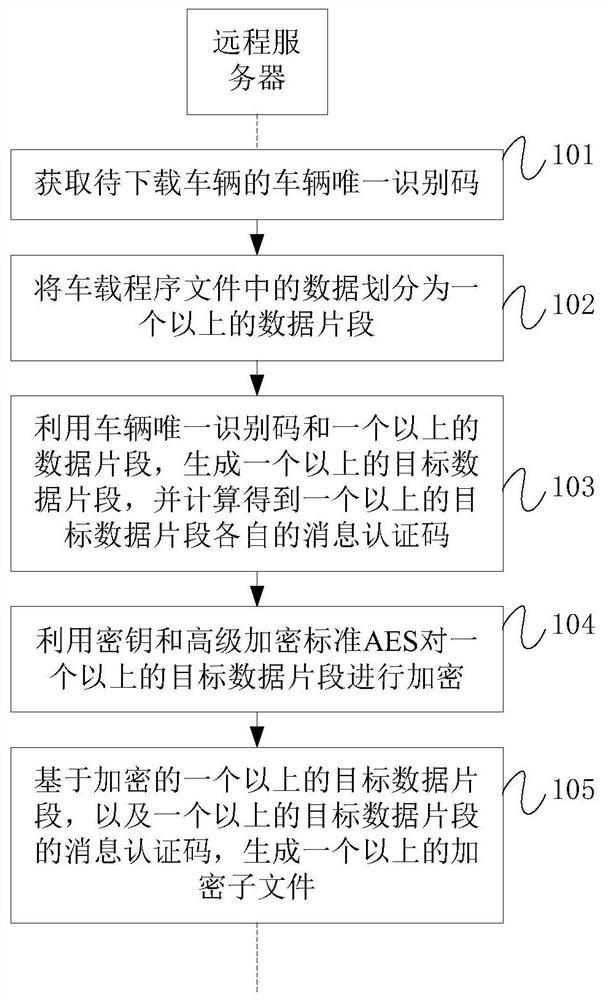
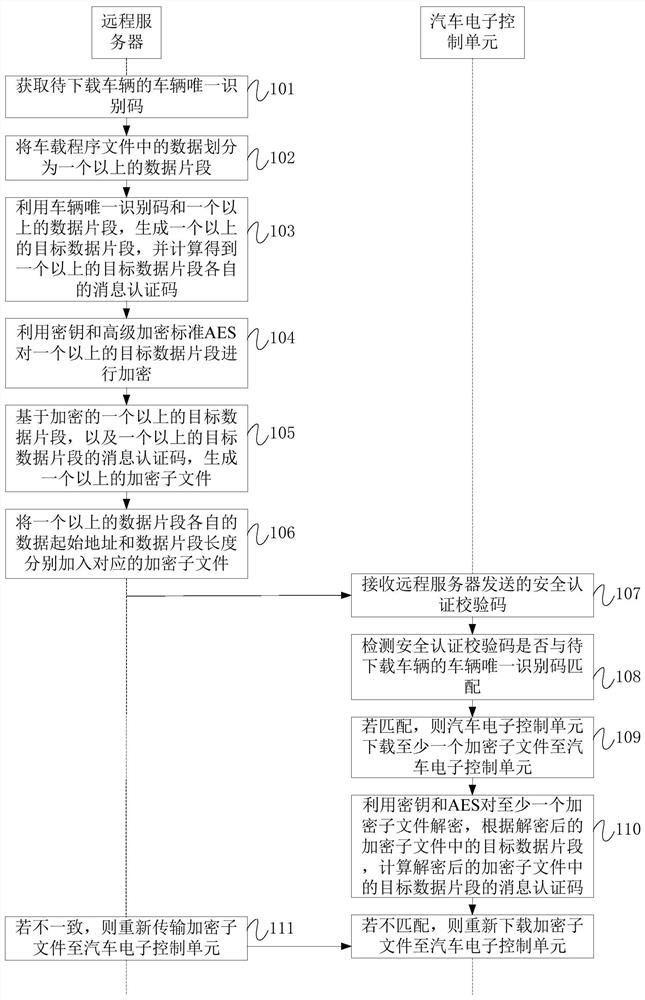
Method used
Image
Examples
Embodiment Construction
[0018] Features and exemplary embodiments of various aspects of the invention will be described in detail below. In the following detailed description, numerous specific details are set forth in order to provide a thorough understanding of the present invention. It will be apparent, however, to one skilled in the art that the present invention may be practiced without some of these specific details. The following description of the embodiments is only to provide a better understanding of the present invention by showing examples of the present invention. The present invention is by no means limited to any specific configurations and algorithms presented below, but covers any modification, substitution and improvement of elements, components and algorithms without departing from the spirit of the invention. In the drawings and the following description, well-known structures and techniques have not been shown in order to avoid unnecessarily obscuring the present invention.
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More