Phishing application detection method and device
The technology of a detection device and detection method, which is applied in the field of information security, can solve the problems of low detection efficiency and inconvenience, and achieve the effects of high detection efficiency, convenient implementation, and high real-time detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
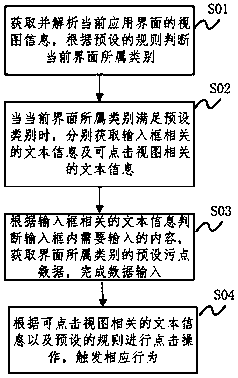
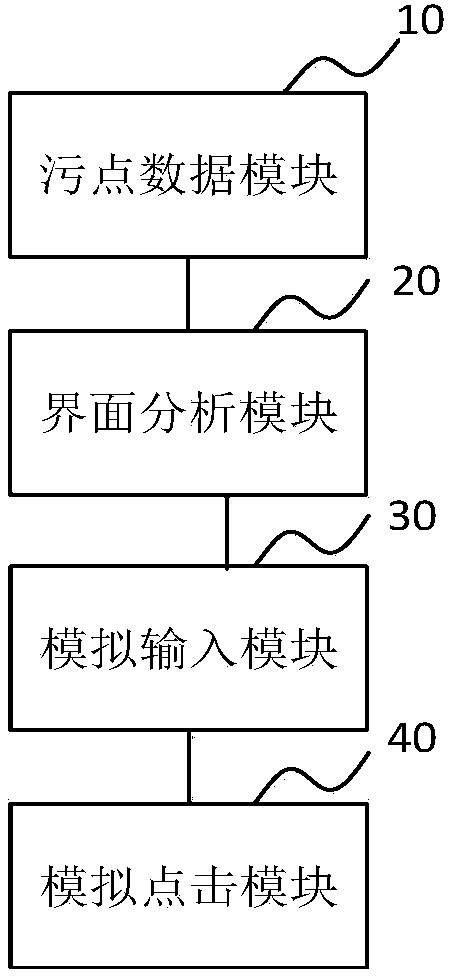
Method used
Image
Examples
Embodiment Construction
[0025] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
[0026] Although the steps in the present invention are arranged with labels, they are not used to limit the order of the steps. Unless the order of the steps is clearly stated or the execution of a certain step requires other steps as a basis, the relative order of the steps can be adjusted.
[0027] At present, there are various automated testing frameworks under the Android system, such as uiautomator and appium. Any framework that can meet the relevant functions in the solution can be used to implement the solution. The specific implementation of this solution is described here with the framework of uiautomator.
[0028] The application interface in the Android system contains a series of views, including views with container types (that is, the views contain...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More