Method for carrying out classification detection on network attack behaviors through utilization of machine learning technology
A network attack and machine learning technology, applied in the field of information security, can solve problems such as active monitoring and complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0071] The technical solutions of the present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
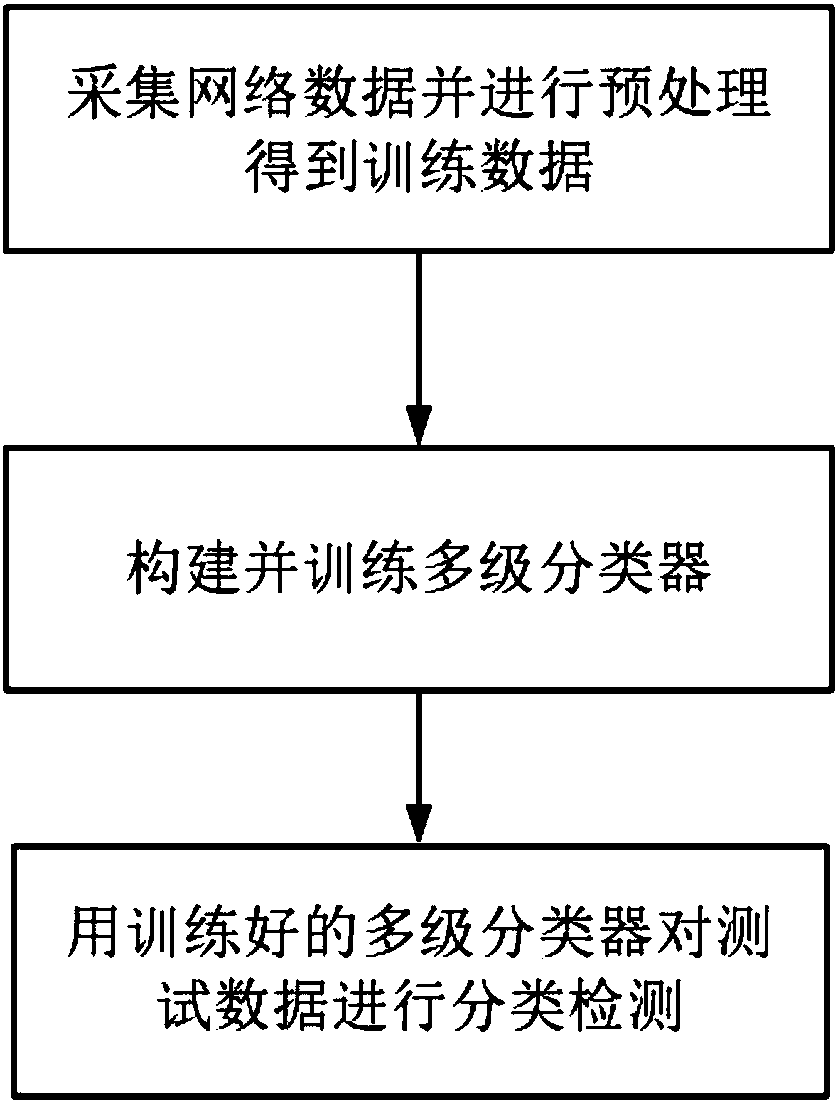
[0072] Using a method of classifying and detecting network attack behaviors proposed by the present invention to classify network data, the operation process is as follows figure 1 As shown, the specific steps are:
[0073] Step 1. Collect network data and perform preprocessing to obtain training data.
[0074] The KDD CUP99 data is obtained, and 10% sampling is performed on the KDD CUP99 data set as the network data of this embodiment.
[0075] The training data is divided into normal (Normal) data and attack data; the attack data is further divided into 4 categories according to different attack types. The number of each type of training data is not less than 3000. The attack types are: Denial of Service (DOS), Monitoring or Probing (Probing), Remote Unauthorized Access (R2L) and Unauthorized Elevation of User Ri...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More