Attack surface modeling method and device for redundant information system
A technology of redundant information and modeling methods, applied in the field of network security, can solve the problems of being unable to fully and effectively adapt to redundant complex structural systems, and unable to effectively measure the security of redundant complex structural systems.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
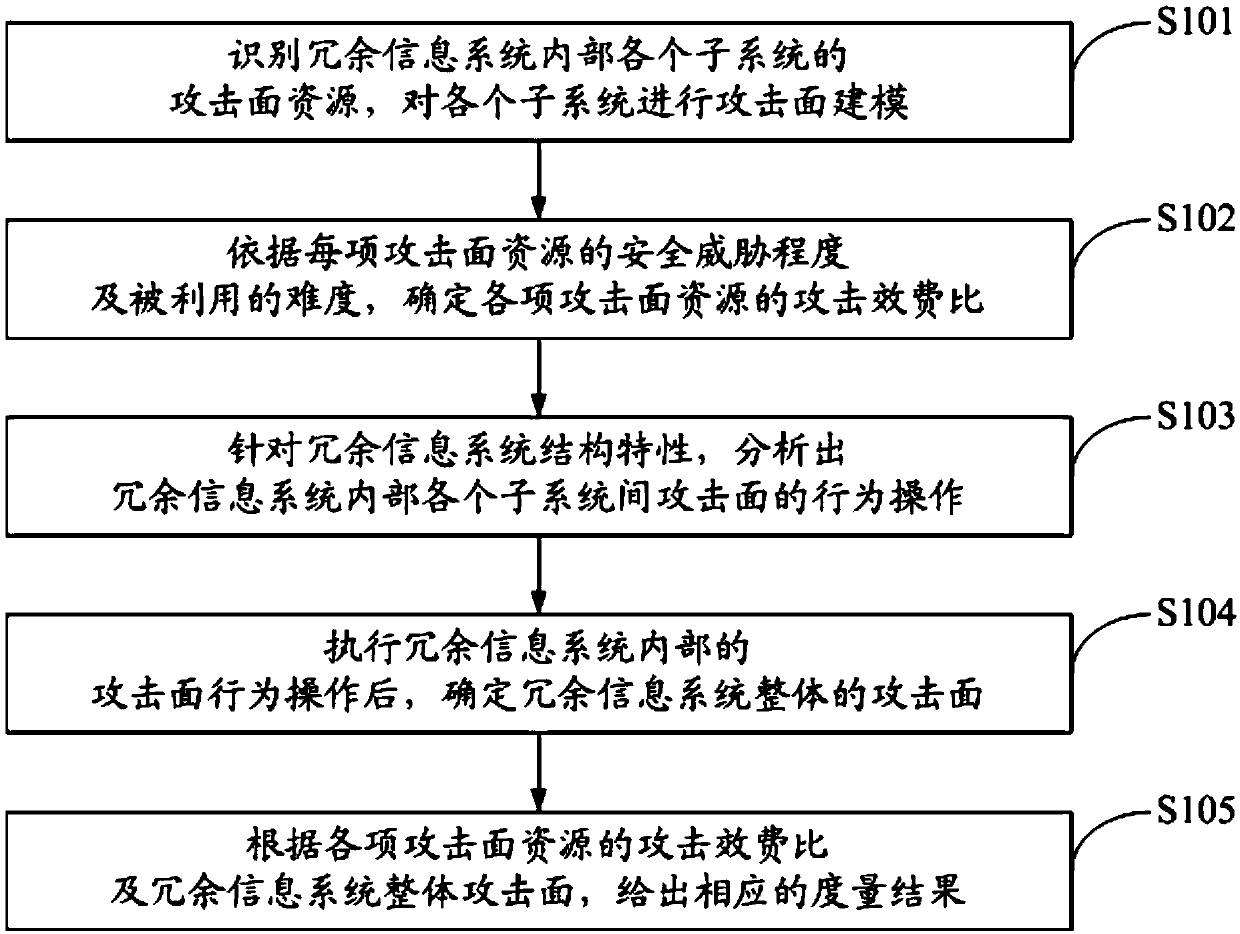
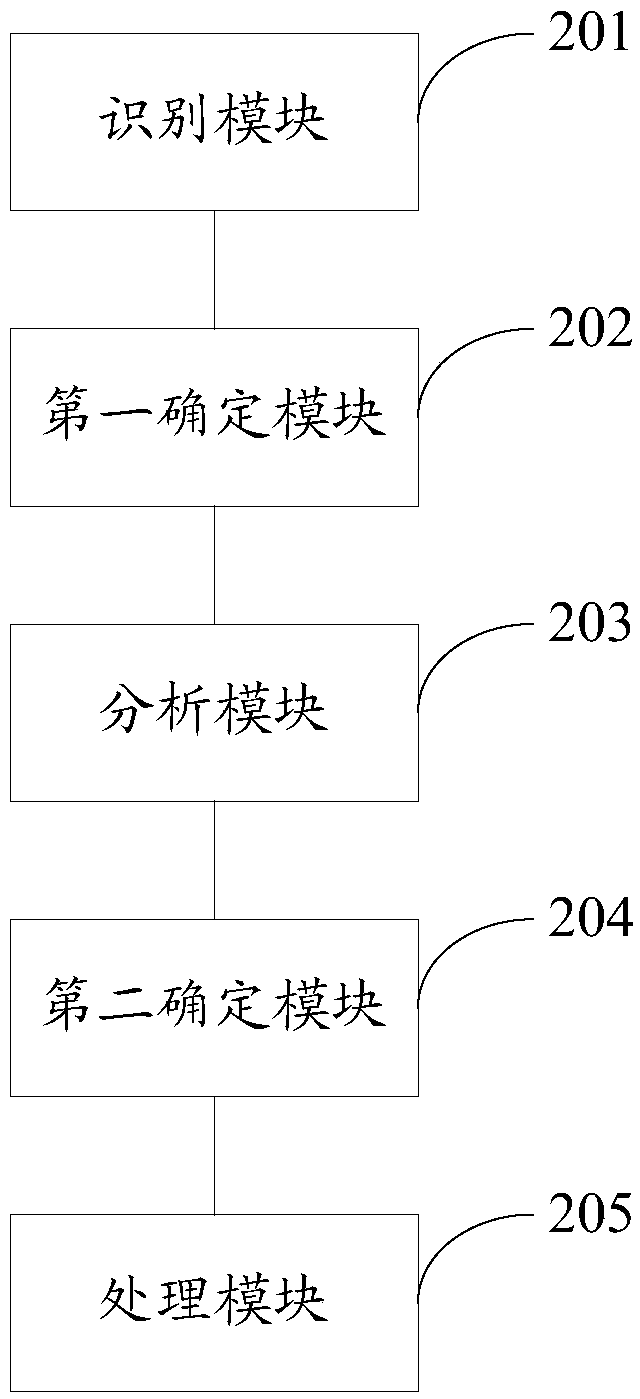
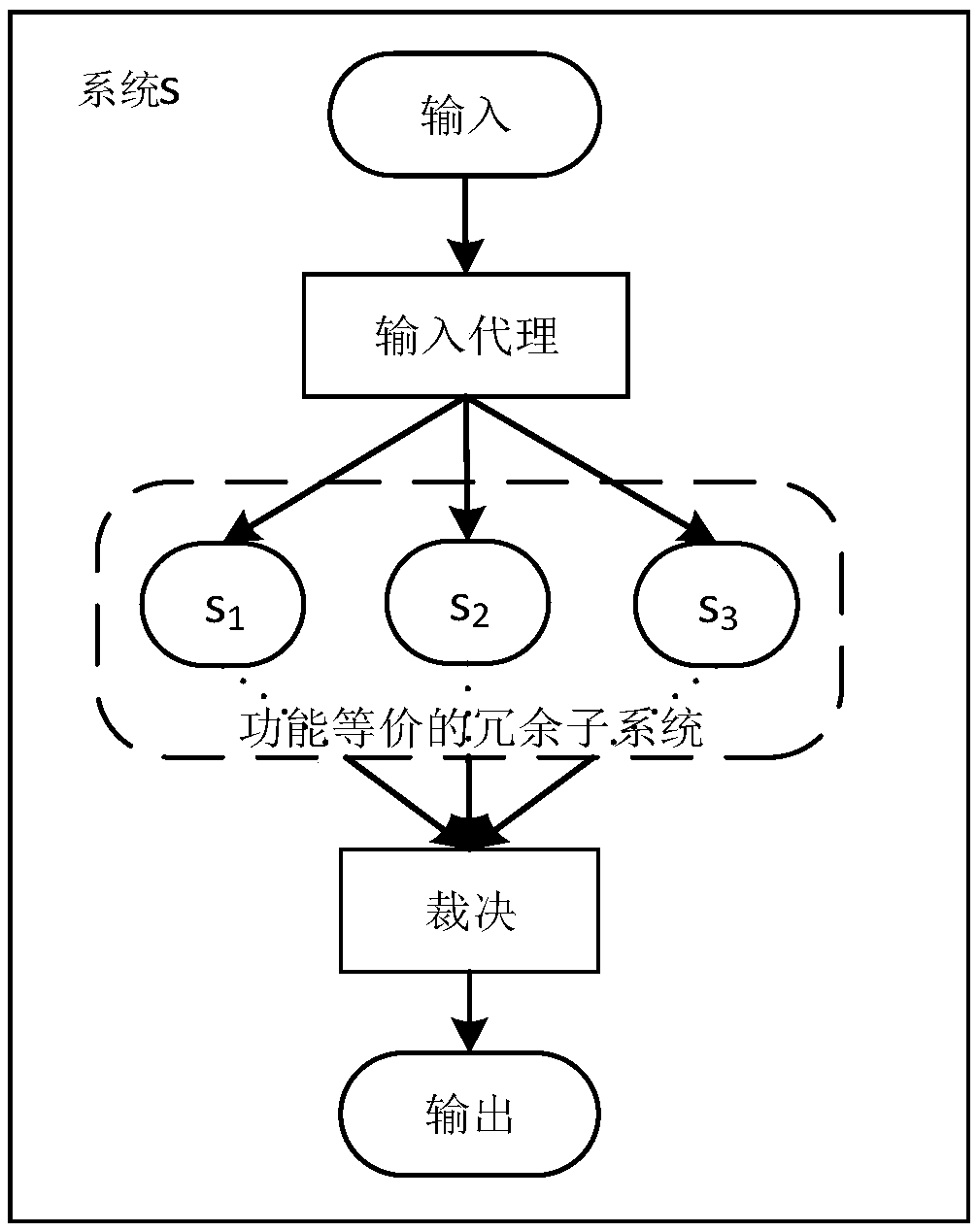
[0037] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0038] The embodiment of the present application is applied to the attack surface modeling of the Web application information system using the dissimilarity redundancy technology. The Web application provides the function of uploading files, and the name of the uploaded file will be encrypted and stored in the database. There are PHP file upload vulnerabilities and SQL injection vulnerabilities in the application. In the embodiment of this application, the attack surface modeling of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More