A method and system for prevent blackmail virus from secondary encrypting host document
A secondary encryption and virus technology, applied in the field of information security, can solve problems such as inability to achieve effective defense, unrepairable operating system and host files, loss, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
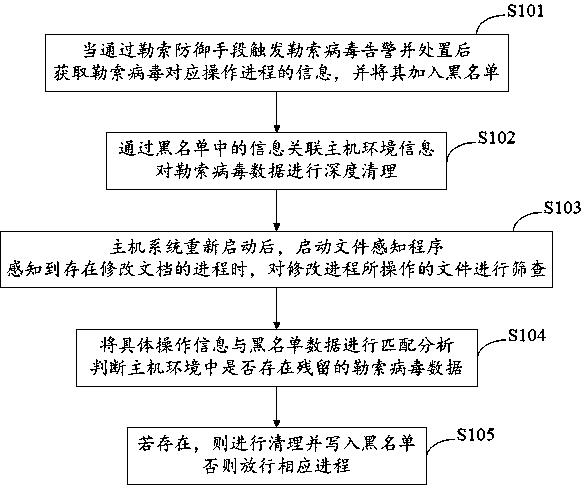
[0029] The present invention provides an embodiment of a method for preventing ransomware from re-encrypting host files, such as figure 1 shown, including:
[0030] S101: After the ransomware alarm is triggered by means of ransomware defense and dealt with, obtain information on the operation process corresponding to the ransomware, and add it to the blacklist;
[0031] S102: Correlate host environment information with the information in the blacklist, and perform in-depth cleaning of the ransomware data;
[0032] S103: After the host system restarts, start the file sensing...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More