Operation behavior interception method and device, storage medium and electronic device
A technology of behavior and operation authority, applied in the field of information network security, can solve problems such as undiscovered solutions, achieve the effect of reducing risks and losses, and solving weak equipment security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
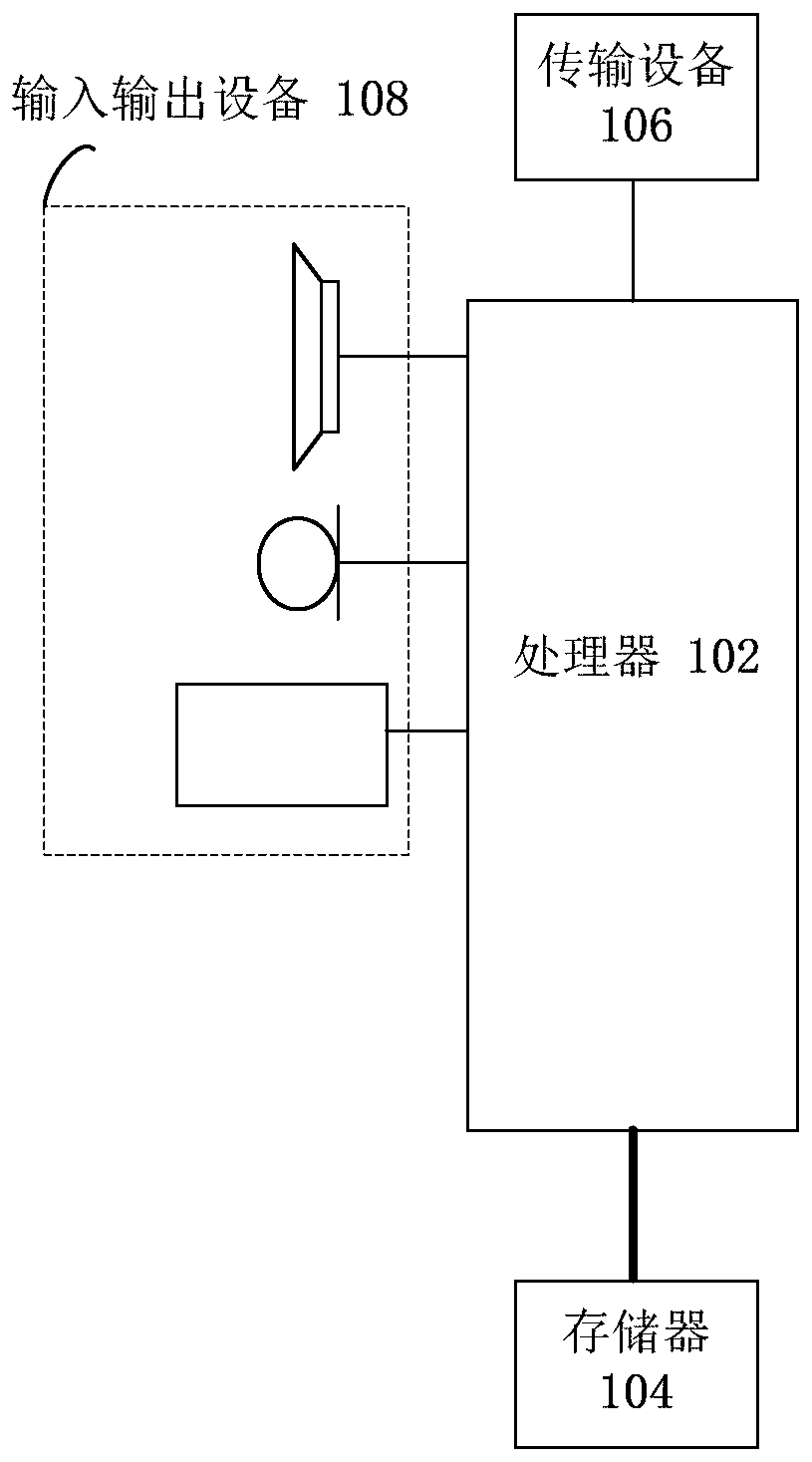
[0037] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, a server or a similar computing device. Take running on the terminal as an example, figure 1 It is a block diagram of the hardware structure of an intercepting terminal of an operation behavior in the embodiment of the present invention. Such as figure 1 As shown, the terminal 10 may include one or more ( figure 1 Only one is shown in ) processor 102 (processor 102 may include but not limited to processing devices such as microprocessor MCU or programmable logic device FPGA) and memory 104 for storing data. Optionally, the above-mentioned terminal can also be A transmission device 106 for communication functions and an input and output device 108 are included. Those of ordinary skill in the art can understand that, figure 1 The shown structure is only for illustration, and does not limit the structure of the above-mentioned terminal. ...
Embodiment 2
[0226] In this embodiment, a device for intercepting operation behaviors is also provided, which may be a terminal or a server. The device is used to implement the above embodiments and preferred implementation modes, and those that have already been explained will not be repeated. As used below, the term "module" may be a combination of software and / or hardware that realizes a predetermined function. Although the devices described in the following embodiments are preferably implemented in software, implementations in hardware, or a combination of software and hardware are also possible and contemplated.
[0227] Figure 9 is a structural block diagram of an intercepting device for operating behavior according to an embodiment of the present invention, which can be applied in a client or a server, such as Figure 9 As shown, the device includes: distribution module 90, monitoring module 92, interception module 94, wherein,
[0228] Assignment module 90, configured to assign ...
Embodiment 3
[0237] An embodiment of the present invention also provides a storage medium, in which a computer program is stored, wherein the computer program is set to execute the steps in any one of the above method embodiments when running.
[0238] Optionally, in this embodiment, the above-mentioned storage medium may be configured to store a computer program for performing the following steps:
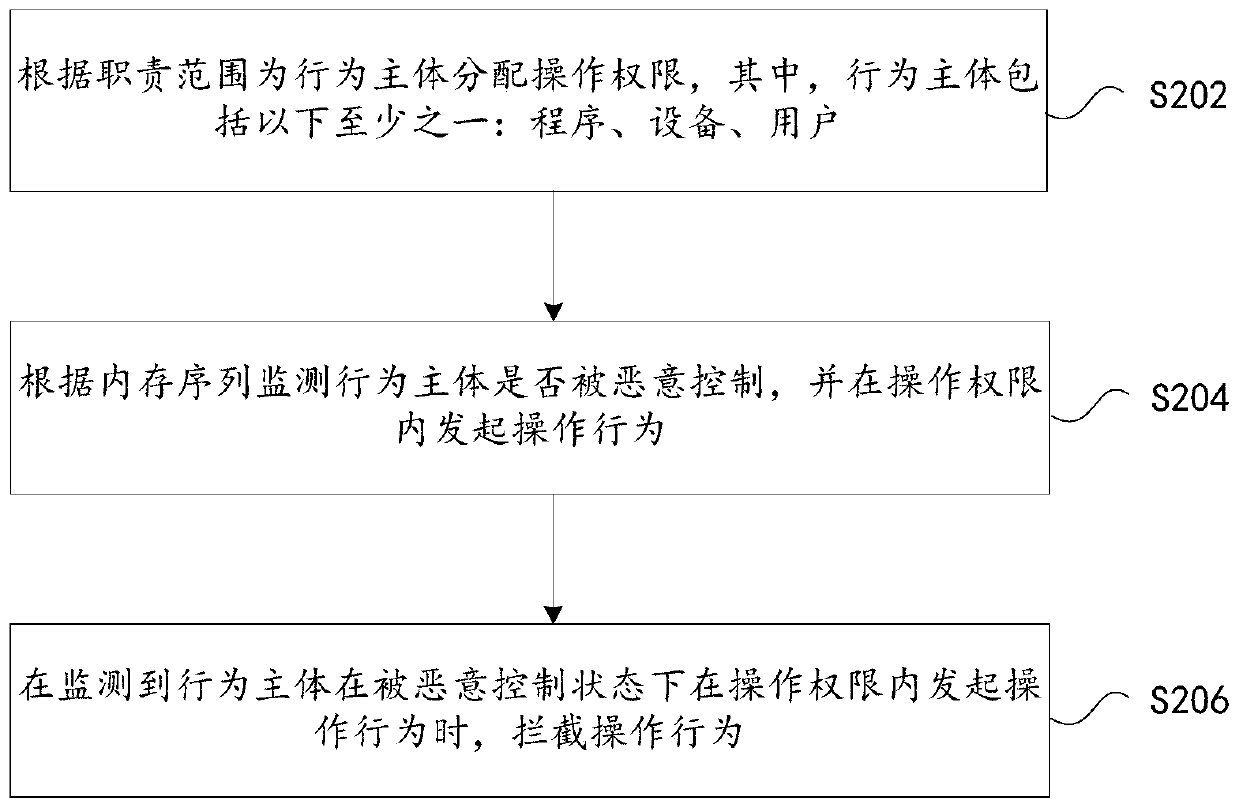
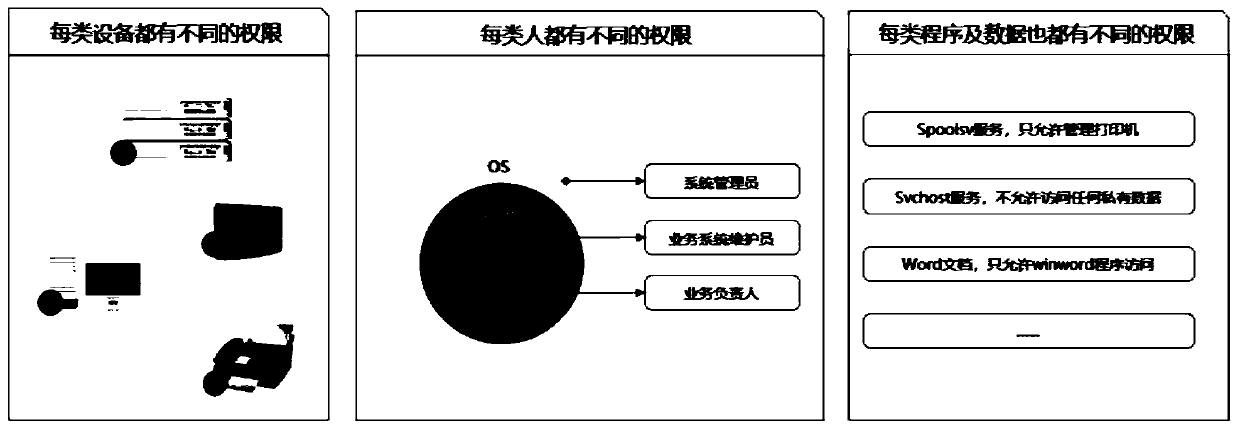
[0239] S1. Assigning operation rights to the behavior subject according to the scope of duties, wherein the behavior subject includes at least one of the following: programs, equipment, and users;
[0240] S2, monitoring whether the subject of the behavior is maliciously controlled according to the memory sequence, and initiating an operation within the operation authority;
[0241] S3. Intercepting the operation behavior when it is detected that the behavior subject initiates the operation behavior within the operation authority under malicious control.
[0242] Optionally, in this embodimen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More