System and method for implementing trusted computing based on lsm and system call interception
A technology of call interception and trusted computing, applied in the field of localized terminal security, which can solve the problems of easy omission, complicated implementation of system calls, and coarse granularity of system call auditing.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] In order to make the purpose, content, and advantages of the present invention clearer, the specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments.
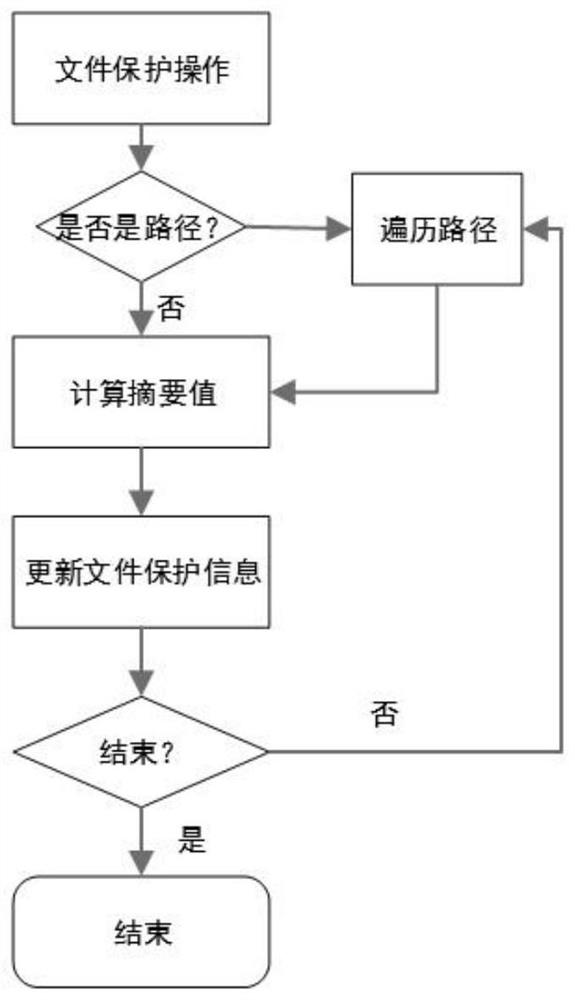
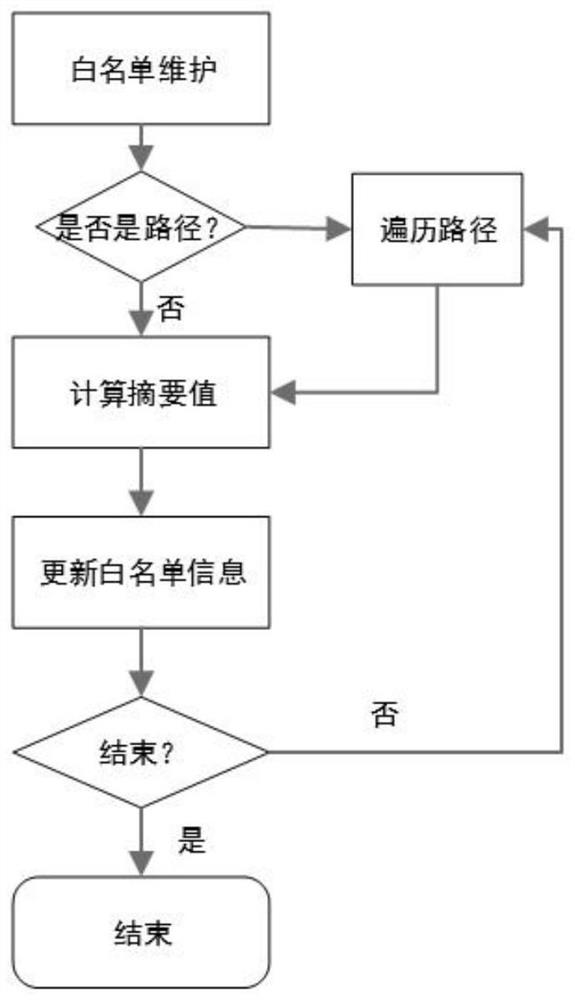
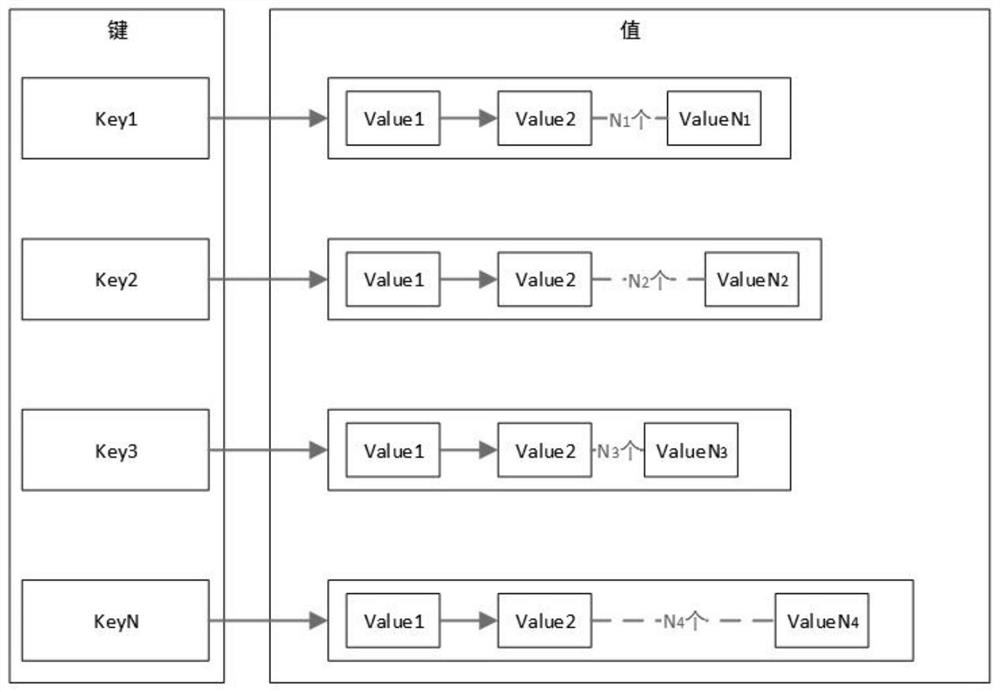
[0048]A domestic linux operating system provided by the present invention is based on the LSM and the system call intercepting trusted computing implementation system, which includes: a kernel mode module, a user mode service module, and an interface module. Wherein, the kernel state module is in the kernel state of the operating system, and is used to intercept operating system actions by using LSM (linux security module) in combination with system call technology, including startup programs and file read and write operations, and is also used to serve according to the user state. The decision-making content of the module executes permission or prohibition operations; the user state service module is located in the use...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More