Malicious code shell identification and static unshelling method and system
A malicious code and code technology, applied in the field of Internet information security, can solve problems such as uncollected and undiscovered data, achieve efficient and convenient identification and analysis, improve accuracy, and realize the effect of system automation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] The present invention will be described in detail below in conjunction with specific embodiments. The following examples will help those skilled in the art to further understand the present invention, but do not limit the present invention in any form. It should be noted that those skilled in the art can make several changes and improvements without departing from the concept of the present invention. These all belong to the protection scope of the present invention.
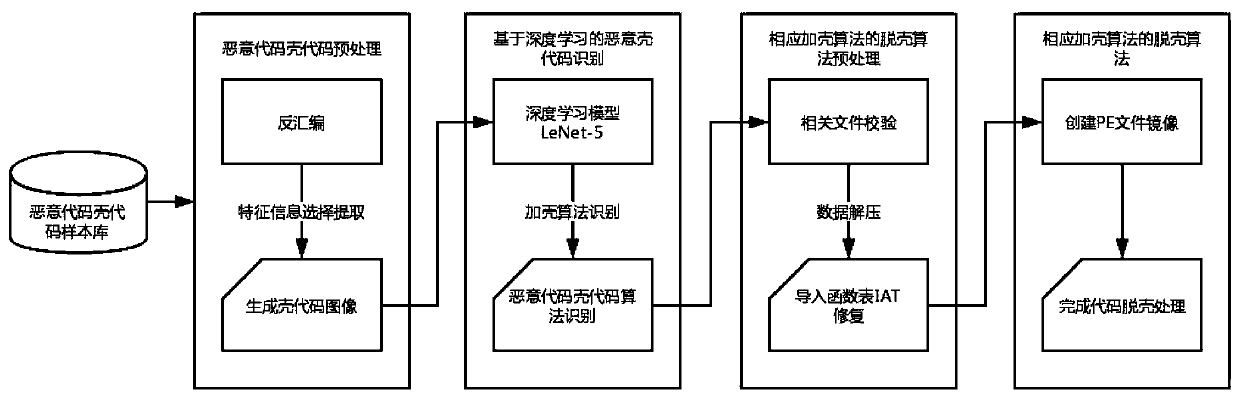
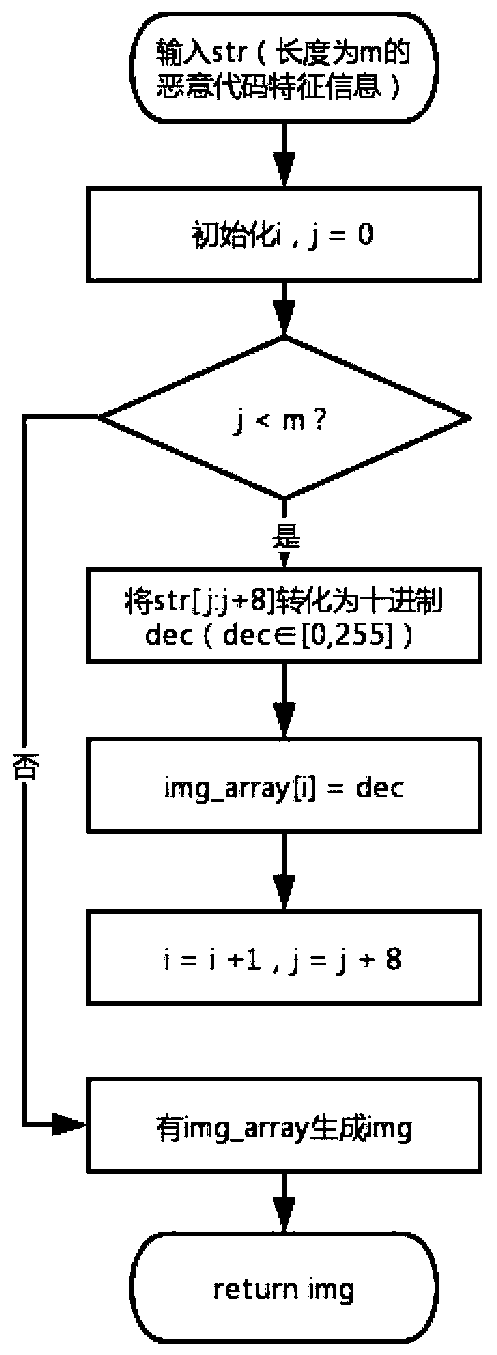
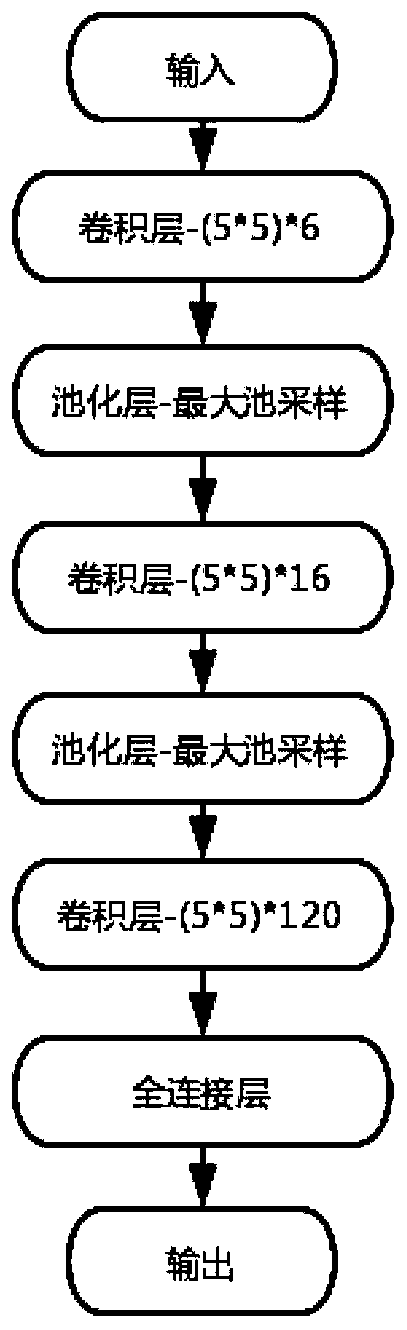
[0039] Aiming at the above-mentioned deficiencies in the prior art, the present invention provides a malicious code shell code identification method and a static unpacking method. The method uses a relatively mature deep neural network to complete an available efficient and accurate malicious code shell code identification and repair the system. The system uses a malicious code shell code visualization algorithm to map the shell code into a grayscale image, and transforms the identification problem of t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More