Application-based service security system and method
A security system and business technology, applied in the field of information security, can solve problems such as low transaction security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
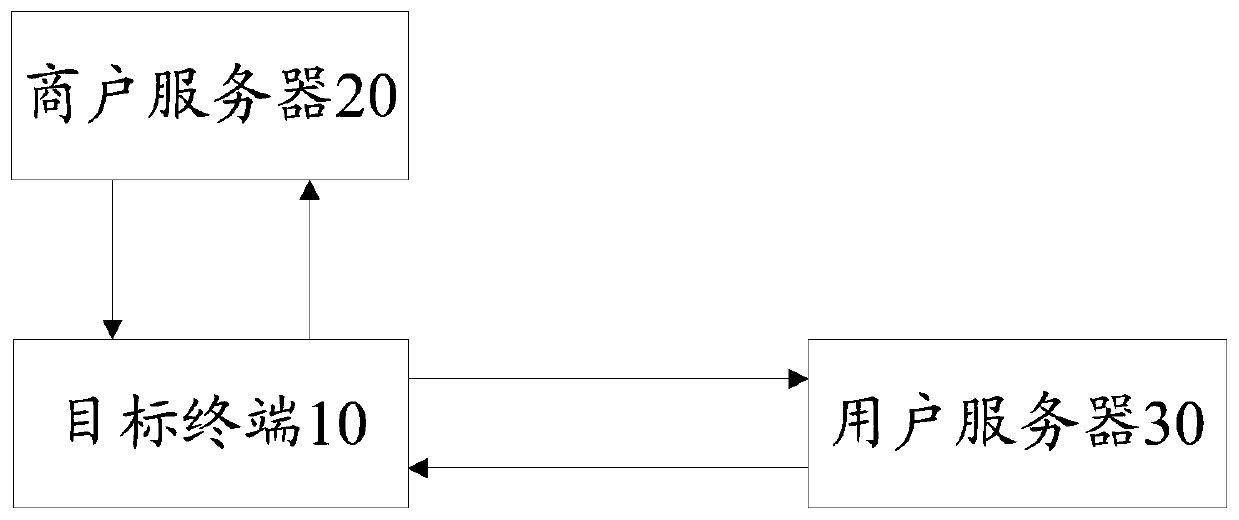
[0058] refer to figure 1 , figure 1 It is a structural block diagram of the first embodiment and the second embodiment of the application-based business security system of the present invention.
[0059] In this embodiment, the application-based business security system includes: a target terminal 10, a merchant server 20 and a user server 30;
[0060] The target terminal 10 is configured to obtain a request message and a session token, encrypt the request message and the session token according to a first preset encryption rule according to a first random key, and obtain a message token Encrypt data, and send the message token encrypted data to the merchant server 20.
[0061] It should be understood that the target terminal 10 may be an electronic device such as a smart phone, a personal computer, or a desktop co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More