Visual attack and defense graph generation method and device, computer equipment and storage medium
A technology for generating devices and computer programs, applied in electrical components, transmission systems, platform integrity maintenance, etc., and can solve problems such as low generation efficiency of attack and defense diagrams
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are some of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
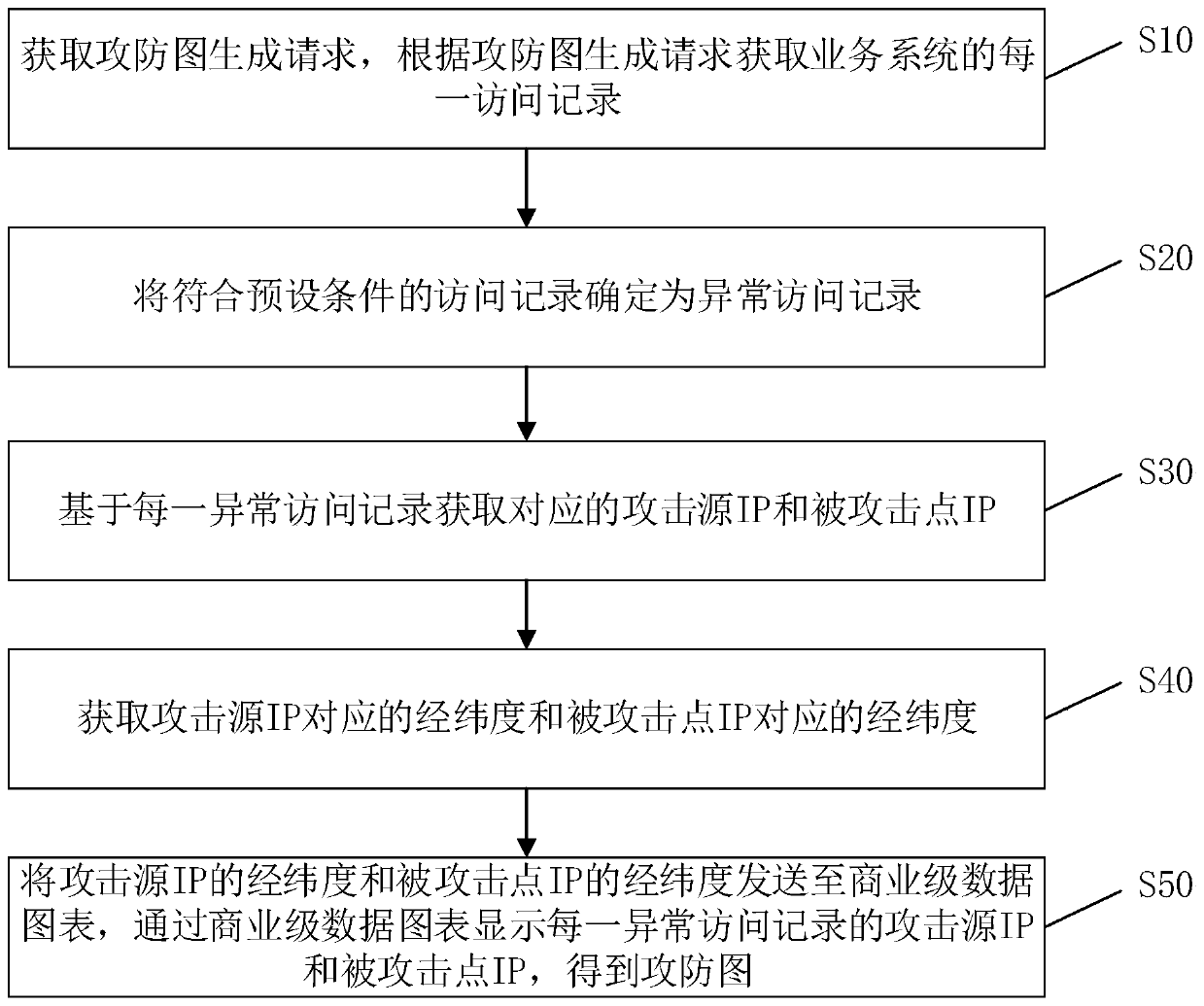
[0034] The visual attack and defense map generation method provided by this application can be applied in such as figure 1 In the application environment, in which, the client communicates with the server through the network, the server obtains the attack and defense map generation request through the client, and obtains each access record of the business system according to the attack and defense map generation request; access records that meet the pre...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More