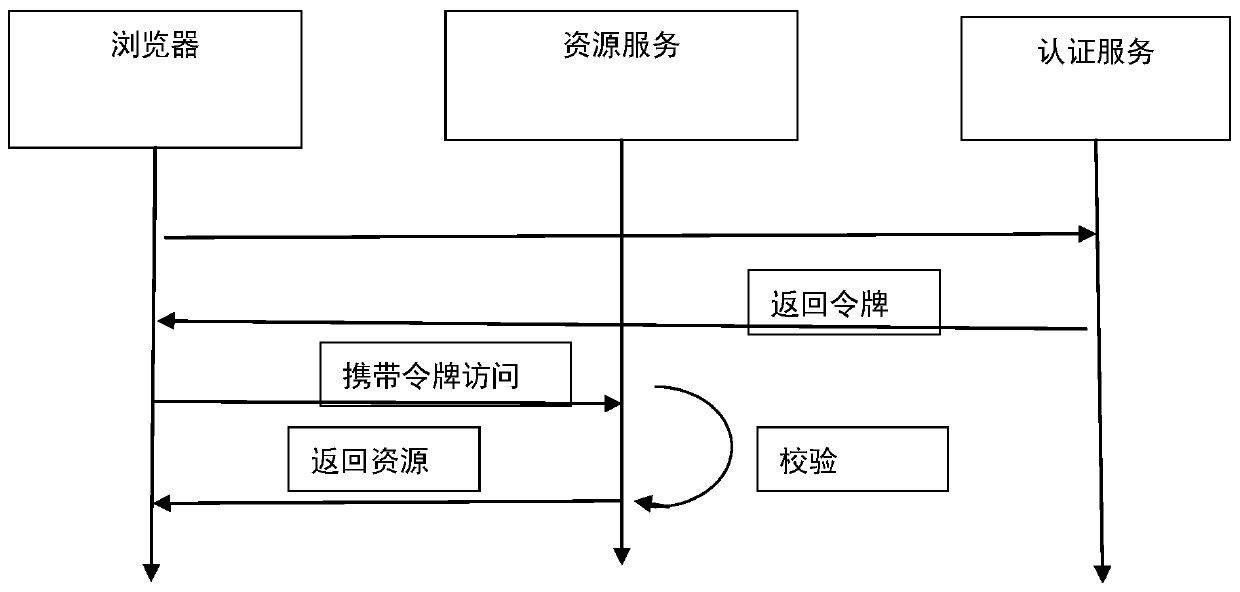
User authentication system based on oauth2 protocol
A user authentication and user technology, applied in the field of user authentication systems based on the oauth2 protocol, can solve problems such as security risks and hinder the development of cloud computing, and achieve the effects of reducing pressure, facilitating judgment, and simplifying repetition.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
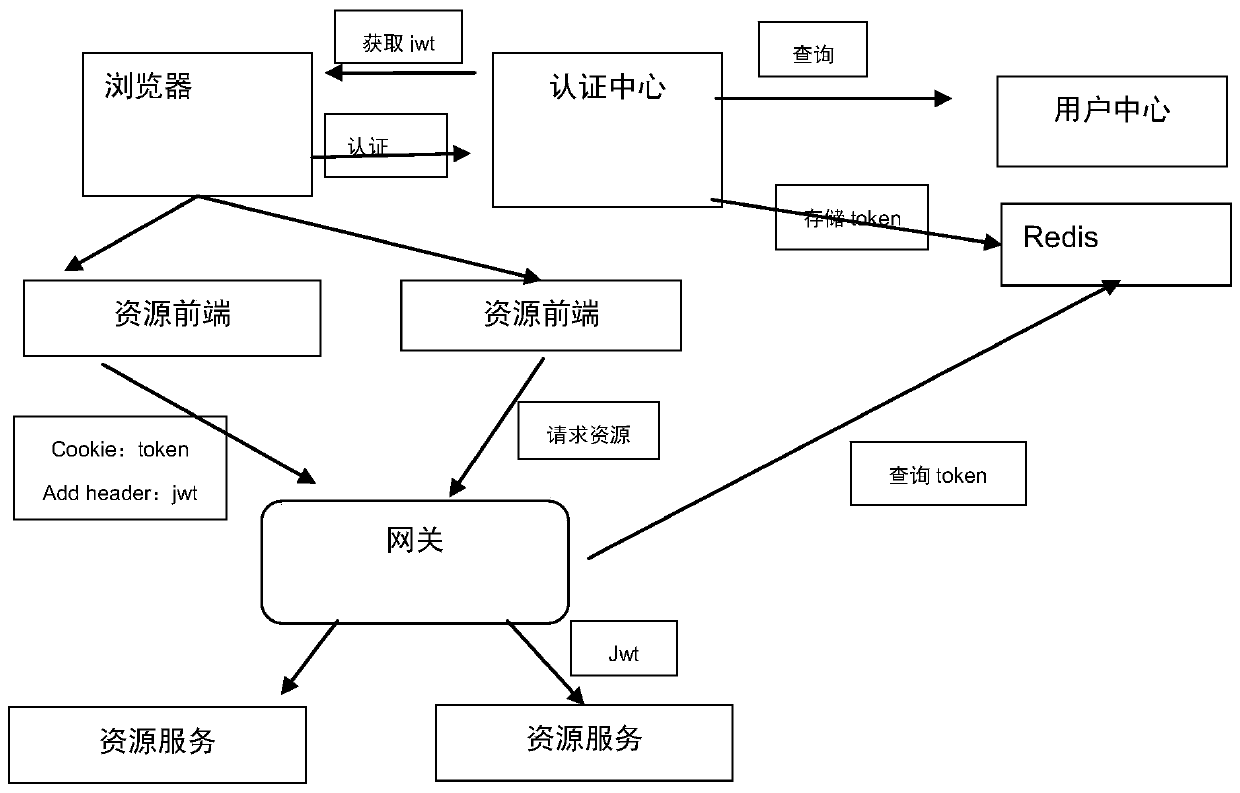
[0041] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the drawings in the embodiments of the present invention. Obviously, the described embodiments It is a part of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative work belong to the protection of the present invention. scope.
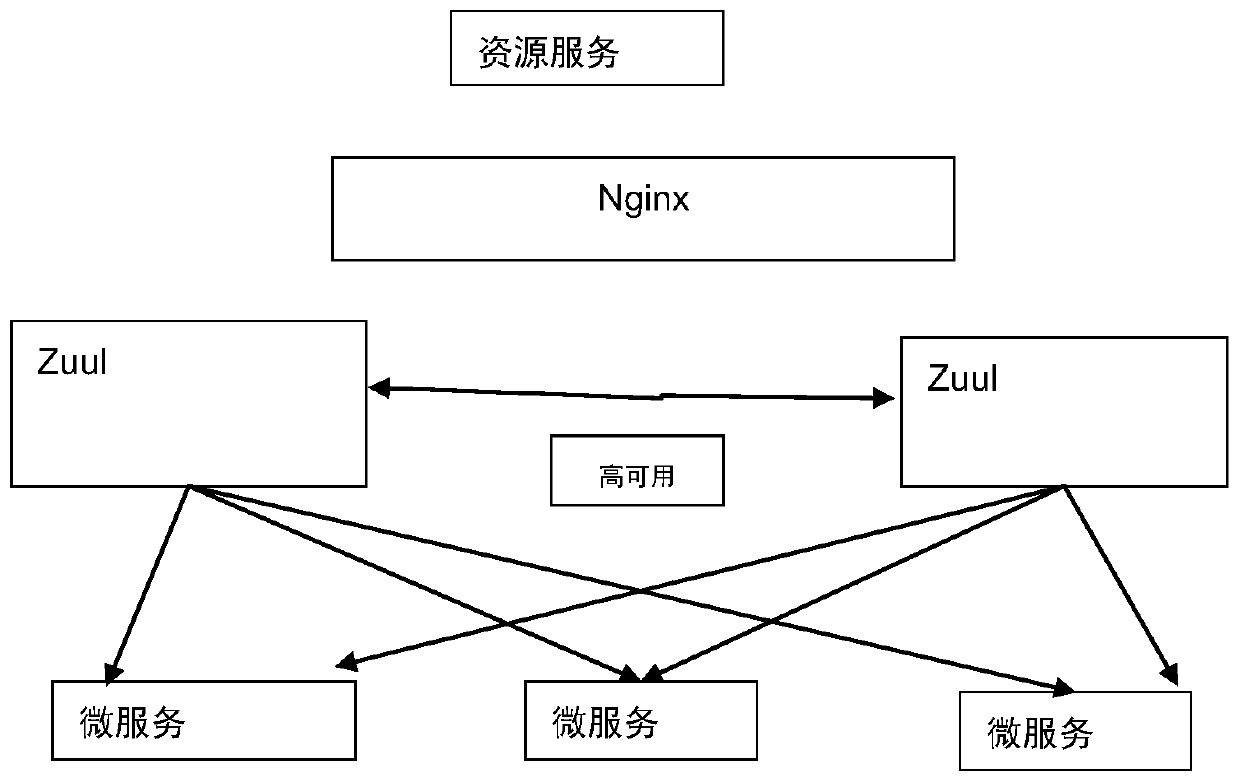
[0042] This application includes a user authentication center module, a Redis token storage module, a user center module, and a service gateway module. Through these modules, the risk of data leakage can be reduced, and at the same time, the pressure on server access can be reduced.
[0043] The main functions of each module are as follows:
[0044] Us...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More