A data security protection method, device and service equipment
A technology for data security and service equipment, applied in the field of data processing
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
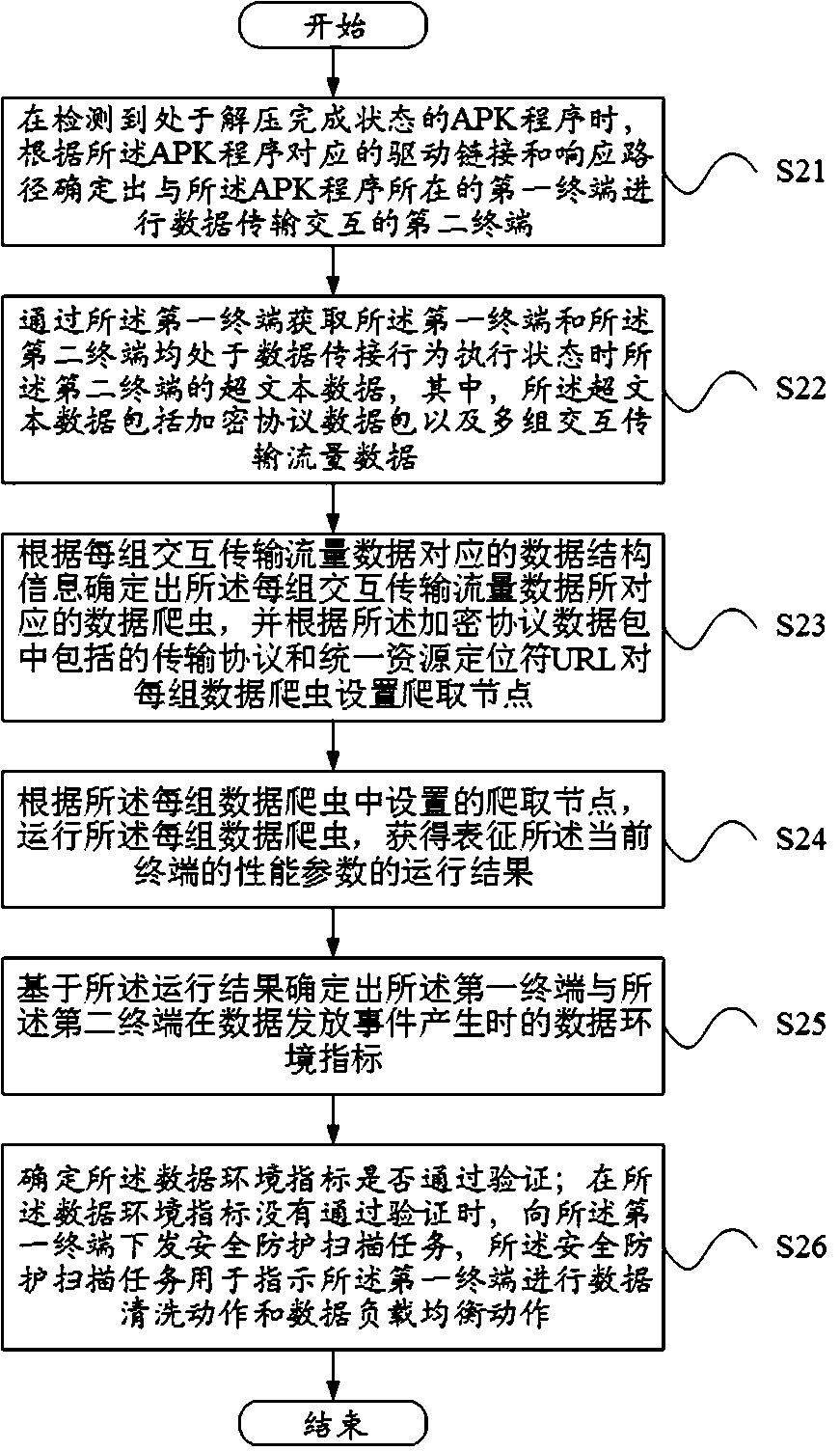
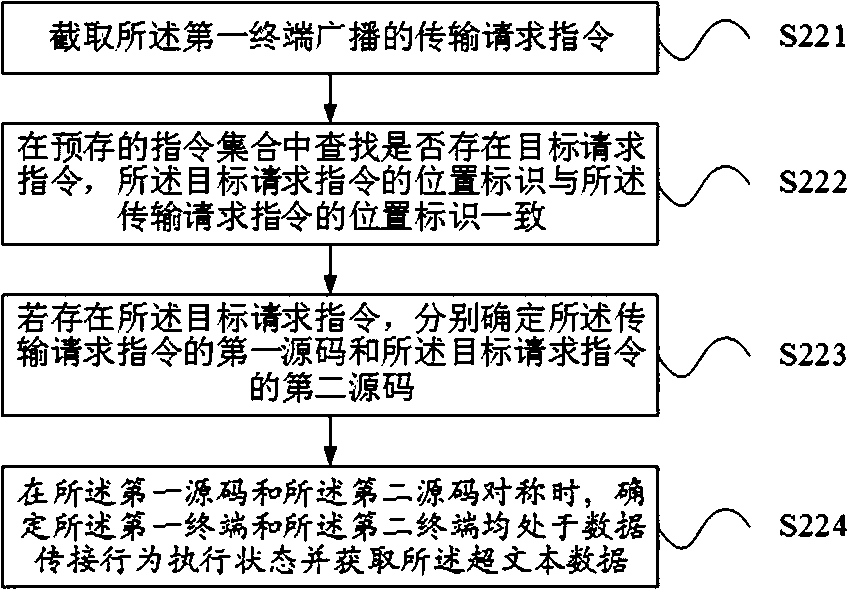
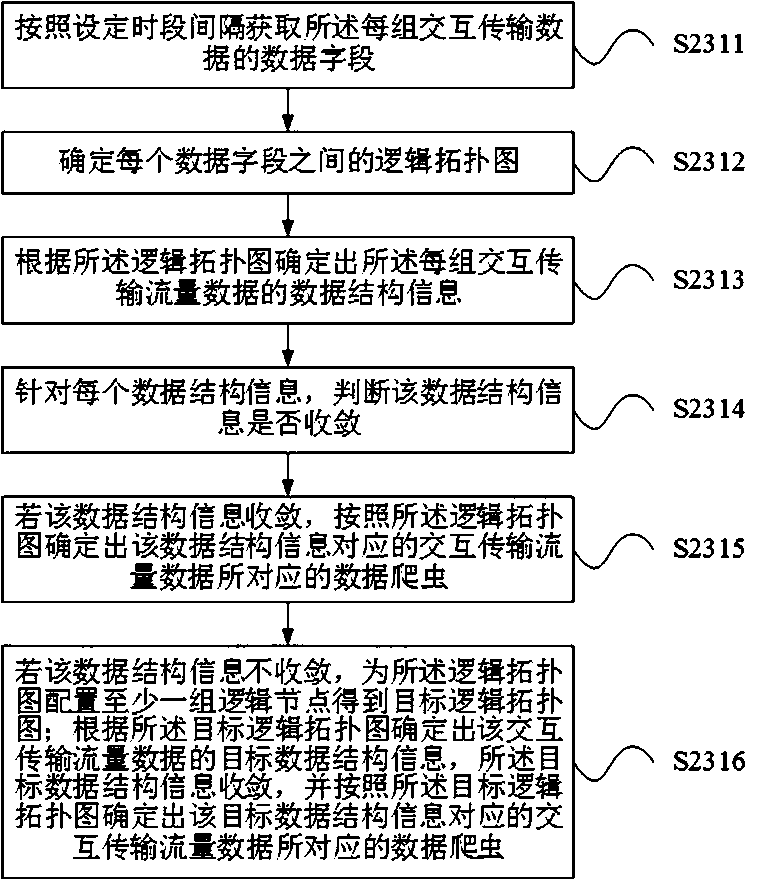
[0080] Exemplary embodiments of the present disclosure will be described in more detail below with reference to the accompanying drawings. Although exemplary embodiments of the present disclosure are shown in the drawings, it should be understood that the present disclosure may be embodied in various forms and should not be limited by the embodiments set forth herein. Rather, these embodiments are provided for more thorough understanding of the present disclosure and to fully convey the scope of the present disclosure to those skilled in the art.
[0081] The inventor found through investigation that most of the common security protection mechanisms provided for data transmission set verification keys at the receiving end / sending end, or encrypt the transmitted data, but these methods are less resistant to attacks and are easily attacked by Trojan horses. Or malicious program cracking, the reliability is poor, and most of these methods are based on the receiving end / data appli...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More