Identity-based digital signature password reverse firewall method
A digital signature and firewall technology, which is applied in the field of information security, can solve the problems of difficult implementation of password reverse firewall technology and high requirements for re-randomization, and achieve the effects of enhancing security, protecting privacy, and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
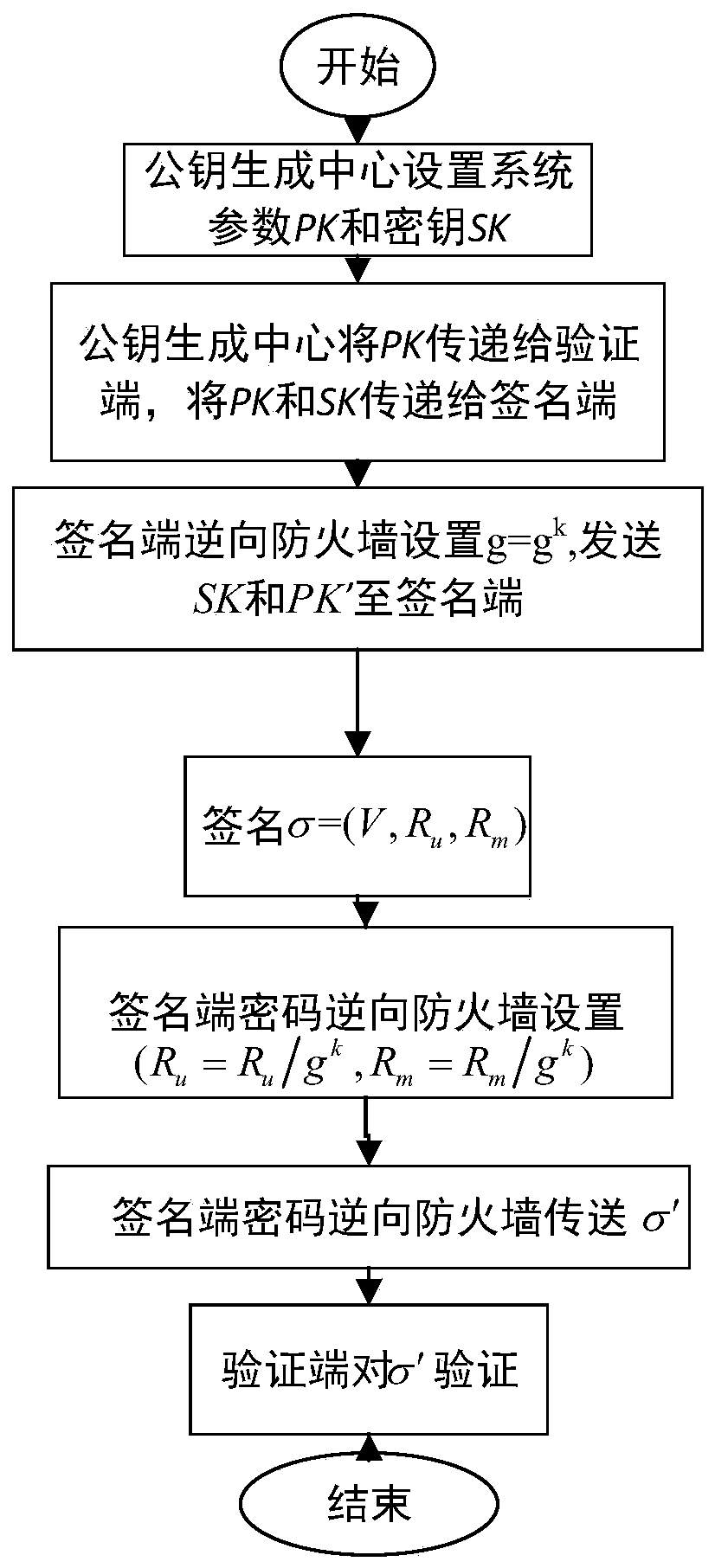
[0037] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the implementation methods and accompanying drawings.
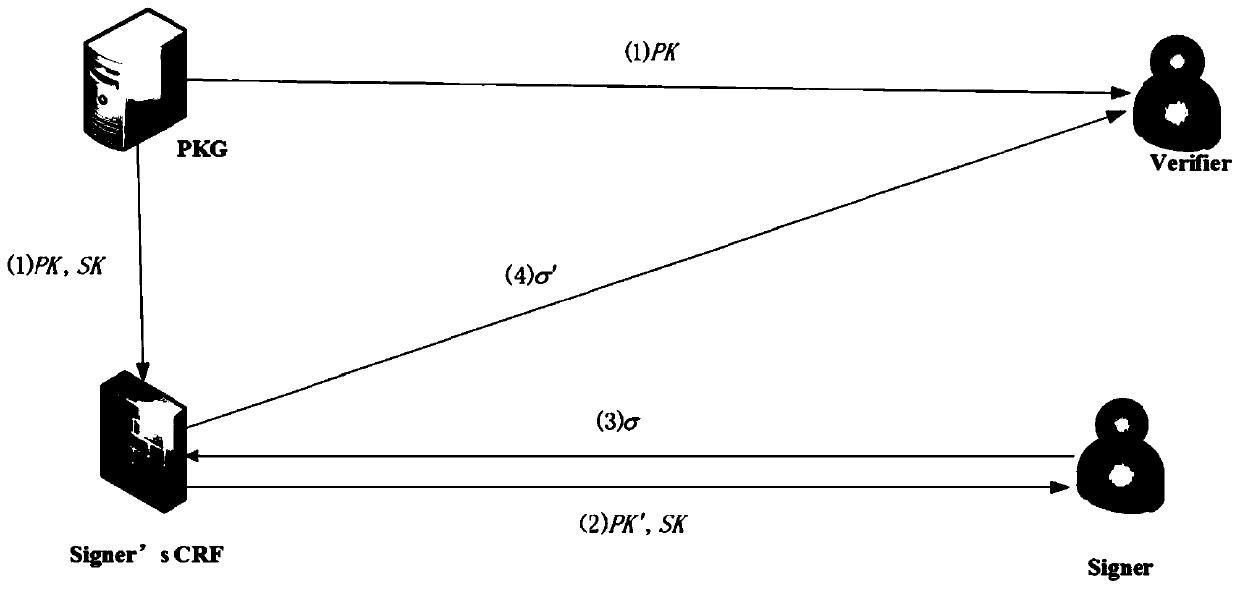
[0038] In 1985, Shamir proposed identity-based encryption (IBE) for the first time, but he did not find an effective and convenient method. Boneh.Dan's follow-up work and identity-based encryption have been successfully implemented and successfully ported to various areas of cryptography, such as identity-based signatures (IBS). The IBS system consists of four parts (Setup, Extract, Sign, Verify). The present invention adopts Paterson and Schuldt in 2006 [Efficient Identity-Based Signatures Secure in the Standard Model. In: Batten L.M., Safavi-Naini R. (eds) Information Security and Privacy. ACISP 2006. LNCS, vol 4058. Springer, Berlin, Heidelberg ], and successfully demonstrated that it satisfies the three basic requirements of a cryp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More